Gareth Karpel
Infrastructure & Security Architect
New to Contra
Gareth is ready for their next project!
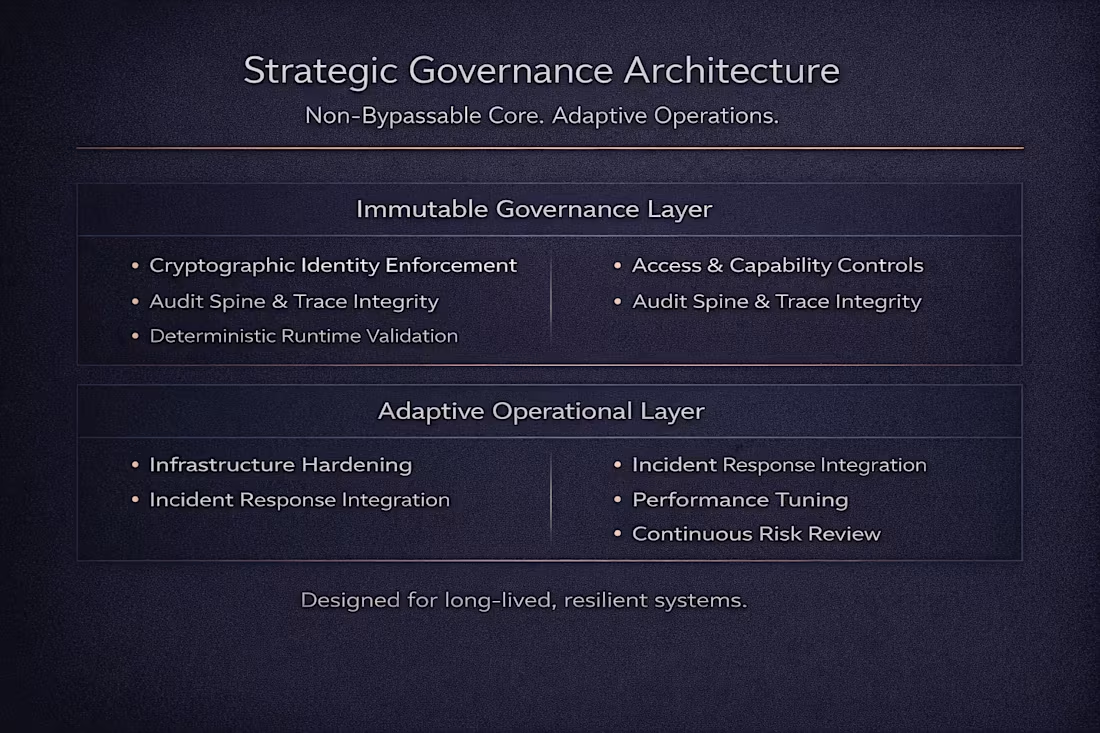
A structured governance model separating immutable enforcement layers from adaptive operational controls.
The immutable core enforces identity, capability boundaries, and audit integrity, while the adaptive layer manages runtime performance, infrastructure resilience, and incident response integration.
Designed for systems that must remain stable under pressure while retaining operational flexibility.
