Saurabh Bhargav
Cloud Security and Devops Engineer
New to Contra
Saurabh is building their profile!
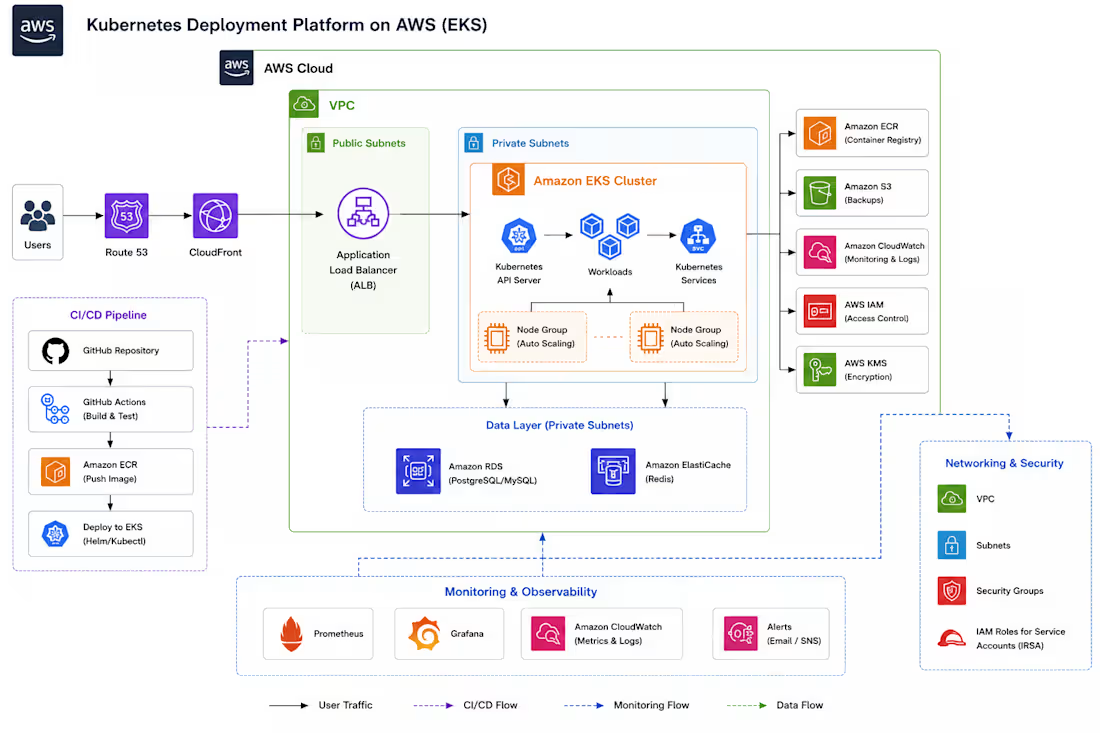
Kubernetes Deployment Platform on AWS (EKS)
Project Overview
Designed and managed a containerized application platform on AWS using Amazon Elastic Kubernetes Service (EKS) to support scalable and reliable application deployments. The platform focused on simplifying Kubernetes-based deployments, improving operational efficiency, and enabling easier management of containerized workloads in AWS cloud environments.
The infrastructure included Kubernetes workloads deployed on EKS, CI/CD automation, container image management, centralized monitoring, and managed AWS services to support production-style application hosting and deployment workflows.
Key Responsibilities
• Deployed and managed Kubernetes workloads on Amazon EKS for containerized applications.
• Configured worker nodes, namespaces, deployments, services, ingress, and autoscaling for application workloads.
• Built CI/CD pipelines using GitHub Actions to automate Docker image build and deployment processes.
• Integrated Amazon ECR for storing and managing container images securely.
• Configured Application Load Balancer (ALB) ingress for external application access and traffic routing.
• Managed containerized applications using Docker and Kubernetes deployment manifests.
• Implemented centralized monitoring and logging using Prometheus, Grafana, and AWS CloudWatch.
• Deployed backend services with Amazon RDS and Redis for application data and caching requirements.
• Worked with IAM roles, security groups, and VPC networking for Kubernetes cluster access and infrastructure communication.
• Improved deployment consistency and scalability through automated Kubernetes deployment workflows.
