Microsoft 365 Security Assessmentibukun Babalola
Most businesses using Microsoft 365 have never had an independent security review and are surprised by what's exposed.
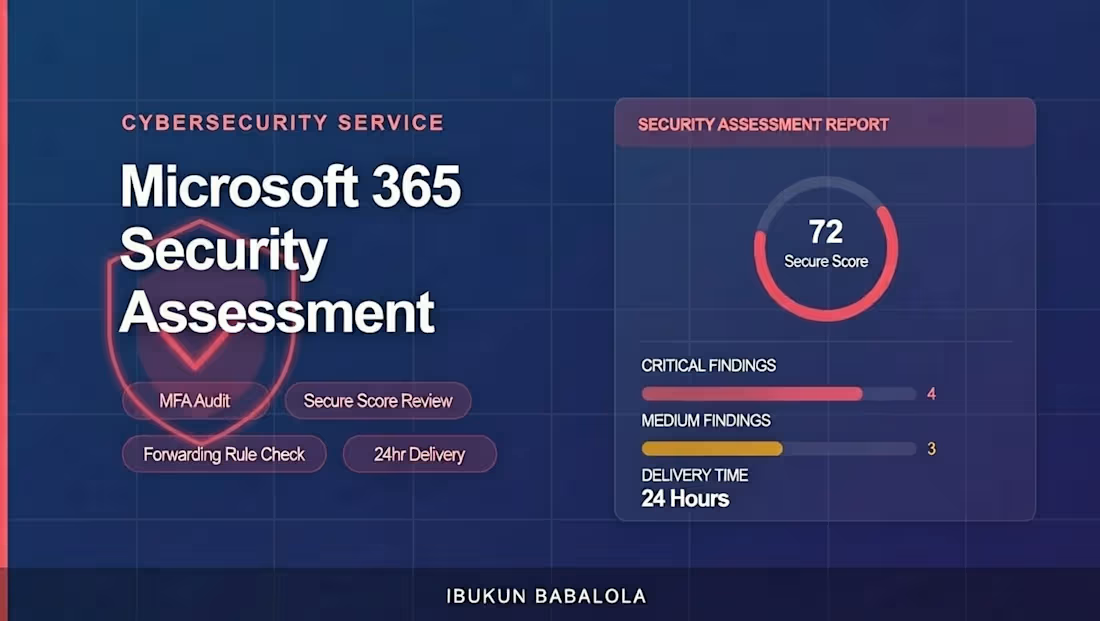
I run a rapid, read-only audit of your entire M365 environment and deliver a plain-English, prioritized report within 24 hours. No jargon. No fluff. Just a clear list of what's open, what's critical, and what to fix first.
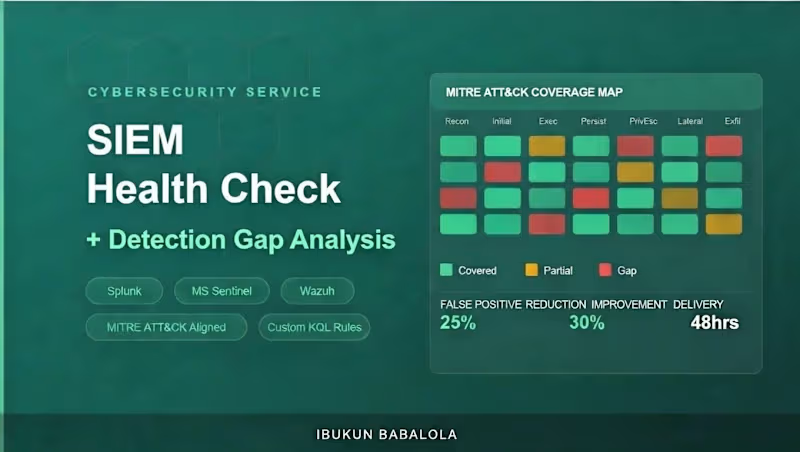
I recently completed a remote SOC analyst contract with an Australian managed security provider, monitoring live environments across Microsoft Sentinel, Splunk, and CrowdStrike Falcon.
What I check:
Microsoft Secure Score baseline and top recommendations
MFA status across all user accounts (including admins)
Email forwarding rules — the #1 active compromise indicator
Conditional Access policies (or the complete absence of them)
SharePoint and OneDrive external sharing configuration
Inactive and over-privileged admin accounts
Audit log retention status
What you get:
A 2-page PDF report structured for both technical and non-technical readers: Executive Summary → Critical Findings → Medium Findings → Priority Action Plan with time estimates for each fix.
Certifications: CompTIA Security+ · ISC2 Certified in Cybersecurity · Microsoft AZ-900 · SC-900
FAQs
ibukun's other services
Starting at$50
Duration1 week
Tags
AWS
Risk Assessment
Cloud Security Engineer
Cybersecurity Specialist
microsoft 365
Information Security
Microsoft Azure
saas
security Audit
Service provided by
ibukun Babalola Lagos, Nigeria

Microsoft 365 Security Assessmentibukun Babalola
Starting at$50
Duration1 week
Tags
AWS
Risk Assessment
Cloud Security Engineer
Cybersecurity Specialist
microsoft 365
Information Security
Microsoft Azure
saas
security Audit
Most businesses using Microsoft 365 have never had an independent security review and are surprised by what's exposed.
I run a rapid, read-only audit of your entire M365 environment and deliver a plain-English, prioritized report within 24 hours. No jargon. No fluff. Just a clear list of what's open, what's critical, and what to fix first.
I recently completed a remote SOC analyst contract with an Australian managed security provider, monitoring live environments across Microsoft Sentinel, Splunk, and CrowdStrike Falcon.
What I check:
Microsoft Secure Score baseline and top recommendations
MFA status across all user accounts (including admins)
Email forwarding rules — the #1 active compromise indicator
Conditional Access policies (or the complete absence of them)
SharePoint and OneDrive external sharing configuration
Inactive and over-privileged admin accounts
Audit log retention status
What you get:
A 2-page PDF report structured for both technical and non-technical readers: Executive Summary → Critical Findings → Medium Findings → Priority Action Plan with time estimates for each fix.
Certifications: CompTIA Security+ · ISC2 Certified in Cybersecurity · Microsoft AZ-900 · SC-900
FAQs
ibukun's other services
$50