0
17
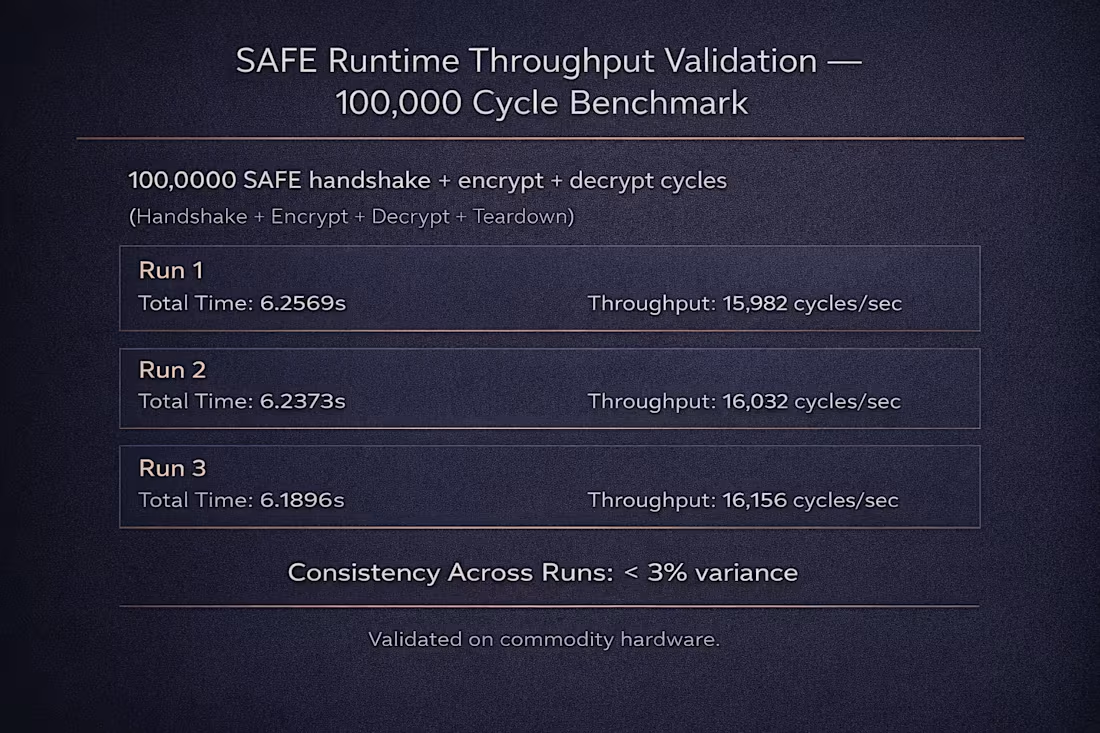
Throughput validation of the SAFE hybrid cryptographic runtime under sustained 100,000-cycle execution.
Each cycle includes handshake establishment, encryption, decryption, and teardown. Results demonstrate consistent ~16,000 cycles per second with minimal variance across runs, validating deterministic runtime stability and performance under load.
0
23
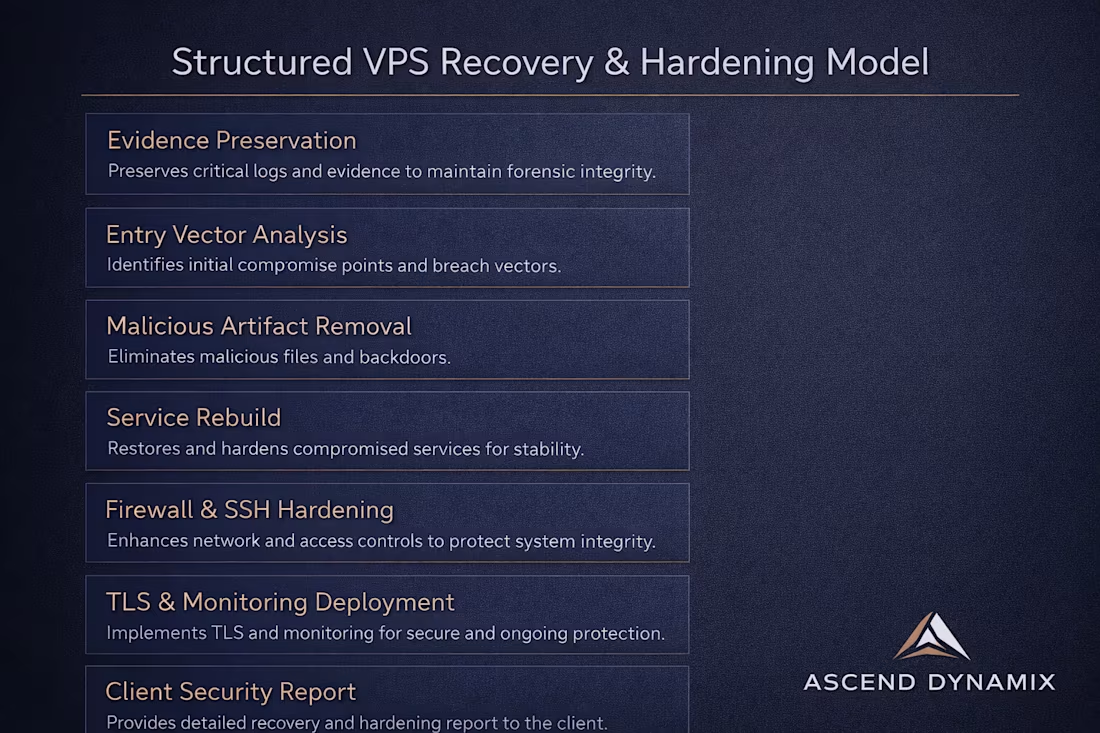
A structured, repeatable VPS incident response and hardening model used to restore compromised systems to stable, secure operation.