Technologies & Services Used
Amazon EKS, Kubernetes, Docker, Amazon ECR, GitHub Actions, Application Load Balancer (ALB), Amazon RDS, Redis, AWS CloudWatch, Prometheus, Grafana, IAM, VPC, EC2, Route 53, Bash Scripting
Key Outcomes
• Improved application deployment consistency using Kubernetes orchestration
• Simplified container deployment and scaling workflows
• Reduced manual operational effort through CI/CD automation
• Improved infrastructure visibility with centralized monitoring and logging
• Built scalable cloud-native application deployment workflows on AWS
• Gained operational experience managing Kubernetes workloads in AWS cloud environments
0
8
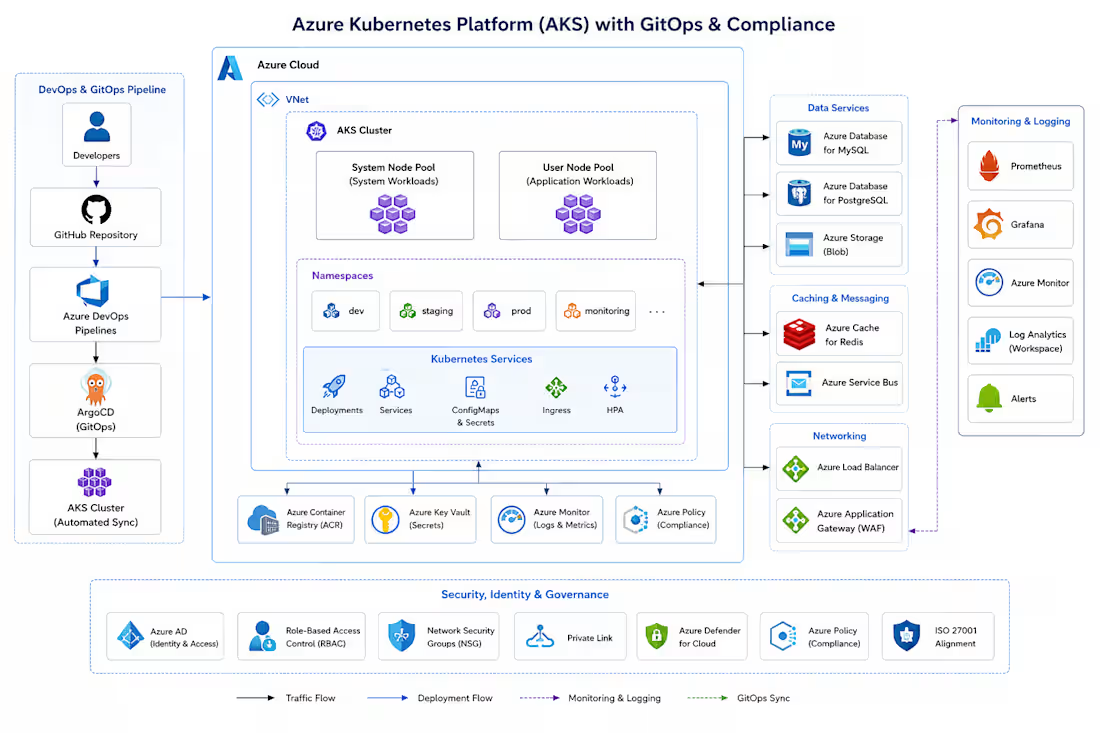
Secure Kubernetes Platform on Azure (AKS) with GitOps & Compliance
Project Overview
Designed and implemented a secure, production-grade Kubernetes platform on Microsoft Azure using Azure Kubernetes Service (AKS) to support scalable and automated application deployments. The platform was built using GitOps principles with ArgoCD to enable consistent, reliable, and automated deployment workflows across multiple environments.
The infrastructure focused on security, operational visibility, compliance alignment, and deployment reliability by integrating centralized monitoring, secure networking, identity management, and automated CI/CD pipelines. The platform was designed to support modern cloud-native workloads while aligning with ISO 27001 and security best practices.
Key Responsibilities
• Designed and deployed a production-ready AKS cluster architecture with secure networking, namespace isolation, and scalable node pool configuration.
• Implemented GitOps-based deployment workflows using ArgoCD to automate application synchronization, configuration management, and continuous delivery processes.
• Built and managed CI/CD pipelines using Azure DevOps and GitHub integration for automated build, validation, and deployment workflows.
• Configured Azure Container Registry (ACR) for secure container image storage and integration with Kubernetes deployment pipelines.
• Implemented secure identity and access management using Azure Active Directory (Azure AD), RBAC policies, and least-privilege access controls.
