Alex Scheaffer
Senior engineer who fixes, modernizes, streamlines, builds.
New to Contra
Alex is ready for their next project!
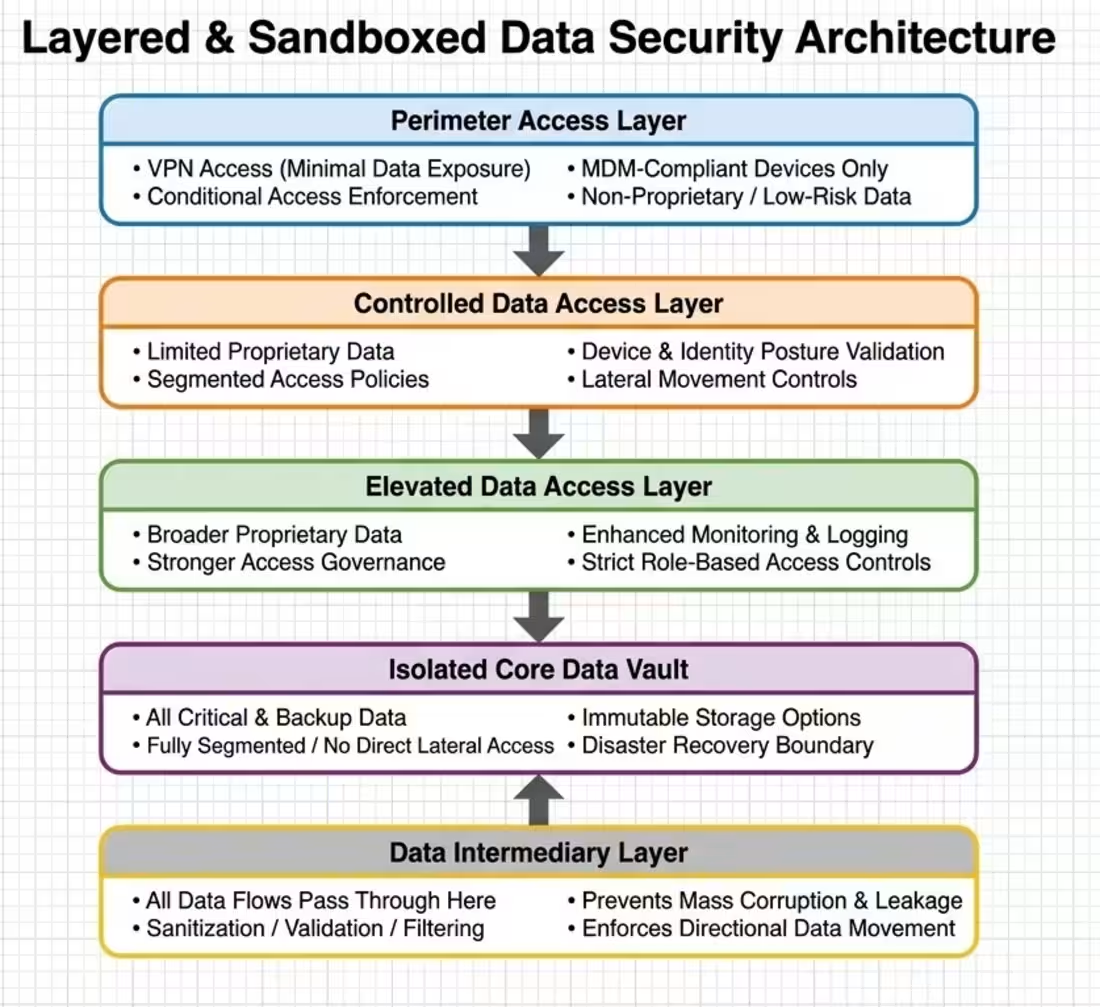
Layered, sandboxed data‑security model that limits exposure, controls data flow, and prevents mass leakage or corruption during an attack.
