The network for creativity
Join 1.25M professional creatives like you
Connect with clients, get discovered, and run your business 100% commission-free
Creatives on Contra have earned over $150M and we are just getting started
Back to feedPost
Cyber Security Services for Startup-Scale Infrastructure
Startups scaling their infrastructure often prioritize speed, feature delivery, and market expansion over structured security governance. Early-stage systems evolve rapidly, integrating cloud services, third-party APIs, and distributed access models without a unified control layer. This creates an environment where visibility is limited, configurations drift over time, and dependencies grow without clear oversight. As the organization scales, these gaps compound, making it difficult to track risks or enforce consistent policies. Attackers frequently target such environments, knowing that rapid growth often outpaces security maturity. The challenge is to establish a security model that scales alongside infrastructure without slowing down innovation or operational agility.
Understanding Modern Cyber Security Services
For scaling startups, cyber security services provide a structured foundation to unify security across cloud and network environments. Instead of fragmented tools, these services integrate governance, monitoring, and response into a cohesive model. cyber security services enable startups to standardize access controls, track system interactions, and maintain visibility across rapidly expanding infrastructure. This integration reduces operational complexity and ensures that security evolves with the organization. By embedding governance into core operations, startups can avoid reactive firefighting and instead adopt a proactive approach that aligns with long-term growth and infrastructure scalability.
Why Cloud Security Services and Assessments Matter
Startups typically rely heavily on cloud environments, making cloud security services critical for maintaining control over dynamic workloads and user access. These services enforce consistent policies across environments, ensuring that rapid deployments do not introduce unmanaged risks. A key component of this approach is cloud security assessment, which continuously evaluates configurations, permissions, and compliance alignment. Without regular assessment, fast-paced development cycles can lead to unnoticed misconfigurations and privilege issues. By combining cloud security services with continuous evaluation, startups can maintain security integrity while scaling operations, ensuring that agility does not come at the cost of exposure.
Strengthening Defenses with Network Security Solutions
As infrastructure expands, startups must implement layered defenses to manage increasing complexity. network security solutions provide segmentation and traffic visibility, reducing the risk of unauthorized movement within systems. These controls are essential in hybrid and distributed environments where boundaries are not clearly defined. Complementing this, endpoint security services protect devices and access points that often serve as entry vectors for attackers. When integrated with threat detection and response, startups gain the ability to identify suspicious behavior in real time and respond before incidents escalate. This layered approach ensures consistent protection across both network and endpoint layers.
The Role of Penetration Testing and Vulnerability Assessments
Rapid development cycles often introduce vulnerabilities that are not immediately visible. vulnerability assessment and penetration testing provide a structured way to identify these weaknesses before they are exploited. Through penetration testing services, startups can simulate real-world attacks and evaluate how their systems respond under pressure. network penetration testing focuses on infrastructure-level risks such as segmentation gaps and privilege escalation paths. Meanwhile, web application security testing addresses vulnerabilities within applications, including authentication flaws and insecure data handling. These practices enable startups to prioritize remediation efforts effectively, ensuring that critical risks are addressed early in the scaling process.
Leveraging Cyber Threat Intelligence for Proactive Security
As startups grow, understanding the threat landscape becomes increasingly important. cyber threat intelligence provides insights into attacker behavior, emerging risks, and industry-specific vulnerabilities. This intelligence helps startups focus their security efforts on the most relevant threats. When combined with cybersecurity consulting services, it supports informed decision-making across architecture design and risk management. Instead of reacting to incidents, startups can anticipate potential attack vectors and implement preventive controls. This proactive approach ensures that security strategies remain aligned with growth objectives while strengthening long-term resilience.
Key Takeaways
cloud security services help organizations maintain control over dynamic environments
cloud security assessment ensures continuous visibility into configuration and compliance risks
network security solutions and endpoint security services strengthen overall defense posture
threat detection and response improves real-time identification and mitigation of security incidents
vulnerability assessment and penetration testing identify exploitable risks before attackers do
cyber threat intelligence and cybersecurity consulting services enable proactive, intelligence-driven security strategy
Conclusion
For startups scaling infrastructure, security must evolve alongside growth rather than follow it. As systems expand and complexity increases, maintaining visibility and control becomes critical to sustaining operational stability. By adopting an architecture-led approach that integrates governance, validation, and intelligence, startups can build a resilient security foundation without compromising agility. Embedding security into core processes ensures that risks are managed proactively, enabling confident scaling and long-term sustainability. This approach transforms security from a reactive necessity into a strategic capability that supports innovation, resilience, and controlled expansion.

The network for creativity
Join 1.25M professional creatives like you
Connect with clients, get discovered, and run your business 100% commission-free
Creatives on Contra have earned over $150M and we are just getting started
Related posts
Cybersecurity training using the Colonial Pipeline ransomware attack as an exercise.