• Designed secure secrets and configuration management workflows using Azure Key Vault integration for Kubernetes applications and infrastructure components.
• Configured ingress and traffic management using Azure Application Gateway and Kubernetes ingress controllers for secure external application access.
• Deployed managed services including Azure Database for MySQL, PostgreSQL, Redis Cache, Azure Blob Storage, and Azure Service Bus to support scalable application workloads.
• Implemented centralized monitoring, logging, and observability using Prometheus, Grafana, Azure Monitor, Log Analytics Workspace, and alerting mechanisms.
• Applied Azure Policy, NSGs, private networking, and security controls to strengthen compliance posture and reduce infrastructure exposure.
• Improved operational reliability and deployment consistency by automating Kubernetes deployment and infrastructure management processes.
Security & Compliance Focus
• GitOps-driven deployment consistency
• Kubernetes RBAC and access control
• Azure AD identity integration
• Secure secrets management using Azure Key Vault
• Centralized monitoring and logging
• Private networking and NSG security controls
• ISO 27001 aligned operational practices
• Compliance-focused governance and policy enforcement
Technologies & Services Used
Azure Kubernetes Service (AKS), ArgoCD, Azure DevOps, GitHub, Azure Container Registry (ACR), Azure AD, Azure Key Vault, Azure Monitor, Log Analytics Workspace, Prometheus, Grafana, Azure Application Gateway, Redis Cache for Azure, Azure Database for MySQL, PostgreSQL, Azure Blob Storage, Azure Service Bus, NSG, RBAC, Docker, Kubernetes, Helm, Bash Scripting
Key Outcomes
• Improved deployment reliability and operational consistency through GitOps automation
• Strengthened Kubernetes security and governance using RBAC, Azure Policy, and private networking
• Enhanced monitoring and observability for production workloads
• Reduced manual deployment effort through CI/CD and infrastructure automation
• Built scalable and secure Kubernetes infrastructure aligned with modern cloud-native best practices
• Improved compliance readiness through centralized governance, logging, and security controls
0
7
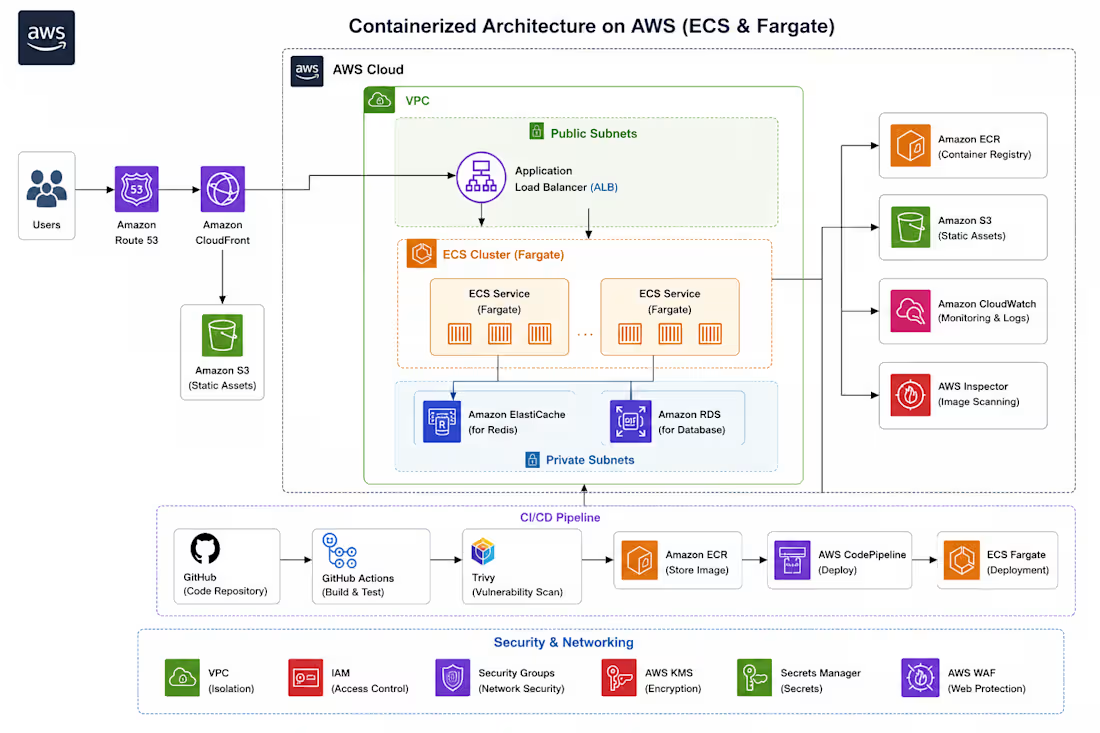
Containerized Architecture on AWS (ECS & Fargate)
Project Overview
Designed and implemented a scalable containerized application architecture on AWS using ECS Fargate to modernize application deployment workflows, improve operational efficiency, and reduce infrastructure management overhead. The platform was built to support secure, highly available, and production-ready application deployments using managed container orchestration services and automated CI/CD pipelines.
