The network for creativity
Join 1.25M professional creatives like you
Connect with clients, get discovered, and run your business 100% commission-free
Creatives on Contra have earned over $150M and we are just getting started
Back to feedPost
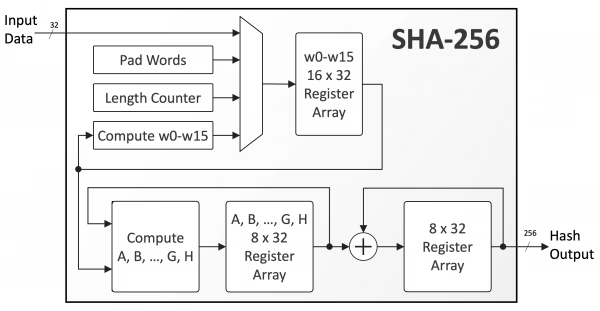
Spent a couple of weeks earlier in the year, learning about the inner workings of the SHA-256 hashing algorithm and how entire files are hashed. Now today, I'm happy to say I've been able to complete a simplified implementation of sha-256 hashing algorithm. If you've seen my previous posts about ROTR, and binary operations, it may now begin to make sense why I've been yapping all the while😅.
Learned a lot on this mini journey, from learning about splitting and padding file chunks, to the Merkle-Damgard compression step, and prime number sieves, it was a pretty fun exercise!!
I made a GitHub gist of my implementation (in python). Feel free to leave a star⭐ https://gist.github.com/Curiouspaul1/92394cc3d58dd2a97ab8389ae8f9915d
[Image source: https://www.cast-inc.com/security/encryption-primitives/sha-256 ]
The network for creativity
Join 1.25M professional creatives like you
Connect with clients, get discovered, and run your business 100% commission-free
Creatives on Contra have earned over $150M and we are just getting started
Trending
aivideo
AI video tools are moving at warp speed. Which ones are you experimenting with?
returntonature
Spring is a reset for creativity. What’s inspiring you outside the screen right now?
aidesignflow
AI tools are redefining design work. What's your current workflow?
freelancerlife
Freelancer life is wins, pivots, and everything in between. What’s yours right now?
allthingsmetal
Metal is having a design moment – from chrome to gates and grates. What designs are you forging?












