Multi-Tenant SaaS Platform on AWS EKS
This repository contains a complete infrastructure and application codebase for a production-ready multi-tenant SaaS platform built on AWS EKS. The platform features automated CI/CD, comprehensive monitoring, security-first design, and cost optimization.
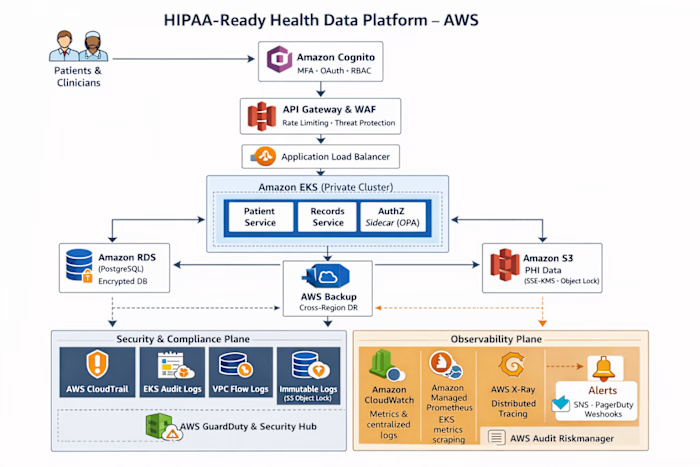
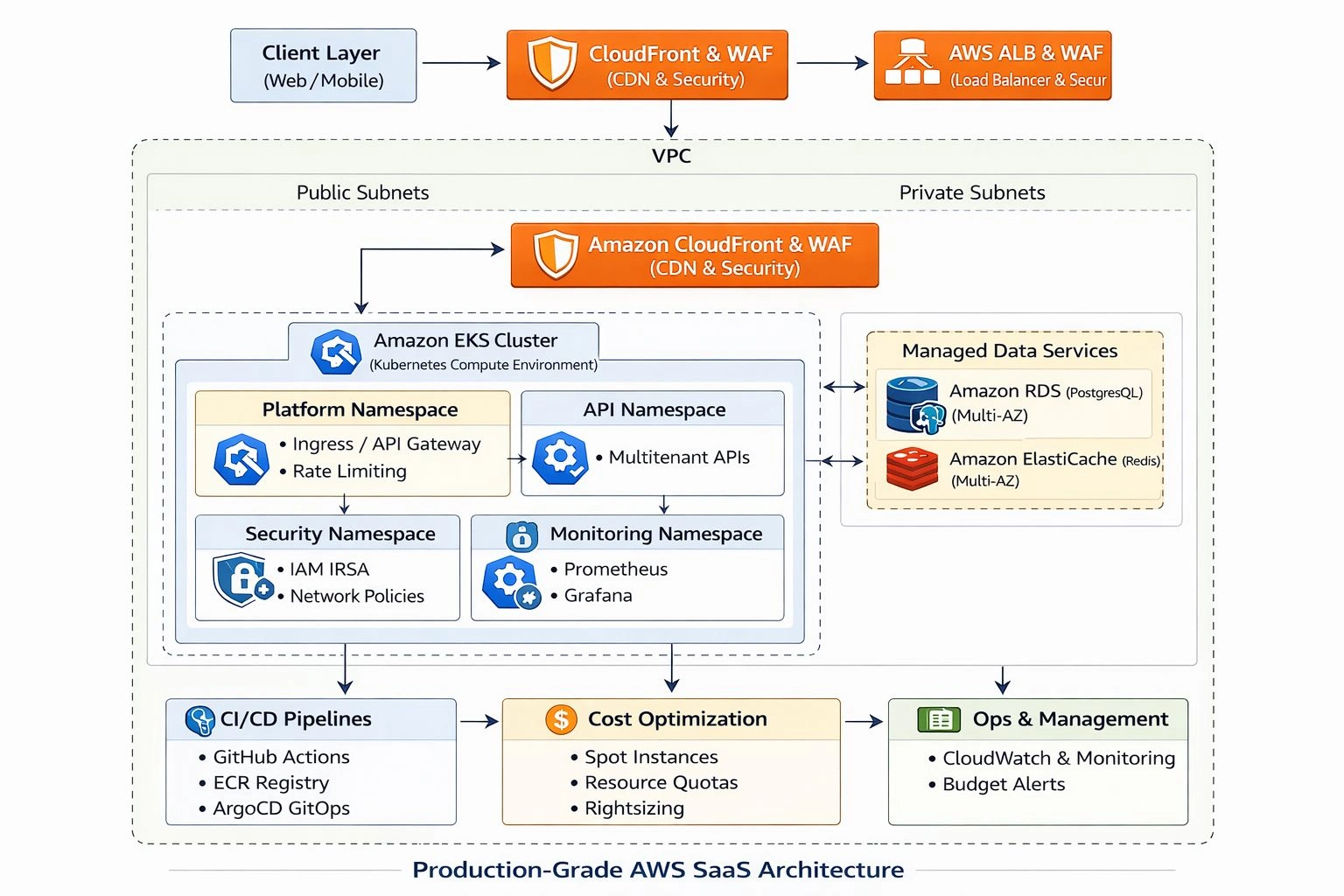
Architecture Overview
The platform follows a cloud-native, microservices-based architecture with:
Application Layer: Go-based multi-tenant API with JWT authentication
Infrastructure: AWS EKS with managed node groups
Database: RDS PostgreSQL with Multi-AZ (external to EKS)
Cache: ElastiCache Redis for session and rate limiting
Load Balancer: Application Load Balancer with WAF
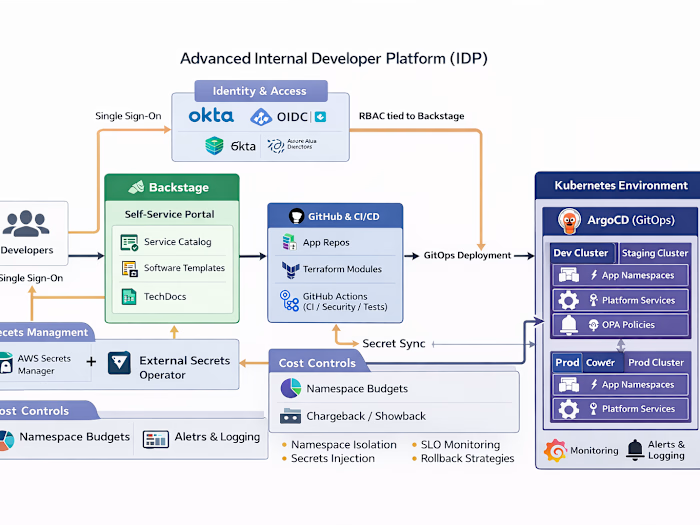
CI/CD: GitHub Actions with security scanning and ArgoCD GitOps
Monitoring: Prometheus, Grafana, and Loki for observability
Security: IRSA, Secrets Manager, and network policies
Project Structure
api/ - Go-based multi-tenant API applicationapplication/ - Core application codeinfrastructure/terraform/ - Terraform configurations for AWS infrastructuremodules/vpc/ - VPC module with private/public subnetsmodules/eks/ - EKS cluster module with node groupsenvs/dev/ - Development environment configurationenvs/staging/ - Staging environment configurationenvs/prod/ - Production environment configurationinfrastructure/kubernetes/ - Kubernetes manifestsinfrastructure/aws/ - AWS-specific configurationskubernetes/ - ArgoCD app-of-apps manifests.github/workflows/ - GitHub Actions CI/CD pipelinesblue-green-deploy/ - Blue/green and canary deployment configurationscost-controls/ - Cost optimization and budget managementdocumentation/ - Architecture and security documentationrunbooks/ - Operational runbooks for deployment, scaling, and outage managementsecurity/ - Security configurations and policieshorizontal-scaling/ - Horizontal scaling configurations and load testingalerts/ - Alerting and monitoring configurationsmetrics/ - Metrics and observability configurationsfailure-scenarios/ - Failure scenario documentation and runbooksCI/CD Pipeline
This project uses GitHub Actions for continuous integration and deployment. The pipeline includes the following stages:
Lint - Validates Terraform, YAML, shell script, and Go code
Unit Tests - Runs Go unit tests and Terraform validation
Docker Build - Builds the application Docker image with multi-stage build
Trivy Scan - Performs security scanning for vulnerabilities in code and container images
Push to ECR - Pushes the Docker image to Amazon ECR (only on main branch)
Deploy via ArgoCD - GitOps deployment to EKS cluster
Pipeline Details
The workflow in
.github/workflows/ci-cd-pipeline.yml includes:Terraform formatting and validation
Go application testing
Docker image building with security scanning
Vulnerability scanning with Trivy
Image pushing to ECR with proper tagging
Security gates to prevent deployment of vulnerable images
Required Secrets