The architecture leveraged Docker-based containerization, serverless container management with ECS Fargate, centralized monitoring, automated image scanning, and secure traffic routing to improve deployment consistency, scalability, and application reliability.
Key Responsibilities
• Designed and deployed containerized workloads using Docker and Amazon ECS Fargate for scalable and serverless application hosting.
• Configured Application Load Balancer (ALB) to securely distribute incoming traffic across ECS services and improve application availability.
• Integrated Amazon ECR for centralized container image storage and secure image management.
• Built CI/CD pipelines using GitHub Actions and AWS CodePipeline to automate build, test, vulnerability scanning, and deployment workflows.
• Implemented container image security scanning using Trivy and AWS Inspector before deployment to identify vulnerabilities and improve container security posture.
• Configured CloudFront and Amazon S3 for efficient delivery of static assets and improved application performance.
• Implemented centralized monitoring, logging, and operational visibility using AWS CloudWatch and alerting mechanisms.
• Designed secure networking and access controls using VPC architecture, IAM policies, and security best practices.
• Improved deployment consistency and release reliability by standardizing container-based workflows and automation practices.
• Reduced operational overhead by eliminating manual server management and leveraging fully managed AWS container services.
Security & Operational Focus
• Secure container image management
• Automated vulnerability scanning
• IAM least-privilege access control
• Centralized monitoring and logging
• Secure deployment automation
• Scalable and fault-tolerant application architecture
• Reduced infrastructure management complexity
Technologies & Services Used
Amazon ECS Fargate, Docker, Amazon ECR, Application Load Balancer (ALB), Amazon S3, CloudFront, GitHub Actions, AWS CodePipeline, AWS CloudWatch, AWS Inspector, Trivy, IAM, VPC, Route 53, Bash Scripting
Key Outcomes
• Improved application scalability and deployment reliability
• Reduced EC2 infrastructure management and operational overhead
• Accelerated deployment workflows through CI/CD automation
• Enhanced container security through automated image scanning
• Improved application availability and performance using managed AWS services
• Standardized and streamlined container deployment processes for production workloads
0
18
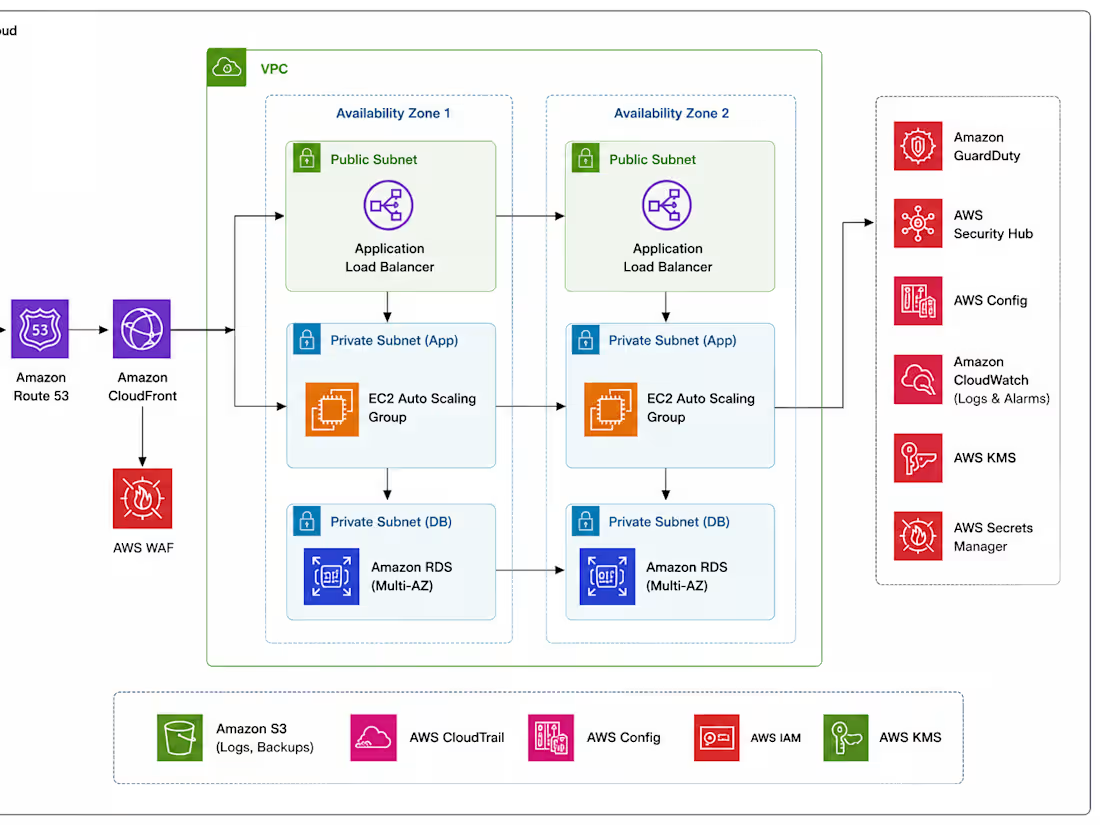
AWS Cloud Architecture, Security & SOC 2 Compliance
Designed and implemented a secure, scalable, and highly available AWS cloud architecture for production-grade applications with a strong focus on cloud security, operational reliability, compliance alignment, and infrastructure optimization. The environment was architected using multi-tier networking with public and private subnets, centralized security controls, monitoring, and automated deployment workflows.
