OpenClaw Setup: AI-Driven Automation System for Credit Startup

How I Turned One Windows Machine Into a Full Automation Stack — and Ran a Credit Startup With It
A case study in production-grade OpenClaw deployment, domain-specific workflow engineering, and security architecture.
The Problem I Was Solving
Running a credit startup while maintaining an active automation engineering practice means juggling things that don't naturally overlap: loan pipeline management, content strategy, borrower communications, KPI reporting, code deployments, and client deliverables — simultaneously, with a small team.
I'd built point-to-point automation scripts before. Python + cron, Zapier, Power Automate. The problem with all of them was the same: each solved a single problem in isolation, and the total system became a collection of brittle scripts I had to babysit. There was no unified control plane. No reasoning capability. No way to instruct everything in plain English from my phone when I was away from my desk.
What I actually needed was an agent — something persistent, programmable, and smart enough to adapt when things didn't go as planned. That's what led me to OpenClaw.
What OpenClaw Actually Is
OpenClaw is an open-source, MIT-licensed AI agent framework built on Node.js. It runs as a persistent daemon on your local machine — in my case, Windows 11 — connects to a large language model (I use Claude Sonnet as primary, GPT-4o as fallback), and exposes a natural-language control interface over your existing messaging channels: WhatsApp, Telegram, or Discord.
The key distinction from most automation tools: OpenClaw doesn't just execute scripts. It reasons. You can tell it "summarise what's changed in the loan portfolio this week and flag anything that looks like an early delinquency signal," and it figures out the steps, queries the data, runs the analysis, and sends you a structured report. It handles multi-step tasks, retries on failure, and asks for clarification when instructions are ambiguous.
"You can instruct it from your phone. It runs while you sleep. It remembers context. And unlike a cloud service, you control where all the data lives."
The Architecture
The system is built around three layers:
Control Layer — I send instructions via WhatsApp or Telegram from my phone. Any message I send is routed to the agent in real time.
OpenClaw Gateway — The persistent core running on my Windows machine, bound strictly to localhost. It handles session routing, tool dispatch, and incoming webhook events. The gateway connects to both Claude Sonnet (primary reasoning) and GPT-4o (fallback), and communicates outward through a Cloudflare Zero Trust tunnel — meaning no ports are open to the internet directly.
Domain Workflows — Eight production skills sitting underneath the gateway, each purpose-built for a specific category of work: file management, data pipelines, credit portfolio monitoring, content, customer support, KPIs, and more.
The Workflows I Built
1. Intelligent File & Folder Automation
Files dropped into a designated inbox folder are automatically classified, renamed to a canonical format (YYYY-MM-DD_client_doctype), and routed to the right project directory. A Telegram notification confirms every move. Inbox clears itself within seconds. Zero manual filing.
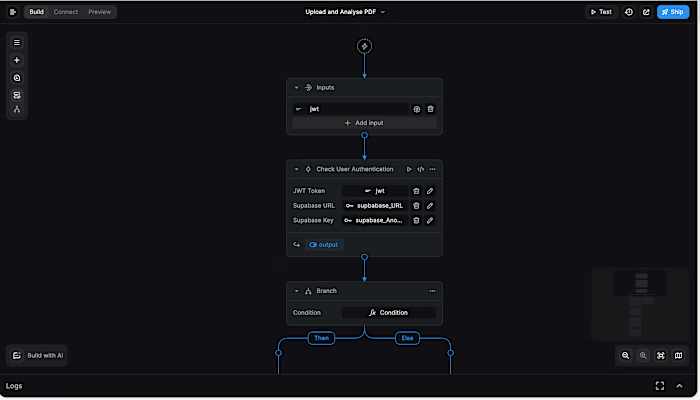
2. API & Webhook-Driven Event Processing
A unified webhook listener handles events from GitHub, payment processors, and monitoring tools — all validated via HMAC signatures before processing. One entry point for all external triggers. When a push hits the main branch, the agent summarises the diff and sends a formatted changelog to the project channel automatically.
