Credit-Card Aggregation Website Backend
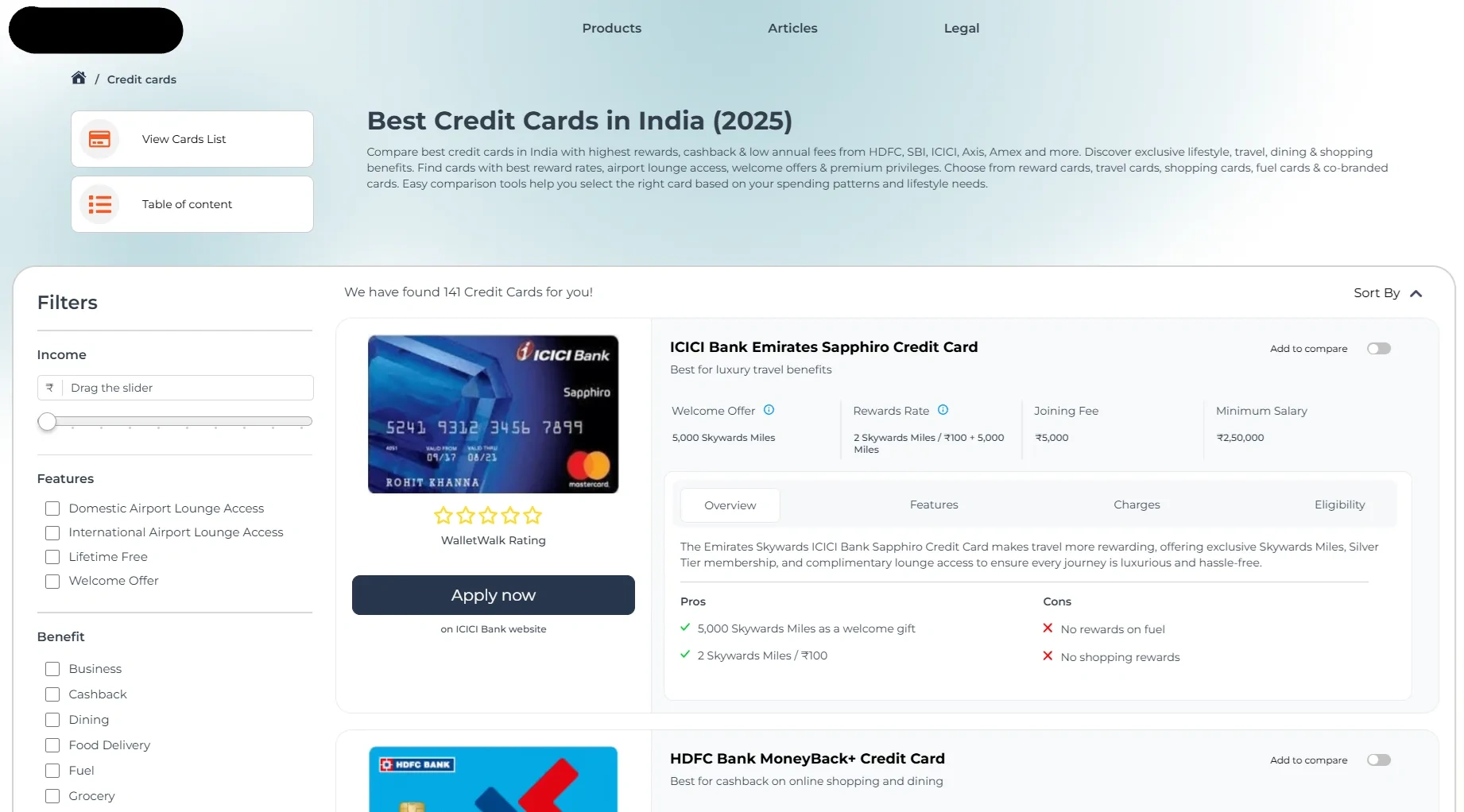
Credit-Card Aggregator Website Backend
Collaborated within a two-person development team to create a sophisticated website platform for a credit card aggregation service with a market presence in both Singapore and India. My primary responsibilities centered on the backend development and architectural design of the system.
The application was built leveraging the power of Next.js and Payload CMS, PostgreSQL was used for database. A central element of the project was the design and implementation of a comprehensive admin system.
This system incorporated a robust user access control model, featuring multiple, distinct user roles with granular permissions, ensuring data security and operational integrity. User authentication was multifaceted and highly secure, supporting email and password login, social authentication, phone number verification via OTP, and robust two-factor authentication using TOTP generated by authenticator applications, alongside provisions for one-click authentication.
Like this project
Posted Mar 1, 2025
Fully Coded Backend in Next.js for a credit-card aggregation active in India and Singapore. Implemented Authentication, custom CMS, multi-tenant system.
Likes
0
Views
0
Timeline
Mar 1, 2024 - Sep 30, 2024