The architecture was designed to align with SOC 2 security principles and industry best practices by implementing least-privilege access controls, continuous monitoring, centralized logging, and secure secrets management.
Key Responsibilities
• Designed a production-grade AWS architecture using VPC, public/private subnets, security groups, and multi-AZ deployment strategies for high availability and fault tolerance.
• Configured Route 53, CloudFront, and Application Load Balancer (ALB) to provide secure traffic routing, low-latency content delivery, and scalable application access.
• Implemented AWS WAF to protect applications from SQL injection (SQLi), XSS attacks, bot traffic, and unauthorized access attempts.
• Built and managed scalable EC2 infrastructure with Auto Scaling Groups to improve application availability and optimize resource utilization.
• Designed secure database architecture using Amazon RDS deployed in private subnets with restricted access and high availability configuration.
• Applied IAM least-privilege policies across services and users, significantly reducing unnecessary permissions and improving overall cloud security posture.
• Integrated AWS GuardDuty, Security Hub, AWS Config, and CloudTrail to provide continuous security monitoring, compliance tracking, auditing, and threat detection.
• Configured centralized monitoring, alerting, and operational visibility using AWS CloudWatch for logs, metrics, alarms, and infrastructure health monitoring.
• Implemented secure secrets management using AWS Secrets Manager and Parameter Store to eliminate hardcoded credentials and improve security practices.
• Managed encryption and key protection using AWS KMS for secure handling of sensitive application and infrastructure data.
• Automated deployment and operational workflows using CI/CD pipelines, infrastructure automation practices, and scripting.
• Optimized infrastructure design and resource utilization, reducing overall cloud operational costs while improving scalability and reliability.
Security & Compliance Focus
• SOC 2 aligned cloud security practices
• IAM hardening and least-privilege implementation
• Infrastructure monitoring and centralized logging
• Threat detection and vulnerability monitoring
• Encryption and secrets management
• Web application protection using AWS WAF
• Compliance-focused operational procedures and documentation
Technologies & Services Used
AWS VPC, EC2, Auto Scaling Group, Application Load Balancer, Route 53, CloudFront, Amazon RDS, AWS WAF, IAM, GuardDuty, Security Hub, AWS Config, CloudTrail, CloudWatch, AWS KMS, Secrets Manager, Systems Manager Parameter Store, S3, GitHub Actions, Terraform, Bash Scripting
Key Outcomes
• Improved infrastructure scalability and reliability for production workloads
• Enhanced cloud security posture through centralized monitoring and access controls
• Reduced manual operational effort through automation and monitoring integrations
• Improved incident visibility and response capability
• Achieved significant cloud cost optimization through infrastructure rightsizing and optimization strategies
• Built a secure and maintainable cloud environment aligned with modern compliance and operational best practices
1
32