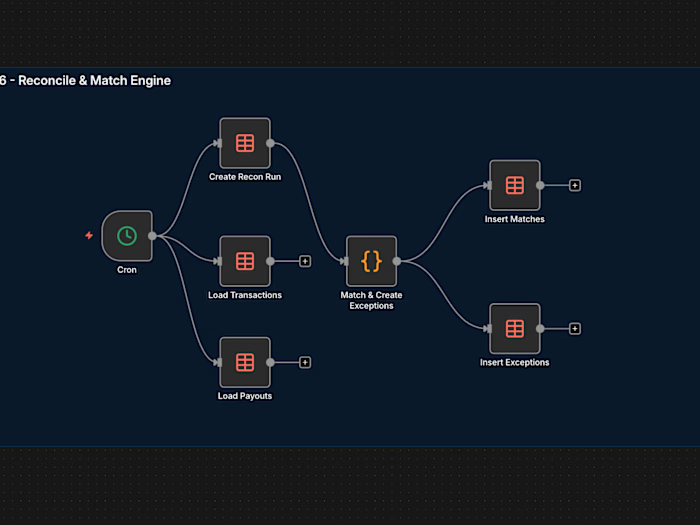
3. Scheduled Pipeline Automation
Six cron-driven jobs run without any human initiation: a morning briefing at 7 AM, a weekly portfolio digest every Monday, a daily KPI snapshot, a nightly audit log review, a Sunday content queue check, and a monthly archive job. Everything unattended.
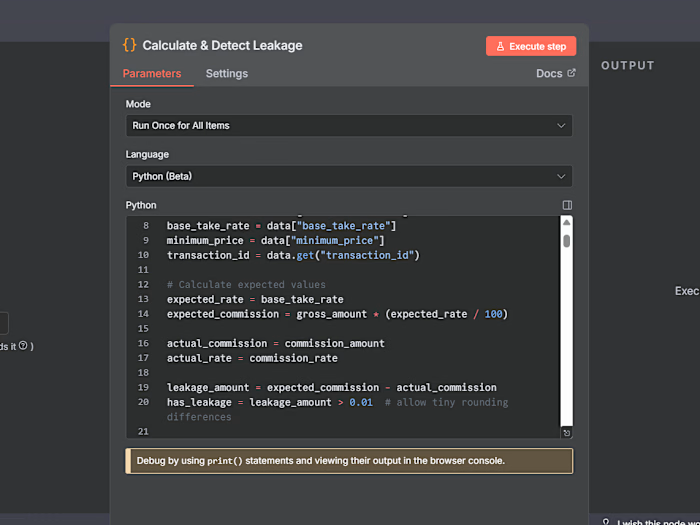
4. ETL Data Processing
Partner data exports arrive in inconsistent formats — different column names, date formats, currency representations. Rather than maintaining brittle regex parsers, the LLM handles normalisation with a "flag if unsure" fallback. What used to be a 2-hour weekly manual task runs automatically, delivering a clean, merged operational dataset with anomalies surfaced for review.
5. Credit Portfolio Management
Daily monitoring of delinquency rates across 30/60/90-day buckets, prepayment speeds, and per-borrower risk score deltas. When a borrower crosses an early-warning threshold — payments late by more than 20 days, two missed payments, or a risk score drop of 15+ points — the agent drafts a contextually appropriate outreach message. I review and approve before it sends. Nothing goes out automatically.
