What should I include in the job description when hiring a cybersecurity specialist?
To find the right cybersecurity expert, clearly state your project needs. Mention if you need help with network security, data protection, or risk assessments. Include any specific technologies or tools you want the freelancer to use. Describe the goals of the project and the skills needed. This helps attract the right specialist with the expertise you require.
How can I verify the qualifications of a freelance cybersecurity expert?
Check their profile for certifications and past project experiences. Look for qualifications like CISSP, CEH, or CISM. Read reviews and ratings from previous clients. Ask for examples of past work or testimonials that highlight their skills. This helps ensure they have the right knowledge to protect your systems.
What is a realistic timeline for a cybersecurity project?
The timeline depends on the complexity of the project. Discuss the scope of work with the freelancer to set realistic deadlines. A simple security audit might take a week, but implementing a full-scale security system could take months. Agree on milestones to track progress. This ensures the project stays on schedule.
How should I outline deliverables for a cybersecurity project?
List clear and detailed deliverables in your project brief. Specify what reports, analyses, or systems need to be implemented. Include expectations for documentation and ongoing support. This provides the freelancer with a roadmap to follow. It also ensures you receive all necessary reports and tools by project completion.
What should be included in a contract with a cybersecurity specialist?
Your contract should detail the scope of work, timelines, and specific deliverables. Include confidentiality and non-disclosure clauses to protect your data. Agree on a process for handling changes or additional requests. Make sure both parties clearly understand the terms. This keeps the project organized and protects sensitive information.
How can I assess the effectiveness of a cybersecurity expert’s work?
Review the deliverables and compare them to the initial project goals. Check for improvements in your system’s security and look for any security reports provided. Ask for a demonstration of the security measures put in place. This helps confirm that your systems are more secure and the freelancer met your project requirements.
What should I keep in mind when communicating with a cybersecurity freelancer?
Clear and regular communication is key. Set up regular check-ins or updates to discuss progress. Be open about any concerns or changes needed. Use simple and direct language to avoid misunderstandings. Keeping the communication channels open ensures a smooth collaboration.
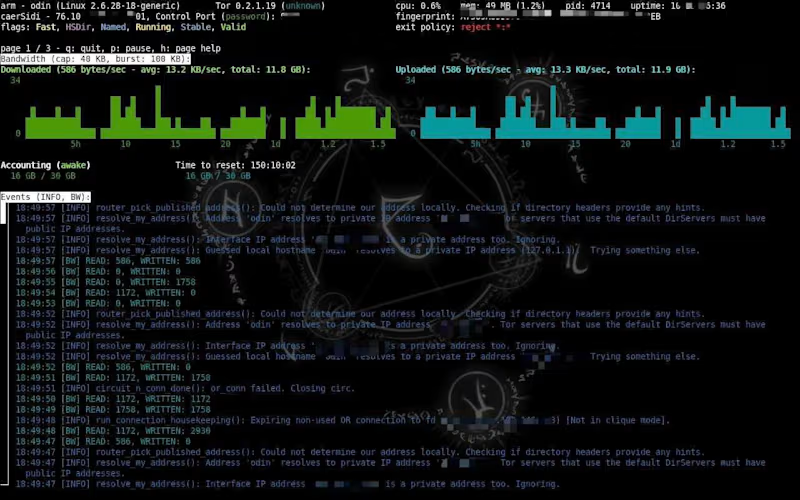
What security precautions should we consider at the start of the project?
Ensure the freelancer has limited access rights at the start. Use secure channels to share sensitive information. Set up regular updates to discuss any potential vulnerabilities. Have a plan in place for how data is stored and managed. Taking these steps helps protect your information right from the beginning.
How do I ensure ongoing security after the project ends?
Discuss ongoing support and maintenance options with the freelancer before the project ends. Set up a plan for regular security updates and patches. Ensure the knowledge transfer of any systems implemented is complete. This ensures your systems remain secure even after the freelancer’s involvement ends.
Who is Contra for?
Contra is designed for both freelancers (referred to as "independents") and clients. Freelancers can showcase their work, connect with clients, and manage projects commission-free. Clients can discover and hire top freelance talent for their projects.
What is the vision of Contra?
Contra aims to revolutionize the world of work by providing an all-in-one platform that empowers freelancers and clients to connect and collaborate seamlessly, eliminating traditional barriers and commission fees.