David Simonic Galun
System & Workflow Architect
New to Contra
David is ready for their next project!
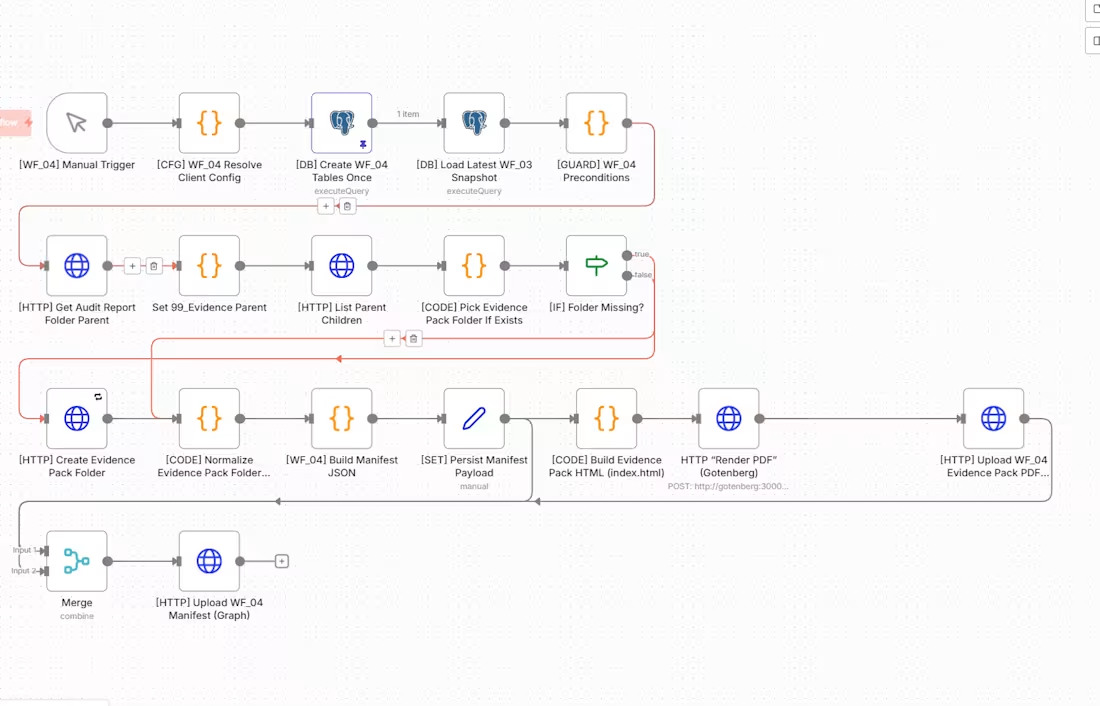
n8n Evidence Pack Builder with PDF Generation and Graph Upload
Designed and implemented a modular n8n workflow that turns prior audit outputs into a finalized evidence pack with manifest generation, HTML-to-PDF rendering, and Microsoft Graph upload. This workflow loads the latest validated audit snapshot, checks preconditions, resolves the target evidence location, creates the evidence pack folder if needed, and then assembles the final delivery artifacts in a structured way.
The architecture separates state loading, guard logic, folder resolution, conditional folder creation, manifest construction, payload persistence, HTML generation, PDF rendering, and upload operations into dedicated stages. This made the workflow easier to troubleshoot, safer to rerun, and more reliable for repeatable evidence packaging.
A key design goal was controlled delivery. Instead of leaving outputs as disconnected JSON files, this workflow normalizes the evidence pack structure, builds a formal manifest, renders a presentation-ready PDF artifact, and uploads both machine-readable and stakeholder-friendly deliverables into the correct destination. The result is a packaging layer that converts workflow outputs into a clean handoff artifact.
This workflow is part of a larger modular n8n system built for deterministic execution, evidence traceability, and production-oriented delivery rather than basic automation chaining.
