How should I describe my project clearly to a freelance security manager on Contra?
Start by explaining what your business does and what you need help with. Make sure to talk about the parts of your project that need security measures. Be clear about your goals and what you hope the freelance security manager will do. This helps the freelancer understand your needs.
What key factors should I consider when evaluating the profiles of security managers on Contra?
Look for freelancers with a strong background in cybersecurity. Check for certifications, past projects, and feedback from other clients. It's important to find someone who has experience with the specific security challenges you face. Also, make sure they have good communication skills to help explain things to you.
How can I set clear expectations for the deliverables from a security manager?
Talk with the security manager and agree on what tasks need to be done. Write down everything clearly, like a checklist. Decide on deadlines so you know when you can expect each part to be done. This helps both of you stay on track and understand each other.
What initial steps should I take to successfully onboard a freelance security manager on Contra?
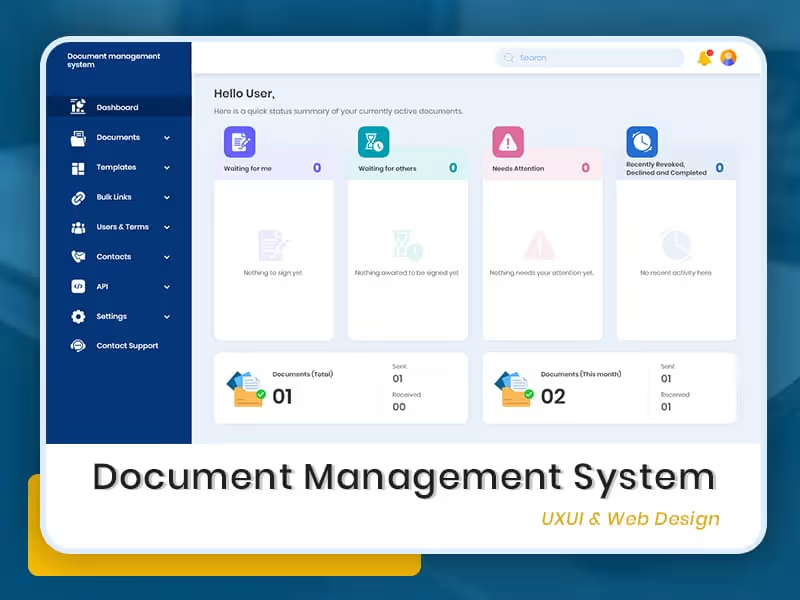
Start by sharing all the needed information about your project and systems. Make sure they have the right access to tools and documents. Set up an introduction meeting to discuss everything and answer any questions they might have. This helps them understand your needs and get started quickly.
How do I ensure effective communication throughout the project with a freelance security manager?
Set up regular check-ins, like weekly calls or email updates. Agree on the best way to communicate, like using email or a chat platform. Being clear and responsive helps solve problems quickly and keeps the project moving forward.
How should I review and approve the security manager’s work on Contra?
Go through the deliverables when they’re done and check if they meet your needs. Compare the work to the goals you agreed on at the start. It's also a good idea to ask questions if something isn’t clear. This way, you know the work is done right.
How can I ensure a freelance security manager understands my company's culture and values?
Share information about your company’s mission, values, and work environment. Explain what is important to you and your team. This helps the security manager align their work with your company’s expectations and cultural context.
What should I do to prepare my team for working with a freelance security manager?
Introduce the security manager to your team and explain their role. Make sure everyone knows how to work together and share information. Encourage open communication, so the security manager can easily reach team members when needed.
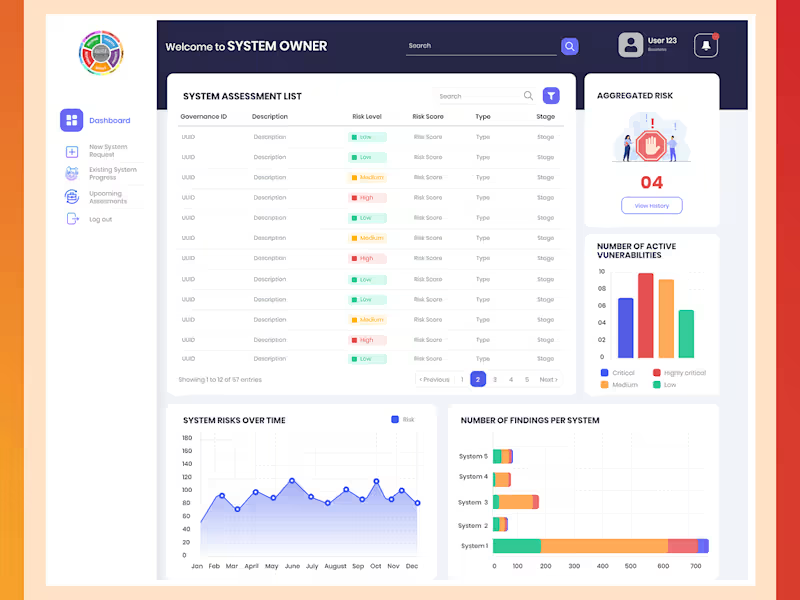
How can I track the progress of the security manager’s work effectively?
Set milestones and deadlines to keep track of the work. Use project management tools to help monitor the tasks. Regular updates from the security manager will help you see if everything is going according to plan.
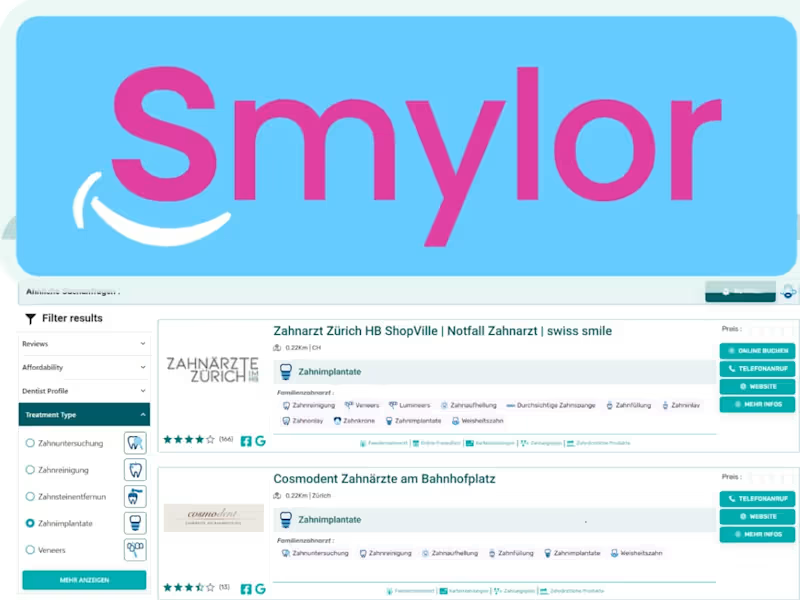
Who is Contra for?
Contra is designed for both freelancers (referred to as "independents") and clients. Freelancers can showcase their work, connect with clients, and manage projects commission-free. Clients can discover and hire top freelance talent for their projects.
What is the vision of Contra?
Contra aims to revolutionize the world of work by providing an all-in-one platform that empowers freelancers and clients to connect and collaborate seamlessly, eliminating traditional barriers and commission fees.