To use this pipeline, you need to configure the following secrets in your GitHub repository:
AWS_ACCESS_KEY_ID - AWS access key IDAWS_SECRET_ACCESS_KEY - AWS secret access keyAWS_ACCOUNT_ID - AWS account IDAWS_REGION - AWS region (default: us-east-1)Additionally, for ArgoCD deployment, you'll need:
ArgoCD server access credentials
EKS cluster access configuration
Deployment Process
Prerequisites
AWS account with appropriate permissions
EKS cluster with required components
ArgoCD installed in the target cluster
Proper AWS credentials configured
Docker installed for local builds
kubectl configured for cluster access
Multi-Environment Deployment
The platform supports three environments:
Development: Lightweight configuration for development and testing
Staging: Medium-sized configuration for pre-production validation
Production: High-availability configuration for production workloads
Each environment has separate Terraform state files and appropriate resource sizing. Each environment includes:
VPC with private and public subnets
EKS cluster with on-demand and spot node groups
RDS PostgreSQL database with appropriate sizing
Redis ElastiCache for caching and rate limiting
Infrastructure Deployment Steps
Configure AWS Credentials: Set up AWS credentials with appropriate permissions
Infrastructure Setup: Deploy infrastructure using Terraform
Configure kubectl: Get the EKS cluster configuration
ArgoCD Bootstrap: Deploy ArgoCD and application manifests
CI/CD Pipeline: Code changes automatically trigger builds and deployments
Application Deployment via ArgoCD
The platform uses ArgoCD for GitOps deployment with the following components:
Application manifests in the
kubernetes/ directoryEnvironment-specific overlays in
kubernetes/overlays/App-of-apps pattern for centralized management
Database Initialization
The platform provisions PostgreSQL RDS databases for each environment with:
Secure connection parameters stored in Kubernetes secrets
Multi-AZ configuration for staging and production
Appropriate backup retention policies
Database credentials managed through Terraform variables
Monitoring and Observability Setup
After infrastructure deployment:
Prometheus and Grafana are deployed via Kubernetes manifests
Loki/Promtail for log aggregation
Pre-configured dashboards for application and infrastructure metrics
AlertManager with SLO-based alerting
Cost Controls Implementation
The platform includes comprehensive cost controls:
Spot instances for up to 90% compute cost savings
Resource quotas to prevent over-provisioning
Budget alerts via AWS Budgets
Rightsizing with VPA for optimal resource usage
GitOps with ArgoCD
The platform uses an App-of-Apps pattern where:
Root application manages child applications
Each service deployed as separate ArgoCD application
Continuous synchronization between Git and cluster state
Automated health assessment of deployed applications
Security Features
Authentication: JWT-based with tenant isolation
Infrastructure Security: IAM Roles for Service Accounts (IRSA)