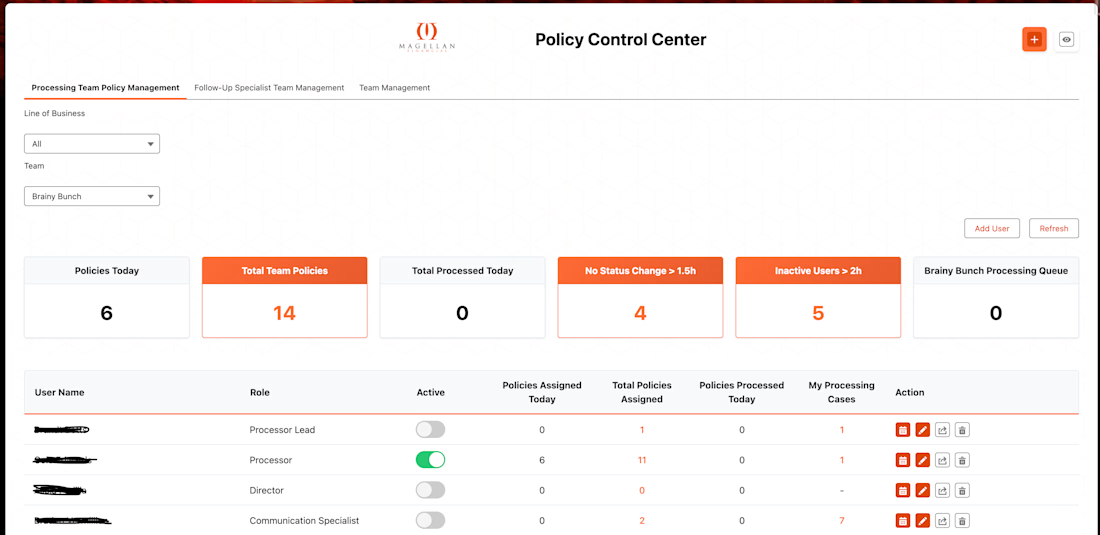
Salesforce Policy Control Center.
Fully integrated team management system with flow round robin distribution system.
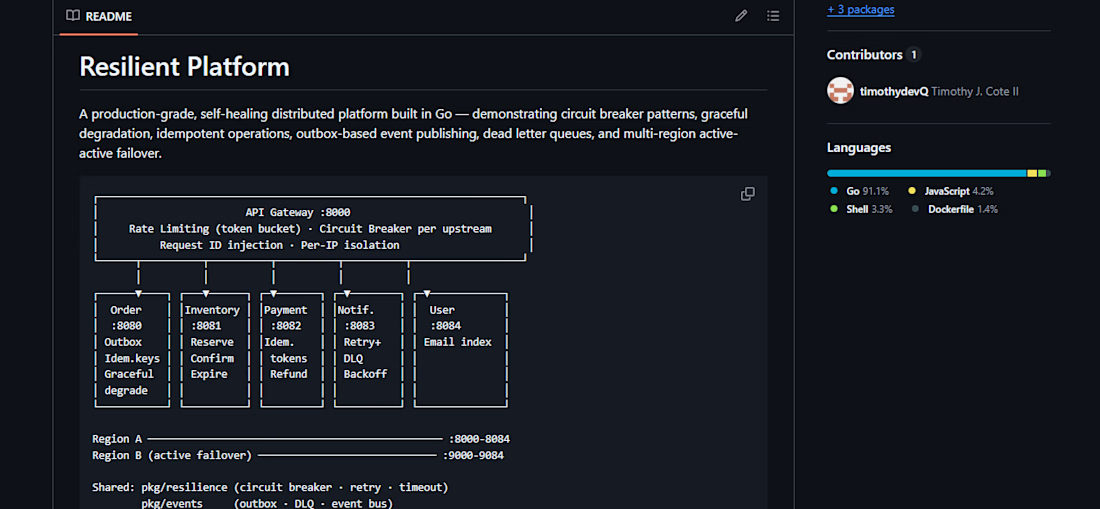
Resilient Platform is a production-grade distributed systems project built in Go that demonstrates fault-tolerant microservice architecture. It includes an API gateway, circuit breakers, rate limiting, request ID injection, graceful degradation, idempotent operations, outbox-based event publishing, dead-letter queues, retry/backoff logic, and active failover across regions. It showcases strong backend engineering skills in reliability, scalability, and resilient service design.
Trending
Claude
Claude has entered the design space. How are you using Claude Design?
Contra University
Learn from expert creatives how to earn more using next-gen AI tools.
creativeaiflow
Creative AI workflows are evolving. What tools do you use, and what are their strengths and weaknesses?
portfolioreview
The best portfolios tell a story, not just show a grid. Share yours for feedback.
freelancerlife
Freelancer life is wins, pivots, and everything in between. What’s yours right now?