0
3
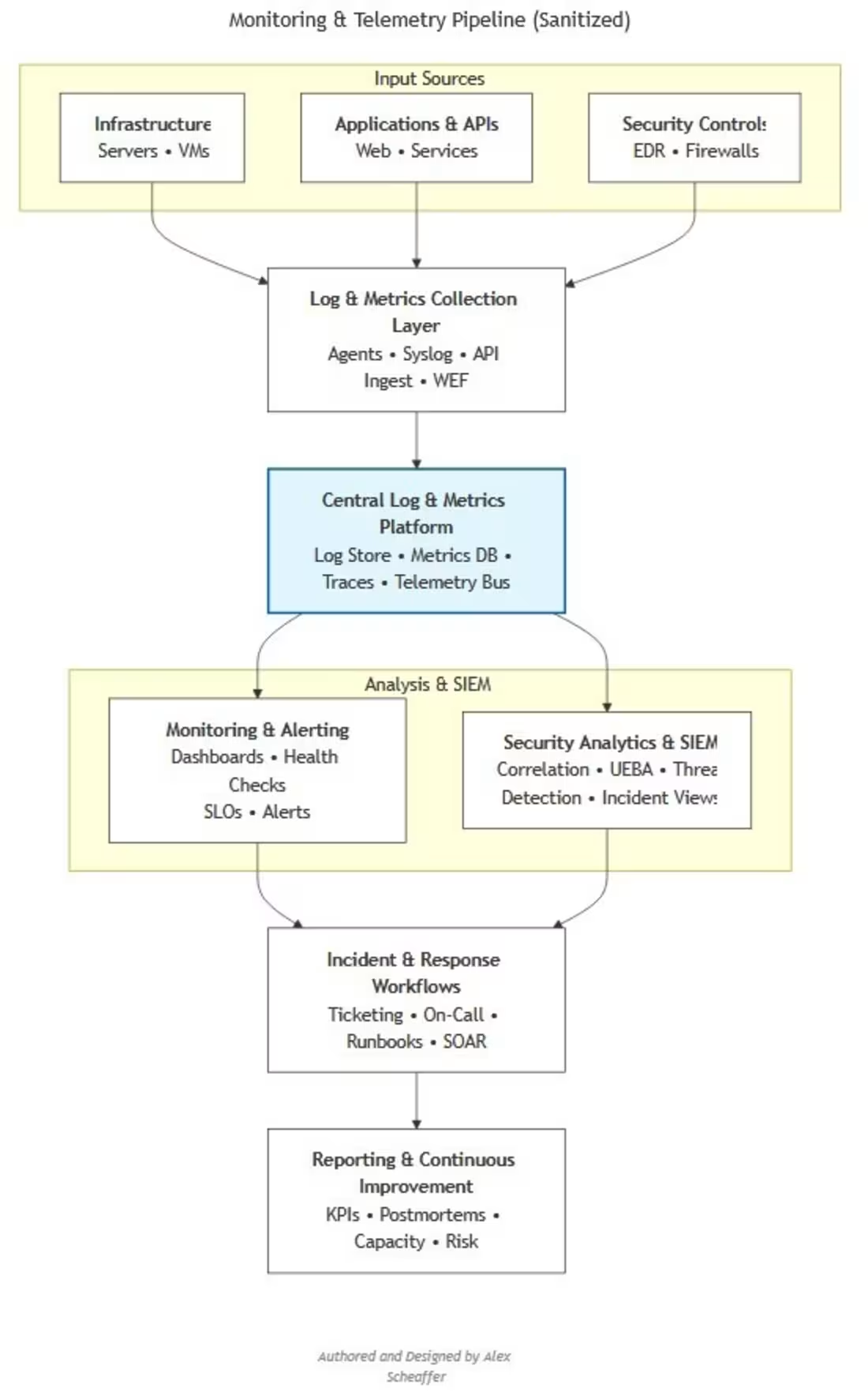
A high‑level view of a unified monitoring and telemetry flow that centralizes logs, metrics, and alerts across hybrid environments. It shows collection, normalization, and routing into observability platforms. This sanitized version removes organization‑specific details. Authored in ASCII, translated into Mermaid syntax, and rendered using Kroki.