1
17
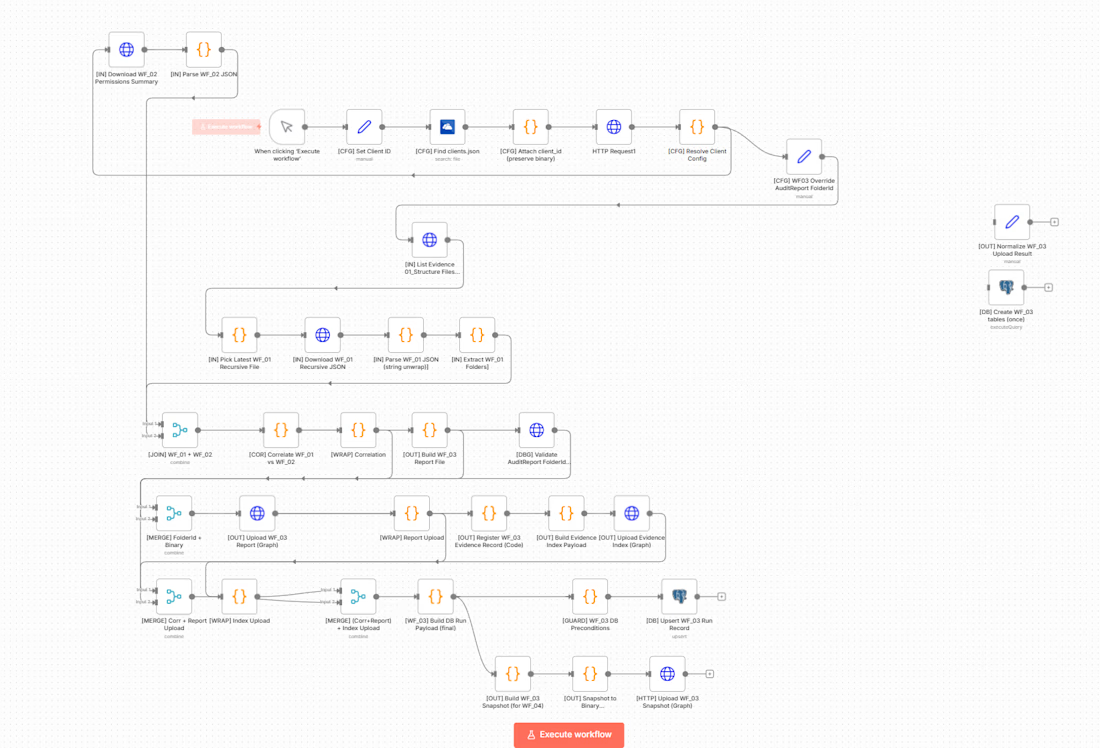
n8n Audit Correlation Workflow with Evidence Report Generation
Designed and implemented a modular n8n workflow that correlates structural and permissions evidence to produce an audit-ready result set and report artifacts. This workflow consumes outputs from earlier workflows, cross-references structure and access data, evaluates consistency, builds a formal correlation result, and generates structured report files for downstream evidence packaging.
The architecture was designed around separation of concerns. Rather than mixing scanning, validation, and reporting in one chain, this workflow focuses specifically on correlation, decision logic, and artifact generation. It loads prior evidence, compares datasets, produces a clear pass/fail style outcome, builds machine-readable report outputs, and uploads them into the designated evidence location.
A major priority was traceability. The workflow generates structured report files, maintains evidence indexing, and supports a reproducible audit trail that can be reused by later packaging and delivery workflows. The result is a reporting layer that converts raw workflow outputs into a coherent and defensible evidence artifact.
This workflow is part of a larger n8n system built with modularity, deterministic execution, and audit-grade output standards in mind.
1
14
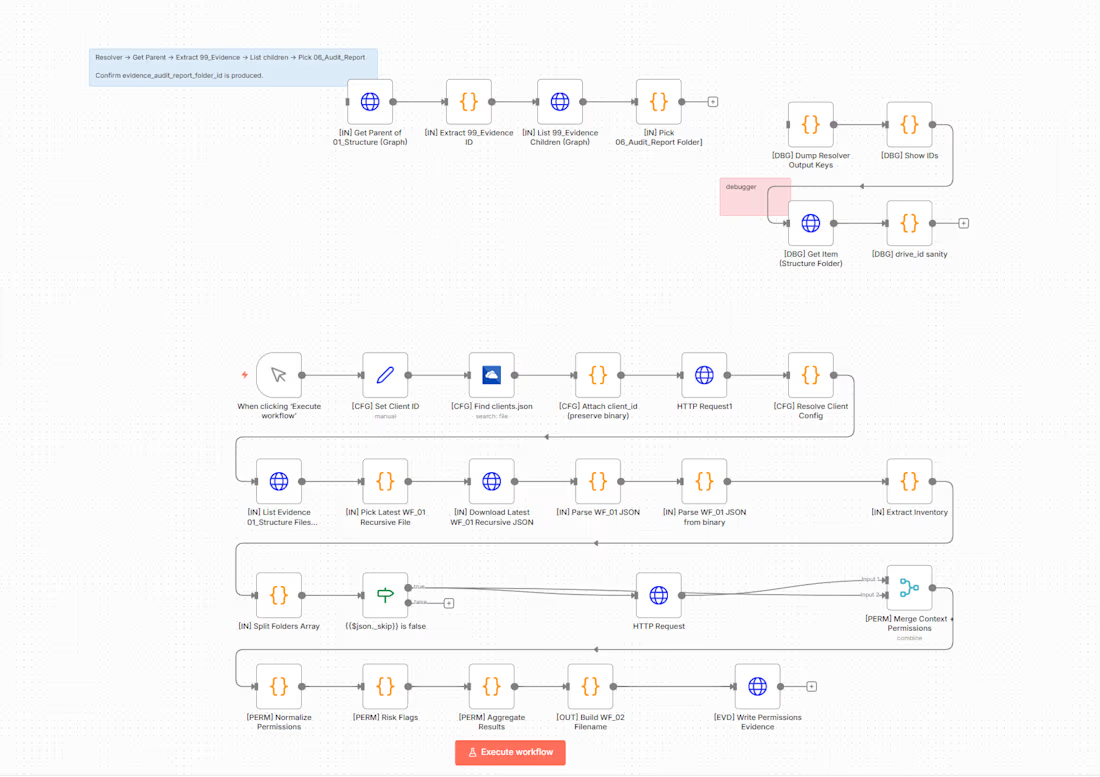
n8n Permissions Audit Workflow using Microsoft Graph
Designed and implemented a modular n8n workflow to audit folder permissions in a Microsoft 365 environment using Microsoft Graph. This workflow resolves client configuration, loads the latest recursive structure artifact from a prior workflow, extracts the folder inventory, and then processes each folder through a permission-analysis pipeline.
