Securing Cloud Infrastructures Muhammed Ali
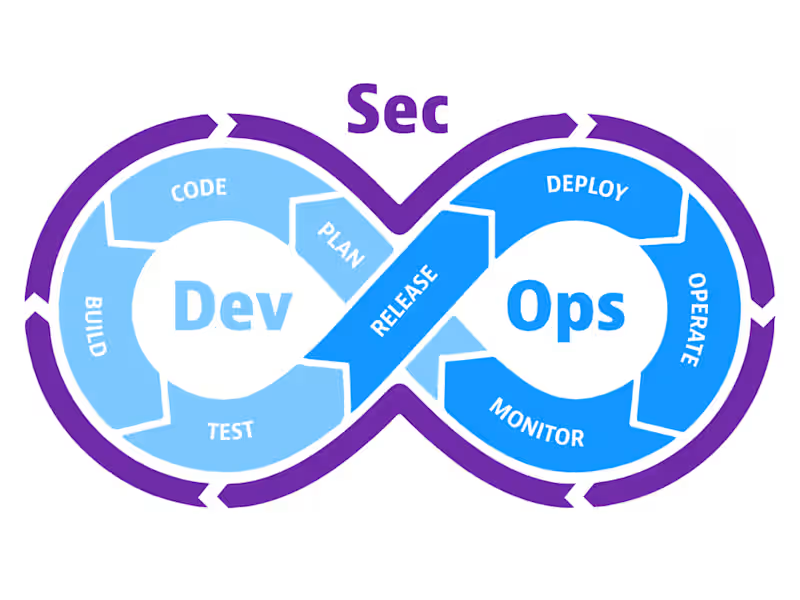
A cloud security project involves assessing and enhancing the security posture of cloud environments by implementing robust security policies, practices, and technologies. This includes securing CI/CD pipelines, managing Identity and Access Management (IAM), configuring encryption for data at rest and in transit, and deploying monitoring and alerting systems to detect and respond to threats. The project ensures compliance with industry standards and regulations such as GDPR, HIPAA, or PCI DSS through audits and control mappings. It leverages tools like Infrastructure-as-Code (IaC) for secure and automated deployments across public, private, and hybrid clouds, embedding security into the entire lifecycle. The goal is to create a resilient, compliant, and scalable cloud infrastructure while fostering a culture of continuous security improvement.
What's included
Cloud Security Assessment Report
- Overview of the cloud environment and architecture.
- Identification of security risks and vulnerabilities (e.g., misconfigured IAM policies, exposed storage buckets).
- Compliance gap analysis (e.g., GDPR, HIPAA, SOC 2).
- Recommendations for mitigating risks and improving the security posture.
- A prioritized action plan for remediation.
Implementing Security Policies and Practices
- Objectives for implementing security policies and practices (e.g., enhancing cloud security, achieving compliance).
- Best practices for IAM configuration (e.g., least privilege, MFA).
- Encryption standards for data at rest and in transit.
- Guidelines for configuring firewalls, security groups, and VPNs.
- List of resources requiring logging (e.g., access logs, API calls).
- Recommendations for periodic review and updates of security policies.
Training Material and Workshops
- Cloud security awareness training materials for different roles (e.g., developers, administrators).
- Hands-on workshops or labs covering secure development practices, threat detection, and response.
- Documentation on using tools and interpreting monitoring dashboards.
Muhammed's other services
Starting at$40 /hr
Tags
AWS
Google Cloud Platform
Jenkins
Kubernetes
Terraform
Cloud Infrastructure Architect
Cloud Security Engineer
Security Engineer
Service provided by
Muhammed Ali Cairo, Egypt
- 1
- Followers

Securing Cloud Infrastructures Muhammed Ali
Starting at$40 /hr
Tags
AWS
Google Cloud Platform
Jenkins
Kubernetes
Terraform
Cloud Infrastructure Architect
Cloud Security Engineer
Security Engineer
A cloud security project involves assessing and enhancing the security posture of cloud environments by implementing robust security policies, practices, and technologies. This includes securing CI/CD pipelines, managing Identity and Access Management (IAM), configuring encryption for data at rest and in transit, and deploying monitoring and alerting systems to detect and respond to threats. The project ensures compliance with industry standards and regulations such as GDPR, HIPAA, or PCI DSS through audits and control mappings. It leverages tools like Infrastructure-as-Code (IaC) for secure and automated deployments across public, private, and hybrid clouds, embedding security into the entire lifecycle. The goal is to create a resilient, compliant, and scalable cloud infrastructure while fostering a culture of continuous security improvement.
What's included
Cloud Security Assessment Report
- Overview of the cloud environment and architecture.
- Identification of security risks and vulnerabilities (e.g., misconfigured IAM policies, exposed storage buckets).
- Compliance gap analysis (e.g., GDPR, HIPAA, SOC 2).
- Recommendations for mitigating risks and improving the security posture.
- A prioritized action plan for remediation.
Implementing Security Policies and Practices
- Objectives for implementing security policies and practices (e.g., enhancing cloud security, achieving compliance).
- Best practices for IAM configuration (e.g., least privilege, MFA).
- Encryption standards for data at rest and in transit.
- Guidelines for configuring firewalls, security groups, and VPNs.
- List of resources requiring logging (e.g., access logs, API calls).
- Recommendations for periodic review and updates of security policies.
Training Material and Workshops
- Cloud security awareness training materials for different roles (e.g., developers, administrators).
- Hands-on workshops or labs covering secure development practices, threat detection, and response.
- Documentation on using tools and interpreting monitoring dashboards.
Muhammed's other services
$40 /hr