Network Security: Network policies and pod security standards
Secrets Management: AWS Secrets Manager
WAF Protection: Web Application Firewall rules
Image Security: Trivy scanning in CI/CD pipeline
Cost Optimization
Spot Instances: Up to 90% cost savings with graceful interruption handling
Rightsizing: VPA and resource quotas to prevent over-provisioning
Budget Management: AWS Budgets with proactive notifications
Horizontal Scaling: CPU and latency-based scaling to match demand
Monitoring and Observability
Metrics: Prometheus with RED metrics (Rate, Error, Duration)
Visualization: Grafana dashboards
Logging: Loki for structured log aggregation
Alerting: SLO-based alerts with proper escalation
Operational Runbooks
The platform includes comprehensive runbooks for:
Deployment procedures
Scaling operations
Outage response
Rollback procedures
See the
runbooks/ directory for detailed operational procedures.Local Development
To build and run the application locally:
Security Guidelines
This project follows security best practices to protect sensitive information:
🔒 No Hardcoded Secrets: All sensitive values are managed through variables and secrets managers
🔒 Secure Credential Handling: Database passwords and other secrets are passed via variables at runtime
🔒 Proper .gitignore: All .tfvars and credential files are excluded from Git commits
🔒 Environment Variables: Use TF_VAR_* environment variables for sensitive inputs
🔒 Secrets Management: Integrate with AWS Secrets Manager or other vault solutions for production
⚠️ Important: Never commit actual passwords, API keys, or other secrets to the repository. Always use secure methods to provide these values during deployment.
Project Readiness for Deployment
The project is fully configured and ready for deployment with the following key features:
✅ Complete Infrastructure as Code: All infrastructure components defined in Terraform modules
✅ Multi-Environment Support: Dev, staging, and production environments with appropriate sizing
✅ Managed Database Service: RDS PostgreSQL configured for each environment
✅ CI/CD Pipeline: Complete GitHub Actions workflow with security scanning
✅ GitOps Deployment: ArgoCD app-of-apps pattern for automated deployments
✅ Security Controls: IRSA, network policies, and secrets management
✅ Monitoring Stack: Prometheus, Grafana, and Loki for full observability
✅ Cost Optimization: Spot instances, resource quotas, and budget alerts
✅ Operational Runbooks: Comprehensive procedures for deployment, scaling, and incident response
✅ Scalability: Auto-scaling configured for both application pods and cluster nodes
Usage
The pipeline will automatically trigger on pushes to the main branch and on pull requests. For manual deployments, follow the infrastructure deployment steps outlined above. After infrastructure deployment, applications are deployed via ArgoCD GitOps.
Like this project
Posted Apr 7, 2026
Built a multi-tenant SaaS platform with CI/CD on AWS EKS.