The architecture separates resolver logic, evidence lookup, inventory extraction, folder splitting, permission retrieval, context merging, normalization, risk flagging, aggregation, and final evidence writing into dedicated stages. This was done intentionally to keep the workflow deterministic, easier to debug, and safe to rerun.
A core design goal was to avoid shallow permission checks and instead generate structured, audit-friendly outputs. The workflow normalizes permission objects, evaluates risk conditions, aggregates results into a summarized evidence artifact, and writes the final output in a reusable format for downstream reporting and governance workflows.
This is part of a broader workflow system built for reliability, traceability, and modular expansion rather than simple one-step automation.
1
16
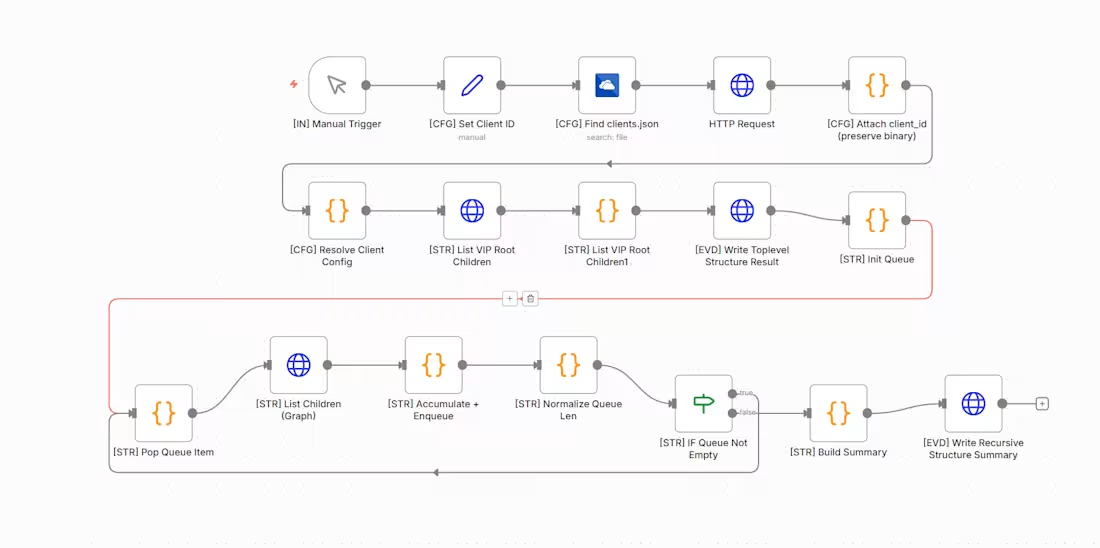
n8n Workflow 01, Recursive Structure Discovery Engine
This workflow is part of a larger modular automation system built in n8n. Its responsibility is to discover, traverse, and summarize a client’s folder hierarchy in a controlled and repeatable way.
It starts with client identification and configuration loading, then uses Microsoft Graph HTTP requests to list root and child items, initializes a traversal queue, processes items iteratively, normalizes queue state, checks branch conditions, and finally writes structured summary artifacts. The design avoids fragile one-shot logic and instead uses queue-based recursion to support reliability, clarity, and future extensibility.
This workflow was built with production thinking in mind: explicit control flow, reusable modules, clean outputs, and compatibility with downstream audit and evidence-generation workflows.
1
24