0
13
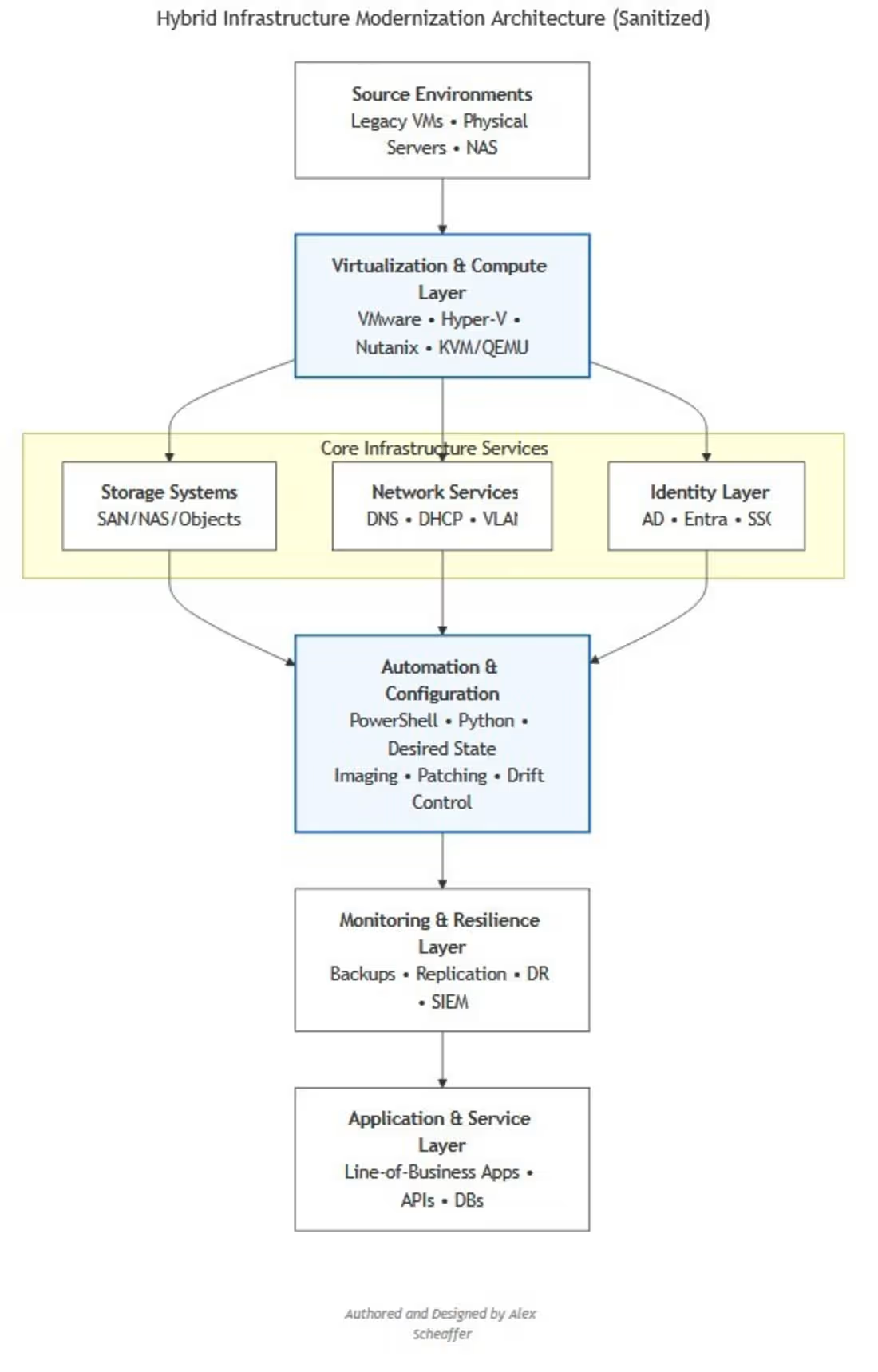
A high‑level view of a modernized hybrid environment focused on identity governance, platform reliability, and secure cloud adoption. This sanitized version removes organization‑specific details. Authored in ASCII, translated into Mermaid syntax, and rendered into a visual diagram using Kroki for clarity and portability.
0
15
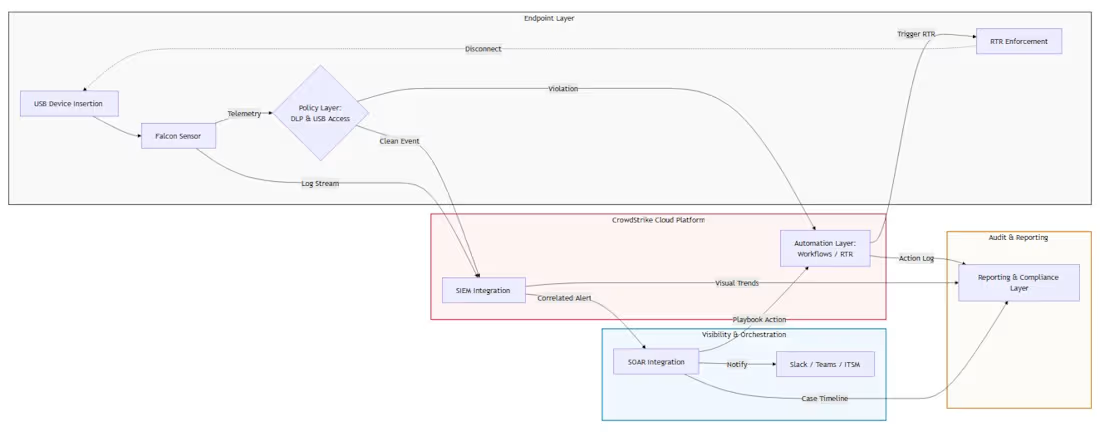
A unified architecture that detects USB mass‑storage events with Falcon Sensor, evaluates DLP and USB Access Conditions, triggers automated RTR enforcement, and streams all activity into SIEM and SOAR for correlation, orchestration, and enterprise‑wide response.
1
27