Afraha Yousuf
Cybersecurity Analyst | Threat Detection & Log Analysis
New to Contra
Afraha is building their profile!
Sarah AI: 24/7 Intelligent Lead Generation Assistant
AI Automation Specialist
Developed a custom AI chatbot using Botpress to automate lead generation for the real estate industry. The assistant, named 'Sarah,' is designed to engage with potential clients 24/7, qualify leads by asking specific questions (budget, location, requirements), and capture contact information seamlessly. This solution ensures no lead is missed outside of business hours and provides a personalized, human-like interaction for users
3
27
Luxury Brand Identity & Typography Logo Design
Created a premium brand identity for 'Glamour Spot Fashion' (GSF). The logo features a minimalist lotus-inspired floral icon combined with elegant gold gradients on a deep black background. The design reflects luxury, sophistication, and a high-end fashion appeal. I focused on clean lines and balanced typography to ensure the brand stands out in the competitive e-commerce market
1
15
Promotional Banner Design for Fashion E-commerce
Designed a high-converting promotional banner for an e-commerce fashion brand ('Glamour Spot Fashion'). Focused on creating a visually appealing layout with a luxury feel, using balanced typography and clean product placement to highlight a seasonal sale. The design was optimized for social media marketing and website headers
1
19
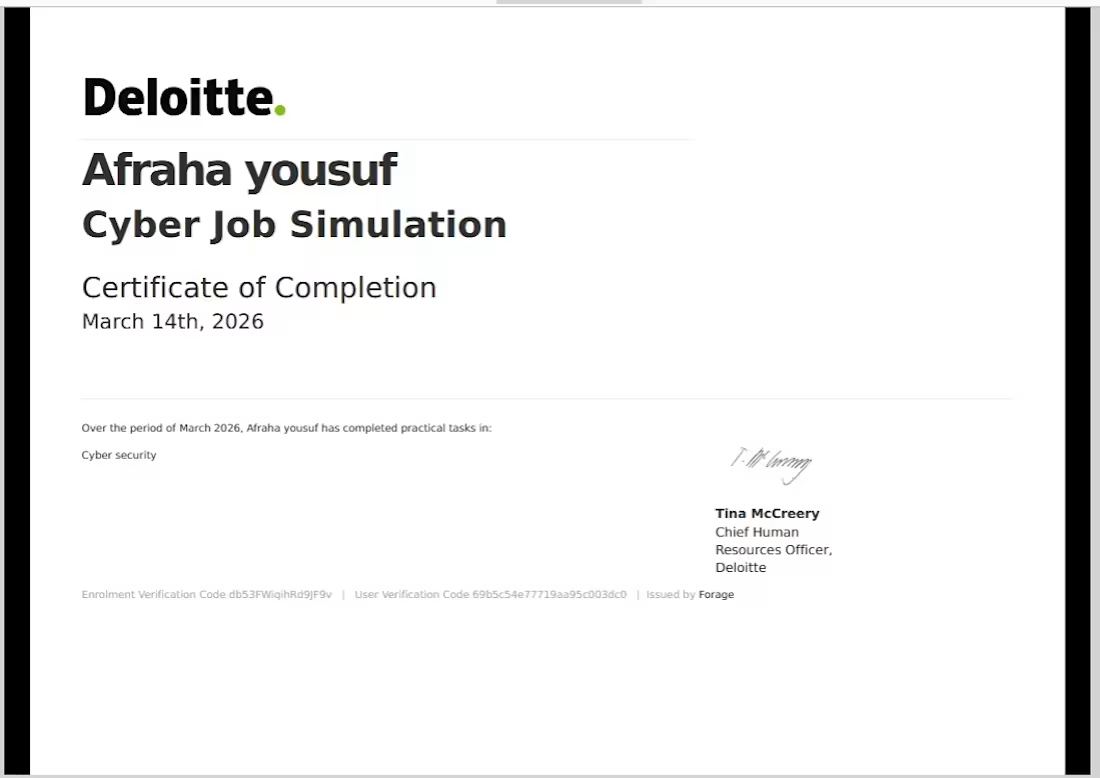
Successfully completed a professional cybersecurity simulation with Deloitte Australia. Key tasks included:
Log Analysis: Monitored web activity logs to identify suspicious patterns and unauthorized access.
Threat Detection: Differentiated between legitimate user traffic and potential malicious attacks.
Incident Response: Provided actionable recommendations to mitigate security breaches and protect client data.
Documentation: Prepared technical reports on security findings and suggested defense improvements
1
38