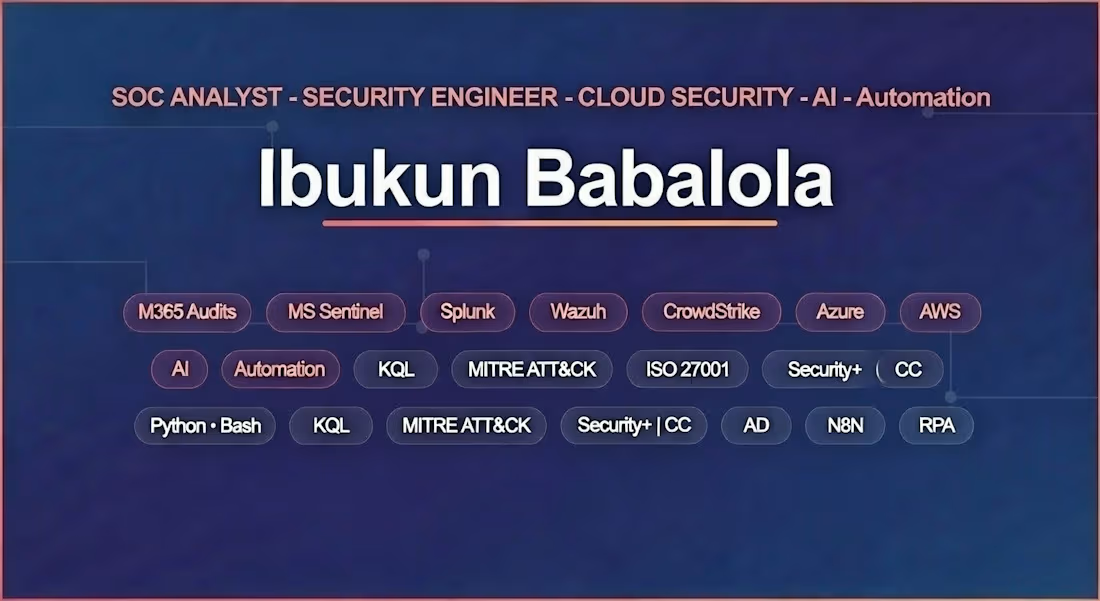
ibukun Babalola
SOC Analyst |M365 · SIEM · Security Engineer · AI Automation
New to Contra
ibukun is ready for their next project!
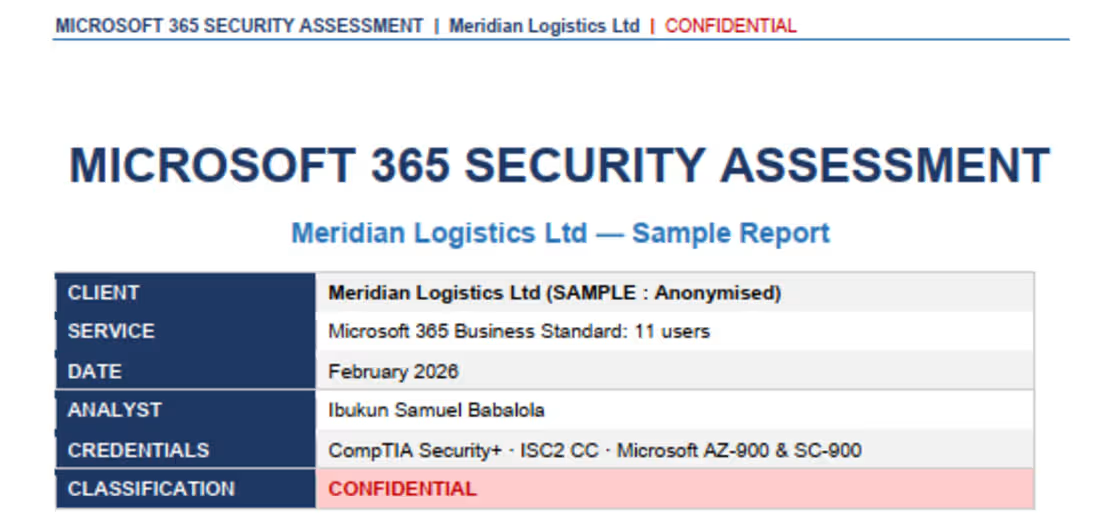
Performed a read-only Microsoft 365 security assessment for an 11-user UK logistics company, uncovering two Critical findings: MFA disabled on Global Administrator accounts and an active email forwarding rule on the Finance Manager's mailbox consistent with Business Email Compromise. Delivered a clear priority action plan, all remediable within 72 hours using tools already included in the client's existing M365 licence along with SharePoint sharing controls and Conditional Access policy configuration to close legacy authentication gaps.
