The network for creativity
Join 1.25M professional creatives like you
Connect with clients, get discovered, and run your business 100% commission-free
Creatives on Contra have earned over $150M and we are just getting started
Back to feedPost
Claude just made its Microsoft 365 connector available on every plan, including Free.
That should get every M365 admin’s attention.
This is not really a Claude story. It is an app consent + shadow AI + data governance story.
Because the real risk is not just one AI tool. It is the growing number of third-party apps and AI connectors that can touch your Microsoft 365 environment once they are approved. And if your tenant’s app consent model is too loose, or old OAuth grants are already sitting in your environment, you may have exposure long before leadership realizes it.
That means two things can be true at the same time:
AI adoption is inevitable for organizations that want to move forward.
Most tenants are not governing AI fast enough.
The uncomfortable part is this: AI does not need to create a brand-new security problem to hurt you. It can simply make your existing problems faster and more dangerous.
Overshared SharePoint sites.
Users with too much access.
Old delegated OAuth grants nobody reviewed.
Third-party apps that looked harmless at the time.
That is the real issue.
And this is not theoretical. Malicious OAuth apps have been a real attack path for years. A consent screen can look harmless, a user clicks approve, and now a third-party app may have persistent access until someone actually finds and revokes it.
If you administer Microsoft 365, here is the checklist I would work through this week:
Review Enterprise Applications in Entra and investigate apps you do not recognize.
Review delegated permissions and old consent grants, not just newly added apps.
Tighten user consent settings and require admin review where appropriate.
Enable an admin consent workflow so users cannot casually approve risky apps on their own.
Review where sensitive data lives in M365 and who can access it.
Send a simple internal note: do not connect AI tools to company systems without approval.
Start an actual AI use policy, even if version one is only a page.
This is not about being anti-AI.
It is about making sure AI adoption happens on purpose — with app control, data control, and leadership awareness — instead of by accident.
If your team is not sure what is already connected, what users have already approved, or where your biggest M365 exposure sits today, that is probably the first thing to assess.

The network for creativity
Join 1.25M professional creatives like you
Connect with clients, get discovered, and run your business 100% commission-free
Creatives on Contra have earned over $150M and we are just getting started
Related posts
Which WordPress Update do you find most exciting and professional
The Connector (Open AI, Claude Anthropic and Google Gemini)
Or
The New Design System (Real Time Collaboration, The Note System, Command Palette, Smart Block Editor)
1 voted
100%
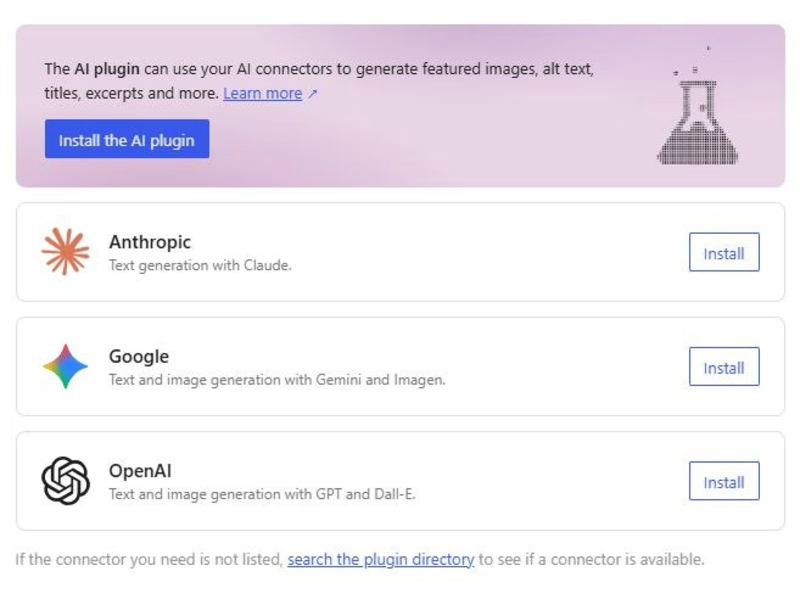
0 voted
0%
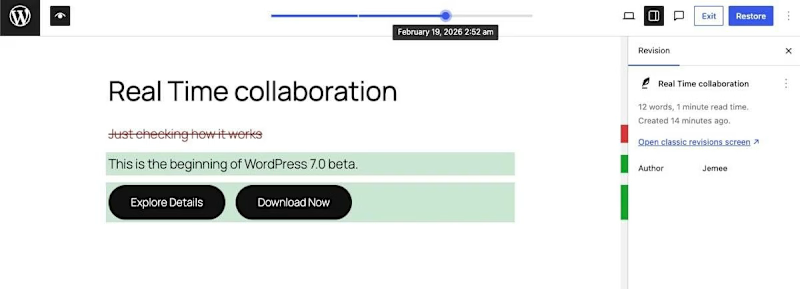
1 vote
Closed
Exceptional execution on the overall presentation.
Which AI model would actually survive a real ad agency brief?
I put Kling 3.0 and Seedance 2.0 head-to-head with the exact same frames. Same prompt. Same creative direction.
And honestly, choosing between models is starting to feel a lot closer to choosing a director than choosing a tool.
Because each one interprets motion, realism, pacing, and atmosphere completely differently.
Prompt’s in the comments if you want to test it with your own product.
They both still need some extra editing and work, but I definitely have a favorite.
Who’s winning this one for you?
29 voted
39%
45 voted
61%
74 votes
Closed
The starting frame vs ending frame.
I generated both frames with Nano Banana 2 and used them as the transition points for the video generation.
I wanted it to feel like one continuous world: floating tension → gravity switches on → full liquid impact


Premium SaaS-style Claude AI edit with clean UI motion, smooth pacing, and sharp product storytelling.
Trending
Claude
Claude has entered the design space. How are you using Claude Design?
Contra University
Learn from expert creatives how to earn more using next-gen AI tools.
creativeaiflow
Creative AI workflows are evolving. What tools do you use, and what are their strengths and weaknesses?
portfolioreview
The best portfolios tell a story, not just show a grid. Share yours for feedback.
freelancerlife
Freelancer life is wins, pivots, and everything in between. What’s yours right now?