The network for creativity
Join 1.25M professional creatives like you
Connect with clients, get discovered, and run your business 100% commission-free
Creatives on Contra have earned over $150M and we are just getting started
Back to feedPost
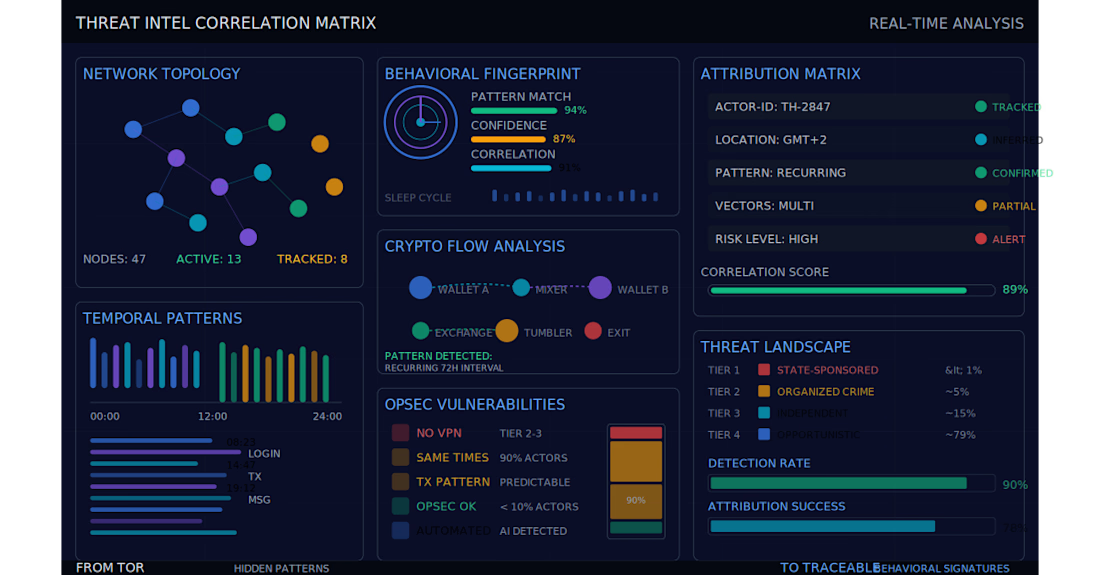
From Tor to Traceable: The Human Vulnerability in OPSEC
After close to two decades monitoring underground ecosystems, I've learned that 90% of threat actors compromise their own anonymity through behavioral patterns—not technical failures.
The problem isn't breaking encryption. It's profiling the human using it.
Temporal pattern analysis, cryptocurrency flow correlation, and behavioral fingerprinting expose more actors than any cryptographic vulnerability.
📄 Full article: on Linkedin
Available for: Threat intelligence consulting, dark web monitoring, adversary behavioral profiling, cryptocurrency crime analysis
#ThreatIntelligence #CTI #DarkWeb #OSINT
The network for creativity
Join 1.25M professional creatives like you
Connect with clients, get discovered, and run your business 100% commission-free
Creatives on Contra have earned over $150M and we are just getting started
Related posts
Nice work!
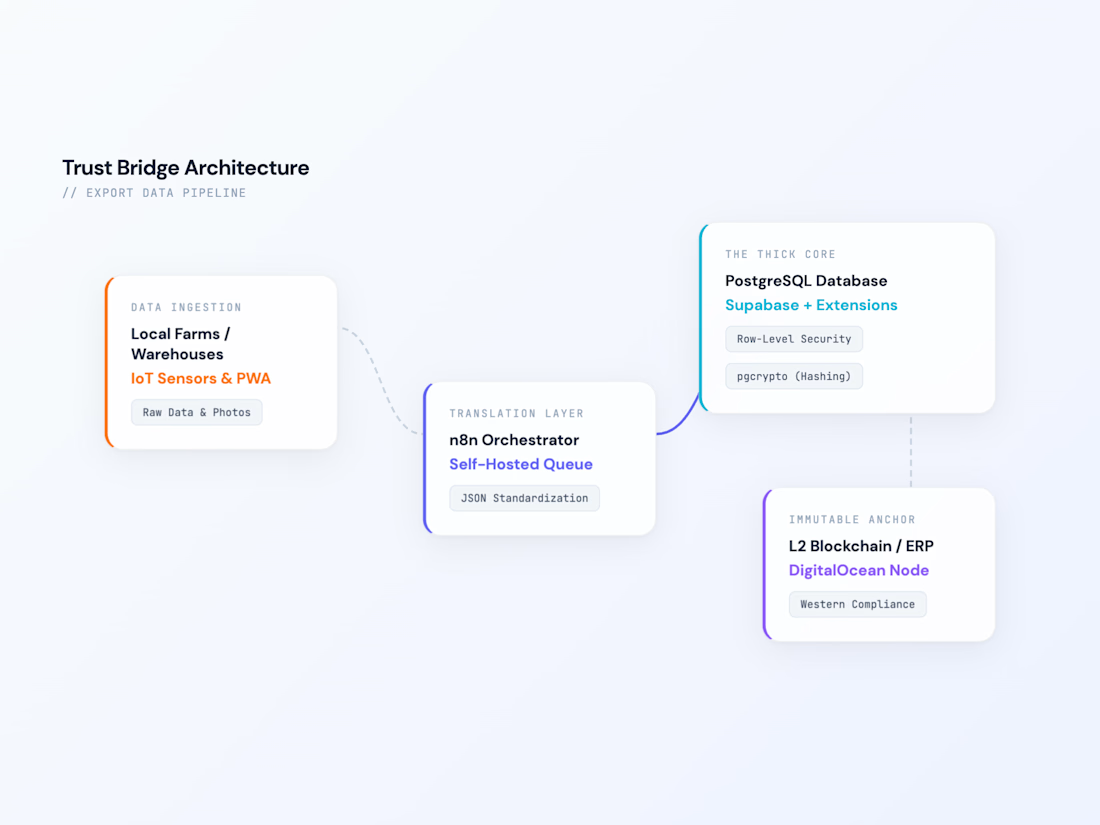
Beautiful UI cannot pass a Compliance Audit. Resilient Architecture does.
In the rush to build fast MVPs, many founders and agencies focus entirely on the frontend, gluing the backend together with fragile No-Code automation tools.
But when you are building B2B platforms in Logistics, FinTech, or HealthTech, a "silent failure" in an API webhook isn't just a bug—it’s a lost contract or a compliance fine.
I just published an engineering deep-dive on Medium covering the "Thick Database" Strategy.
I explore how to encapsulate complex business logic natively inside PostgreSQL (using extensions like pgcrypto for hashing, earthdistance for logistics routing, and pg_partman for heavy IoT logs).
By keeping the compute inside the database and only using orchestration (n8n/Deno) for network I/O, we build systems that are mathematically secure and infinitely scalable.
If you're designing a beautiful product, make sure it has a titanium spine. Read the full blueprint on my Medium.
#SystemsArchitecture #Supabase #BackendEngineering #DatabaseDesign
Trending
Claude
Claude has entered the design space. How are you using Claude Design?
Contra University
Learn from expert creatives how to earn more using next-gen AI tools.
creativeaiflow
Creative AI workflows are evolving. What tools do you use, and what are their strengths and weaknesses?
portfolioreview
The best portfolios tell a story, not just show a grid. Share yours for feedback.
freelancerlife
Freelancer life is wins, pivots, and everything in between. What’s yours right now?