This workflow emphasizes forensic integrity, controlled rebuilds, layered access enforcement, and measurable post-recovery validation ensuring not just cleanup, but sustainable protection.
0
23
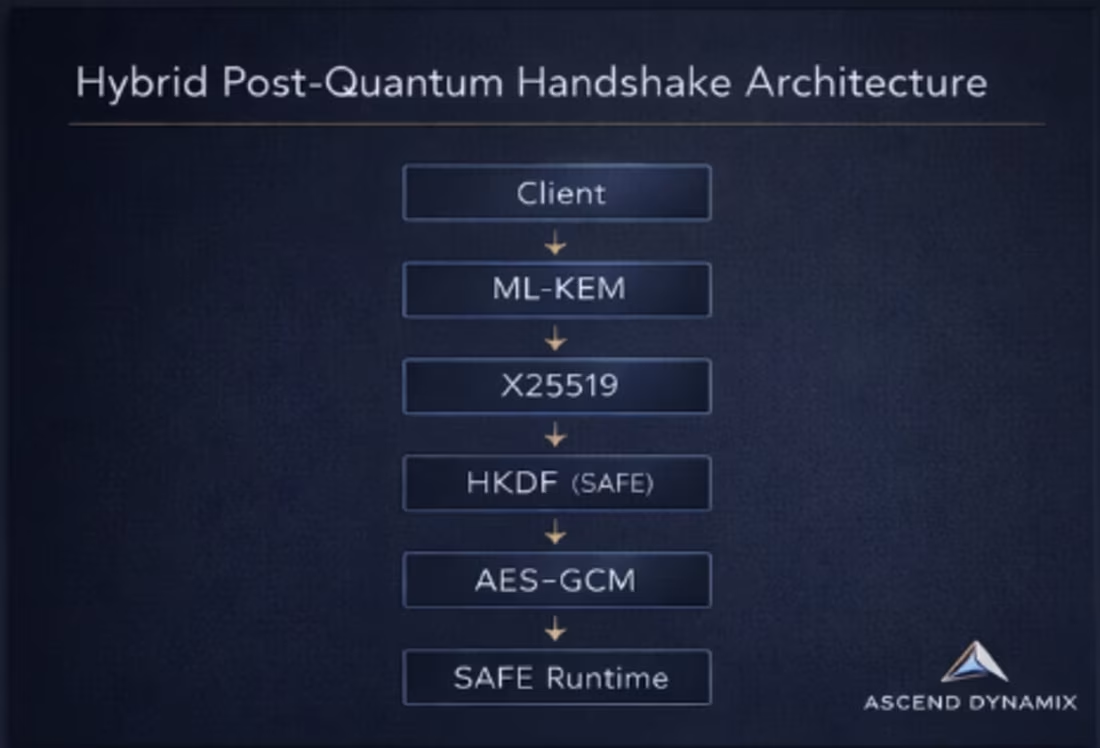
SAFE-Full is a hybrid post-quantum cryptographic runtime combining ML-KEM-768, HKDF, and AES-GCM into a structured, transcript-bound handshake process.
This benchmark validates deterministic execution, zero drift across 100 cycles, and sub-2ms full hybrid handshake performance on commodity hardware.
The objective is not theoretical performance — it is operational stability under real runtime conditions.
0
29