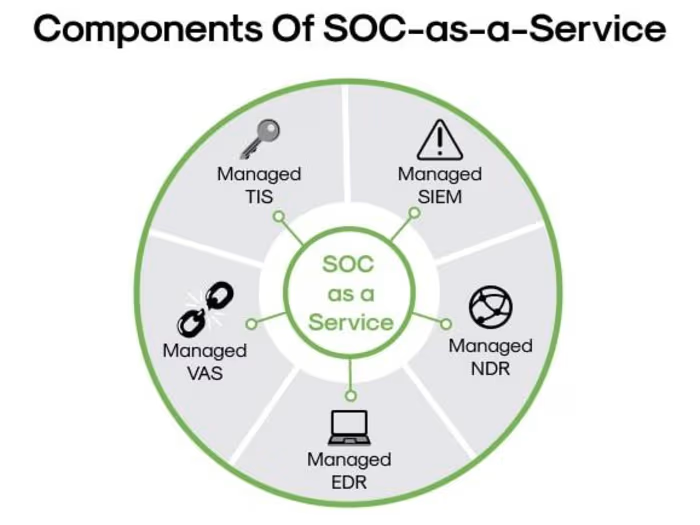
Implementation of Information Security Management System (ISMS)
Project Scope
Assessment & Gap Analysis
Review current security policies, procedures, and practices.
Identify gaps between existing controls and ISO 27001 requirements.
Risk Assessment
Identify and assess security risks to critical information assets.
Prioritize risks based on potential impact and likelihood.
Policy Development
Develop and formalize an ISMS policy, security objectives, and controls.
Align policies with organizational goals and regulatory requirements.
Implementation of Controls
Establish security controls addressing confidentiality, integrity, and availability.
Implement controls for physical, network, and information security.
Training & Awareness
Conduct security awareness training for staff on ISMS policies.
Ensure compliance through ongoing education.
Monitoring & Auditing
Set up continuous monitoring systems to detect and respond to threats.
Conduct internal audits to assess compliance and control effectiveness.
Incident Response & Improvement
Develop incident management and response plans.
Regularly review and improve the ISMS for ongoing protection.
Timeline:
6-12 months (depending on organization size)
Deliverables
ISMS policies and procedures
Risk assessment report
Training materials
Incident response plan
ISO 27001 audit readiness
Success Criteria
Achieving ISO/IEC 27001 certification
Improved security posture
Reduced risk of security incidents
Like this project
Posted Sep 14, 2024
Mashooque's ISMS-driven threat intelligence system helped the client proactively detect and mitigate cyber threats, greatly improving their security posture.