Penetration Testing & Cybersecurity Services for Your BusinessDragos Moruz
Penetration testing services aligned with OWASP Top 10 standards to identify and mitigate vulnerabilities in web apps, mobile apps, APIs, and IT infrastructure. My testing approach uncovers critical risks, including misconfigurations to strengthen your security posture.
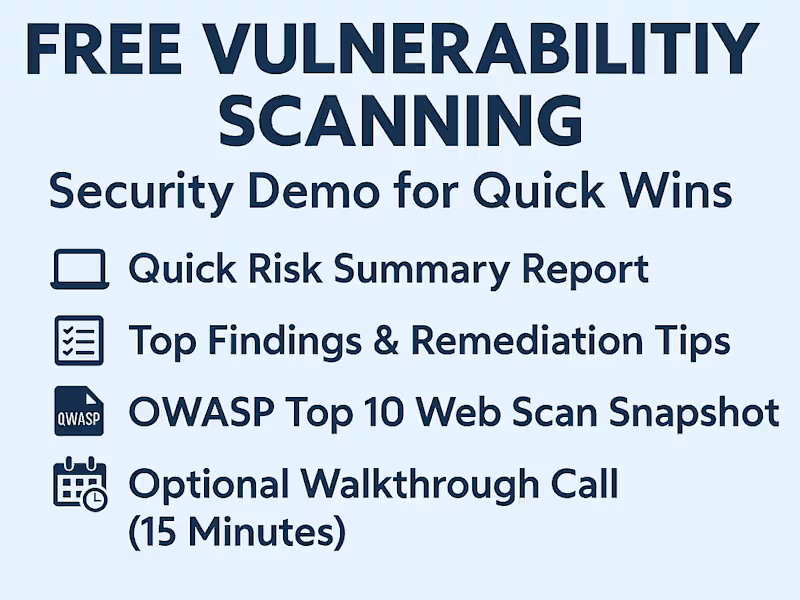
What's included
Expert Penetration Testing & Cybersecurity Services to Secure Your Business
Penetration testing services aligned with OWASP Top 10 standards to identify and mitigate vulnerabilities in web apps, mobile apps, APIs, and IT infrastructure. My testing approach uncovers critical risks, including misconfigurations to strengthen your security posture.
Web Application Testing
Detect OWASP Top 10 vulnerabilities like SQL Injection, XSS, and Broken Authentication.
Assess logic flaws, session handling, and input validation.
Mobile Application Testing
Analyze data encryption, API calls, and test for reverse engineering risks.
Evaluate insecure data transmission vulnerabilities.
API Security Testing
Review authentication, authorization, and data exposure for REST and SOAP APIs.
Test rate-limiting, security headers, and input validation.
Infrastructure Testing
Perform network scans, port analysis, and firewall rule reviews.
Assess VPNs and intrusion detection systems for weaknesses.
Deliverables
Comprehensive Reports with risks, vulnerabilities, and proofs of concept.
Remediation Plans with actionable fixes.
Compliance Mapping (OWASP, CIS, NIST).
Retesting Support to validate fixes.
Perfect for businesses seeking secure and compliant applications!
FAQs
Contact for pricing
Tags
Burp Suite
Chainlink
Docker
Oracle APEX
Solidity
Cybersecurity Specialist
Security Engineer
Security Manager
Service provided by
Dragos Moruz Timișoara, Romania
- 5.00
- Rating
- 4
- Followers

Penetration Testing & Cybersecurity Services for Your BusinessDragos Moruz
Contact for pricing
Tags
Burp Suite
Chainlink
Docker
Oracle APEX
Solidity
Cybersecurity Specialist
Security Engineer
Security Manager
Penetration testing services aligned with OWASP Top 10 standards to identify and mitigate vulnerabilities in web apps, mobile apps, APIs, and IT infrastructure. My testing approach uncovers critical risks, including misconfigurations to strengthen your security posture.
What's included
Expert Penetration Testing & Cybersecurity Services to Secure Your Business
Penetration testing services aligned with OWASP Top 10 standards to identify and mitigate vulnerabilities in web apps, mobile apps, APIs, and IT infrastructure. My testing approach uncovers critical risks, including misconfigurations to strengthen your security posture.
Web Application Testing
Detect OWASP Top 10 vulnerabilities like SQL Injection, XSS, and Broken Authentication.
Assess logic flaws, session handling, and input validation.
Mobile Application Testing
Analyze data encryption, API calls, and test for reverse engineering risks.
Evaluate insecure data transmission vulnerabilities.
API Security Testing
Review authentication, authorization, and data exposure for REST and SOAP APIs.
Test rate-limiting, security headers, and input validation.
Infrastructure Testing
Perform network scans, port analysis, and firewall rule reviews.
Assess VPNs and intrusion detection systems for weaknesses.
Deliverables
Comprehensive Reports with risks, vulnerabilities, and proofs of concept.
Remediation Plans with actionable fixes.
Compliance Mapping (OWASP, CIS, NIST).
Retesting Support to validate fixes.
Perfect for businesses seeking secure and compliant applications!
FAQs
Contact for pricing