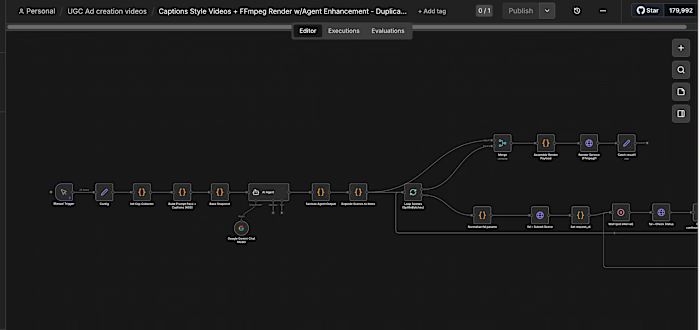
6. Content Creation & Distribution Pipeline
I drop a voice note or a few bullet points into Telegram. The agent transcribes, expands, and formats the content for the right platform — LinkedIn long-form, Twitter/X thread, or blog outline. Each draft goes into a review queue with an ID. I reply
approve 07 and it schedules via the platform API at optimal posting time. Consistent presence without dedicated content hours.7. KPI Monitoring & Alerting
One unified view across Stripe (MRR), the portfolio database (active loans, delinquency rate), platform analytics (content engagement), and system health (uptime). Threshold breaches trigger an immediate Telegram push with the metric, the delta from last period, and the agent's suggested probable cause and next step.
8. Customer Support Automation
Incoming support queries are classified into three tiers. Tier 0 — FAQ-answerable questions about rates, application status, document checklists — are resolved automatically. Tier 1 — non-trivial queries — get a drafted response for my review before sending. Tier 2 — complaints, disputes, compliance questions — get an immediate escalation alert. About 70% of support volume is now handled without my time. Average first-response time dropped from 6 hours to under 5 minutes for tier-0 queries.
The Security Architecture
OpenClaw has real attack surface — it can execute shell commands, access the filesystem, and call external APIs. Security wasn't something I added at the end. It was designed in from day one.
Secrets management. All credentials live in Windows System Environment Variables. Nothing in config files. Nothing in version control. The credit startup's API keys use a separate isolated env file with its own loader, entirely decoupled from the main agent config.
Gateway hardening. The default OpenClaw configuration binds the gateway to 0.0.0.0 — meaning any device on your local network can reach the control interface. That's a known issue in the project's GitHub tracker. I override it to loopback (127.0.0.1) on day one. External webhook triggers reach the agent through a Cloudflare tunnel that terminates locally — no open ports.
Role-based access control. Channel-level allowlists restrict exactly which Telegram user IDs and WhatsApp numbers can issue instructions. For high-impact skills — anything touching portfolio data, borrower outreach, or financial records — there's an additional layer: the agent echoes back the planned action and waits for an explicit "yes" before executing. That confirm-before-execute pattern has prevented at least three significant mistakes.
Filesystem sandboxing. The agent can only read and write within explicitly allowlisted directories. System paths are denied. Automation subprocesses that need broader access run in constrained PowerShell sessions with restricted execution policies.
Audit logging. Every workflow execution is logged — timestamp, trigger source, skill invoked, parameters, and outcome. A nightly job parses the logs, surfaces anomalies, and sends a digest. 90-day retention. Any failure pattern triggers an immediate alert.
What This Project Taught Me
Security has to be first, not last. OpenClaw's defaults are not production-ready. The gateway binding, webhook validation, filesystem scoping — these need to be addressed before a single workflow runs.
LLM reasoning beats rigid parsing for real-world data. Partner exports are inconsistent. Letting the LLM normalise data with a "flag if uncertain" fallback is dramatically more resilient than maintaining a parser that breaks every time a partner changes their format.
The confirm-before-execute pattern is non-negotiable for high-stakes actions. The friction is worth it. Every time.
Build one workflow, make it bulletproof, then expand. I started with file automation. Only after two weeks of reliable operation did I layer in webhooks. Incremental expansion makes debugging clean and trust in the system high.
Tech Stack
OpenClaw · Node.js 22 LTS · Claude Sonnet 4.6 · GPT-4o · Windows 11 Pro · Telegram Bot API · WhatsApp Web · Cloudflare Zero Trust · PostgreSQL · HMAC-SHA256 · LinkedIn API · Twitter/X API v2 · Stripe API · GitHub Webhooks
Automation Engineer & Founder · ethercess@gmail.com
Like this project
Posted Mar 24, 2026
Built an AI-driven automation system using OpenClaw for a credit startup on Windows 11.
Likes
1
Views
4
Timeline
Feb 24, 2026 - Mar 28, 2026