MalX: Vulnerability Testing
Developing and Implementing MalX
MalX is a platform built to create, manage, and distribute vulnerability tests written in Python. The tests are written by a team of security experts and each test is annotated by vulnerability classes as defined by The MITRE Corporation. Clients can download executable tests that they can run on their respective platforms and assess the security of their devices.
Product Overview
Malx UI
MaIX UI is the primary consumer-facing platform that provides the user's access to the content along with executable files. The administrators and content creators can use the same platform to write, modify, and debug their vulnerability tests.
Executable Compiler
Whenever a test or created or updated, a robust system is invoked in parallel to the main thread (using Celery and Docker) that invokes a docker container of the relevant platform with Python and PyInstaller libraries pre-installed. The compilation commands are initiated in the said container and the output file is saved in a storage point shared between all containers.
Using docker allows the product to be compatible across multiple platforms. The system works regardless of which operating system it is deployed in.
Role and Responsibilities
Provided The PC Security Channel with all the necessary architecture, design, development, and testing capacity to build MalX from scratch.
A robust system built in-house through close collaboration with The PC Security Channel team. Currently, the product is in an MVP state and its beta testing is underway.
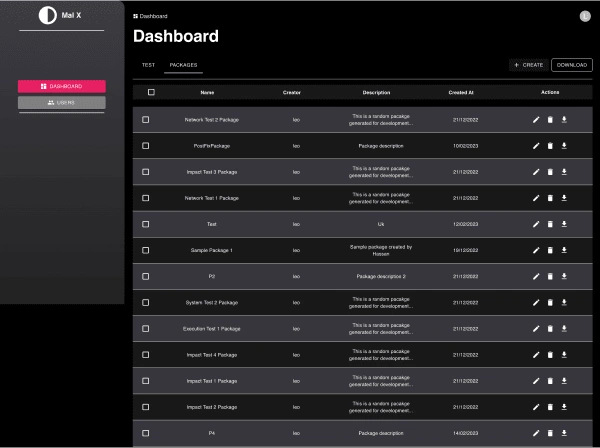
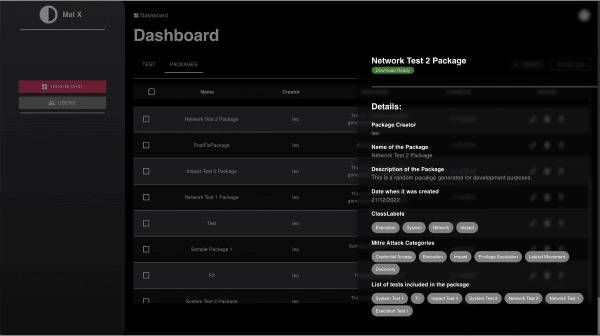
MalX Dashboard
some screens from the Web App that I implemented.
Dashboard- Test
Allows users to browse available tests and download them. Admins can edit and create tests for their subscribers.
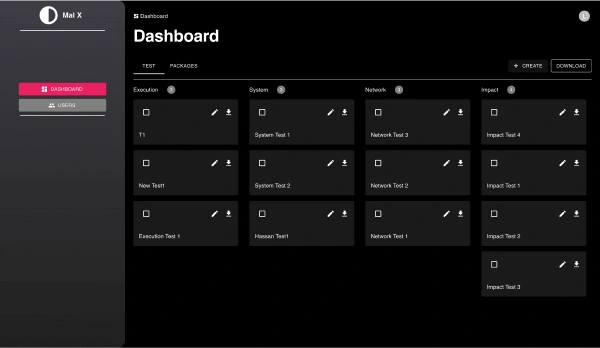
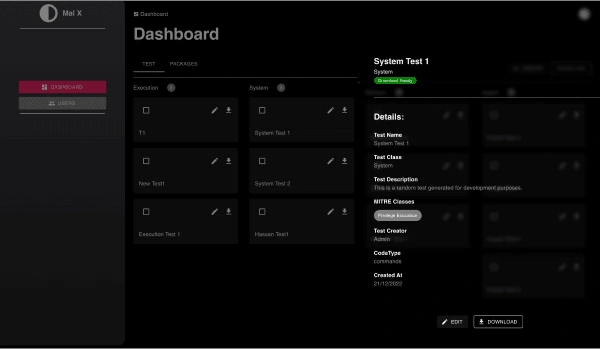
Test Details Drawer
Test Details Drawers show the basic information of the test along with UI indicators for the availability of the downloadable executable file.
Packages List
Allows user to browse packages (Pre-Compiled combination of multiple tests) and download their executable if needed. Admins can edit and create packages from this screen.
Package Details Drawer
Package Details Drawers show the basic information of the test along with UI indicators for the availability of the downloadable executable file.
RESt API Documentation
An auto-generated documentation that thoroughly describes the URL structure of the MalX API. The documentation is generated by drf-yasg library and also includes data definitions.

Technology Stack
Frontend
Node JS
React JS
Base framework for the entire frontend systel
Context API
Module-level state management
SWR by vercel
Caching and mutating data served by the backend
Material UI
Frontend UI libraries used for the website cor
Yarn Package Manager
For live robust testing and debugging
Jest Test Runner
Resumable file uploads
Docker and Docker Compose
For development and production pipelines
Backend
Python
Django
Django Rest Framework
For REST APIS
DRF-yasg
For automatically generated REST API documentation
Celery and Celery Beat
For parallel/threaded tasks, task scheduling, and task management
Redis Queue
Messaging queue service for Celery worker nodes
Traefik
For HTTPS reverse proxies on development computers
Jupyter Notebook
For live robust testing and debugging
Docker and Docker Compose
For development and production pipelines
Make and Makefile
For automating setup, testing, and deployment routines
Like this project
Posted Feb 22, 2024
MaIX is a platform built to create, manage, and distribute vulnerability tests written in Python.