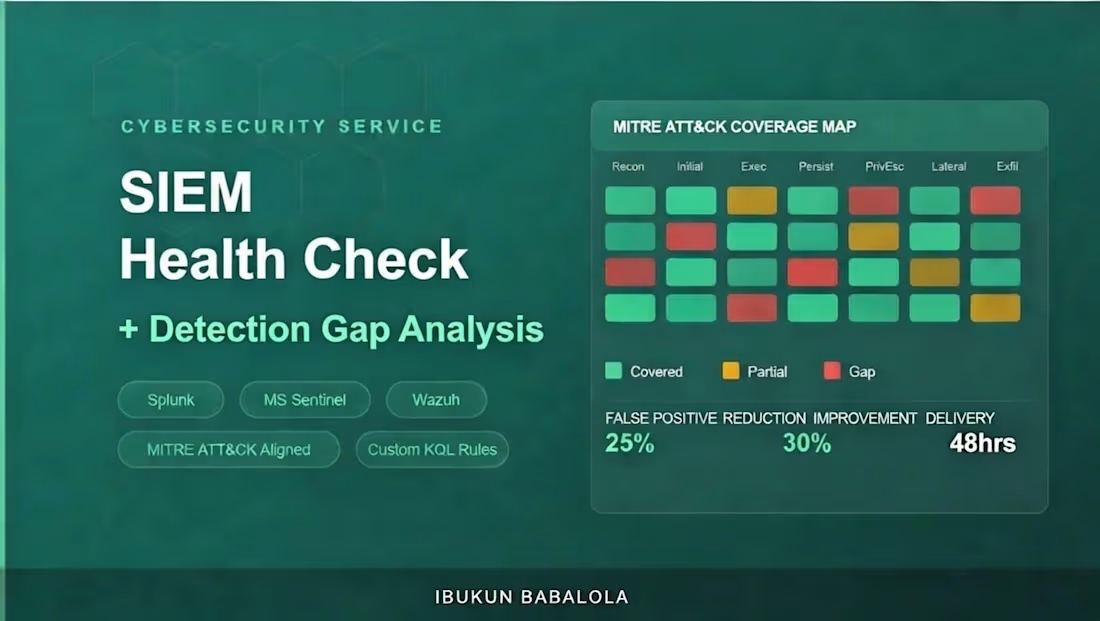
SIEM Health Check + Detection Gap Analysisibukun Babalola
Your SIEM was deployed to protect you. But if the detection rules haven't been mapped against MITRE ATT&CK, you have blind spots you don't know about and attackers do.
I review your entire SIEM deployment and deliver a gap analysis showing exactly where your coverage ends, what techniques you're not detecting, and custom-written rules to close the most critical gaps.
At CyberEdge Solutions (Australia), I reduced false positive rates by 25% and improved mean time to respond by 30% through structured detection engineering and rule tuning in a live production SOC.
Platforms I work with:
Microsoft Sentinel (KQL) · Splunk (SPL) · Wazuh · Security Onion
What I assess:
Detection rule coverage mapped against MITRE ATT&CK Navigator
False positive hotspots and tuning opportunities
Log source gaps what isn't being ingested
Dashboard relevance and alert fatigue analysis
Data ingestion cost vs. detection value
What you get:
MITRE ATT&CK heatmap of your current coverage (covered / partial / gap)
Top 5 detection gaps with risk rating
2–3 custom detection rules written for your environment (KQL or SPL with full syntax)
False positive reduction recommendations
90-day tuning roadmap
Certifications: CompTIA Security+ · ISC2 CC · Microsoft SC-900 · AZ-900
FAQs
ibukun's other services
Starting at$100
Duration1 day
Tags
Splunk
Cloud Security Engineer
Cybersecurity Specialist
Information Security
microsoft sentinel
MITRE ATT&CK
Security Operations
SIEM
Threat Detection
Service provided by
ibukun Babalola Lagos, Nigeria

SIEM Health Check + Detection Gap Analysisibukun Babalola
Starting at$100
Duration1 day
Tags
Splunk
Cloud Security Engineer
Cybersecurity Specialist
Information Security
microsoft sentinel
MITRE ATT&CK
Security Operations
SIEM
Threat Detection
Your SIEM was deployed to protect you. But if the detection rules haven't been mapped against MITRE ATT&CK, you have blind spots you don't know about and attackers do.
I review your entire SIEM deployment and deliver a gap analysis showing exactly where your coverage ends, what techniques you're not detecting, and custom-written rules to close the most critical gaps.
At CyberEdge Solutions (Australia), I reduced false positive rates by 25% and improved mean time to respond by 30% through structured detection engineering and rule tuning in a live production SOC.
Platforms I work with:
Microsoft Sentinel (KQL) · Splunk (SPL) · Wazuh · Security Onion
What I assess:
Detection rule coverage mapped against MITRE ATT&CK Navigator
False positive hotspots and tuning opportunities
Log source gaps what isn't being ingested
Dashboard relevance and alert fatigue analysis
Data ingestion cost vs. detection value
What you get:
MITRE ATT&CK heatmap of your current coverage (covered / partial / gap)
Top 5 detection gaps with risk rating
2–3 custom detection rules written for your environment (KQL or SPL with full syntax)
False positive reduction recommendations
90-day tuning roadmap
Certifications: CompTIA Security+ · ISC2 CC · Microsoft SC-900 · AZ-900
FAQs
ibukun's other services
$100