0
14
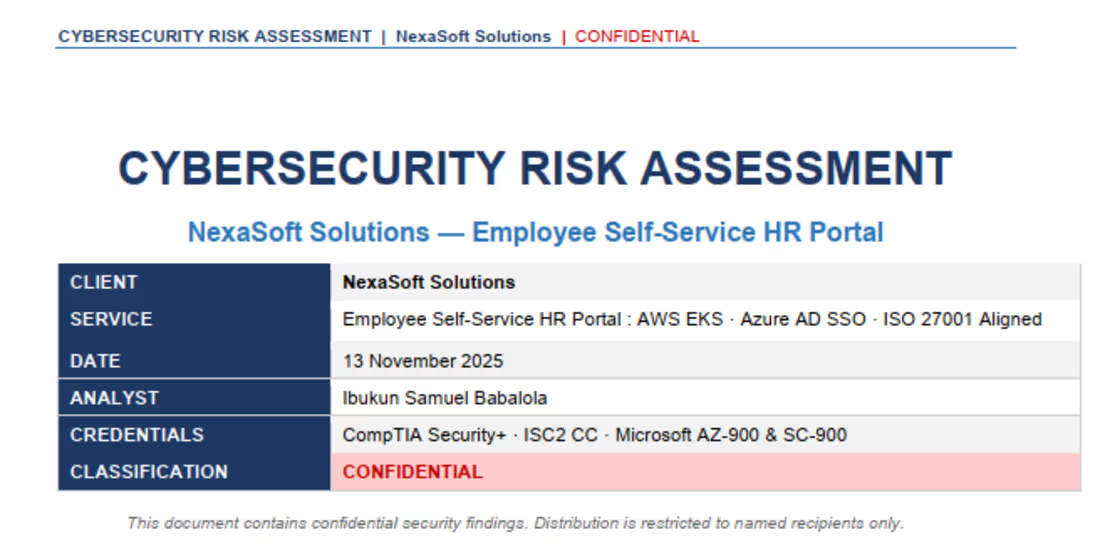
Conducted a full cybersecurity risk assessment for NexaSoft's AWS EKS-hosted Employee Self-Service HR Portal, processing sensitive employee PII including payroll, health records, and government-issued ID. Identified three Critical and five High risks across Azure AD SSO, cloud IAM configuration, and insider privilege controls, aligned to ISO 27001. Delivered a prioritised 90-day remediation roadmap using native AWS and Azure tooling, reducing all Critical risks before go-live and supporting the client's ongoing ISO 27001 certification obligations under Australia's Privacy Act 1988.
0
15
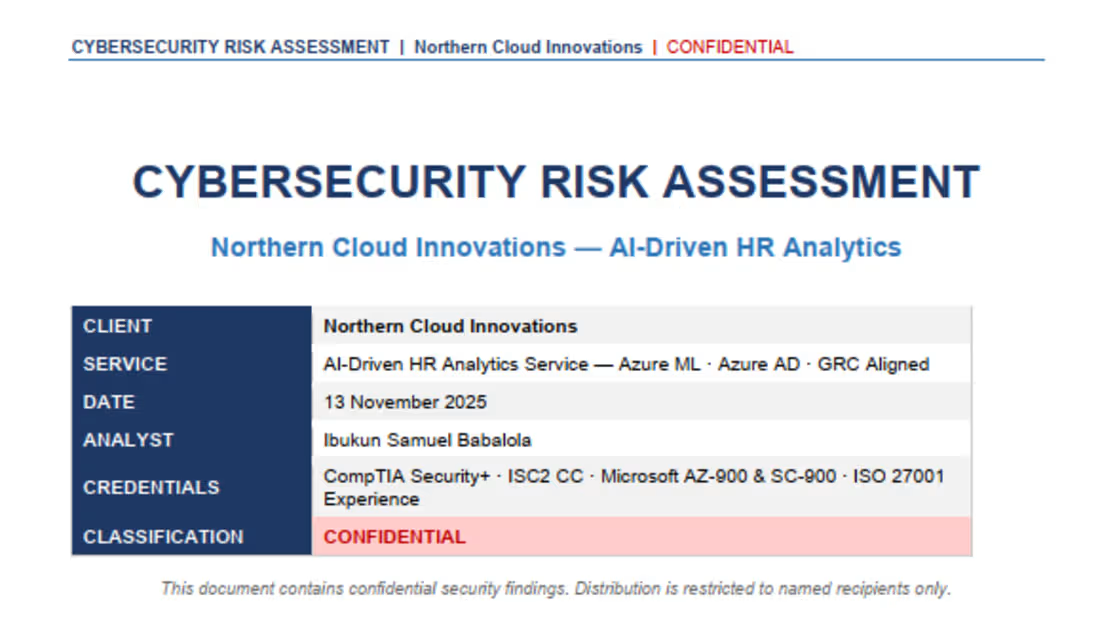
Delivered a GRC-aligned cybersecurity risk assessment for an Azure-hosted AI-Driven HR Analytics Service processing employee PII and behavioural data. This engagement went beyond conventional security reviews to address AI-specific risks including data poisoning and model bias that carry direct legal exposure under the Canadian Human Rights Act and the proposed AI and Data Act (AIDA). Identified five High risks and produced a mitigation strategy using Azure-native controls, alongside governance recommendations to ensure compliant and auditable AI decision-making ahead of AIDA enforcement.
0
17
Worked as a remote SOC Analyst at CyberEdge Solutions (Australia): a managed security provider from November 2025 to February 2026. Operated across Splunk, Microsoft Sentinel, and Wazuh in a 24/7 production monitoring environment.
Key outcomes:
Reduced false positive rate by 25% through MITRE ATT&CK-aligned detection rule tuning.
Improved mean time to respond (MTTR) by 30% through Python and PowerShell automation.
Reduced log ingestion costs by 20% through optimised data collection.
Led end-to-end incident response for malware infections, unauthorised access, and cloud account compromise.
Maintained ISO 27001 compliance documentation and coordinated with engineering teams during high-severity incidents
0
19
Designed and deployed a complete phishing awareness simulation using GoPhish on Microsoft Azure with DuckDNS for clean tracking links. Built and sent a holiday-themed phishing campaign to a test group.
Result: 62.5% click rate , demonstrating exactly how exposed users are to social engineering without awareness training.
The campaign findings drove concrete improvements in the organisation's security awareness programme. Full methodology, results, and recommendations documented in a published write-up on Medium.
0
16
Deployed a cloud-native SIEM integrating Microsoft Azure infrastructure, Windows endpoints, Microsoft 365, and Defender XDR telemetry into a unified detection and response platform.
Wrote KQL analytics rules for real-time threat detection covering: privilege escalation, suspicious PowerShell execution, lateral movement via RDP and SMB, anomalous Azure AD sign-ins, and malware execution patterns. Automated incident response using Azure Logic Apps.
Reduced log ingestion costs by 20% through optimised data collection, balancing coverage against cost without losing detection fidelity.
Published full write-up on Medium: medium.com/@babsib2dk
0
12
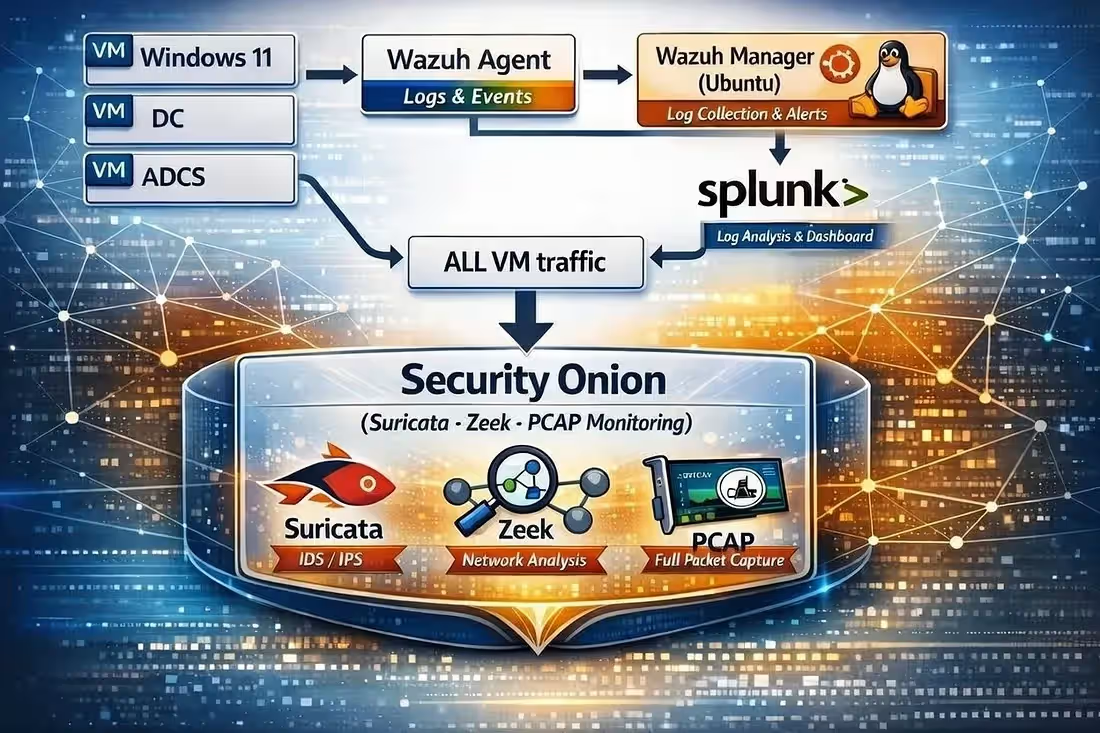
Built a complete enterprise-grade SOC environment from scratch: featuring Wazuh SIEM with custom detection rules, Security Onion with Suricata IDS/IPS and Zeek network monitoring, Active Directory with advanced security logging via Group Policy, and Windows Server with Sysmon telemetry. Designed and executed MITRE ATT&CK-aligned attack simulations from Kali Linux and validated detection coverage through red team exercises. Achieved over 95% detection rate across all tested techniques and tactics. This project served as the foundation for understanding how detection engineering decisions translate into real gaps and how to close them.
0
23