The network for creativity
Join 1.25M professional creatives like you
Connect with clients, get discovered, and run your business 100% commission-free
Creatives on Contra have earned over $150M and we are just getting started
Back to feedPost
Recently something interesting happened.
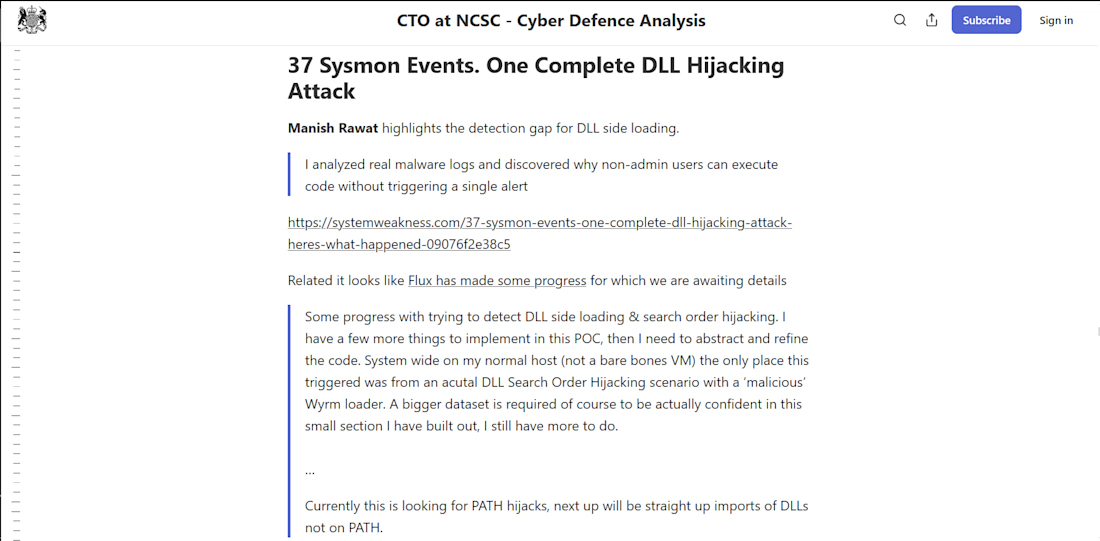
My research on DLL hijacking detection was referenced in work from the National Cyber Security Centre (Cyber Defence Analysis).
The section “37 Sysmon Events. One Complete DLL Hijacking Attack” came from my analysis of malware telemetry showing how code execution occurred without triggering alerts.
To clarify: the detection PoC mentioned later isn’t mine — my contribution focused on identifying the detection gap.
Right now I’m continuing to explore:
• Sysmon event correlation
• Detection blind spots in Windows telemetry
• Why some attacks still bypass common logging assumptions
If you're working on detection engineering, threat hunting, or malware analysis, I’d be happy to exchange ideas.
#threathunting #Malwareanalysis #Medium #Infosec #detectionengineering
The network for creativity
Join 1.25M professional creatives like you
Connect with clients, get discovered, and run your business 100% commission-free
Creatives on Contra have earned over $150M and we are just getting started
Related posts
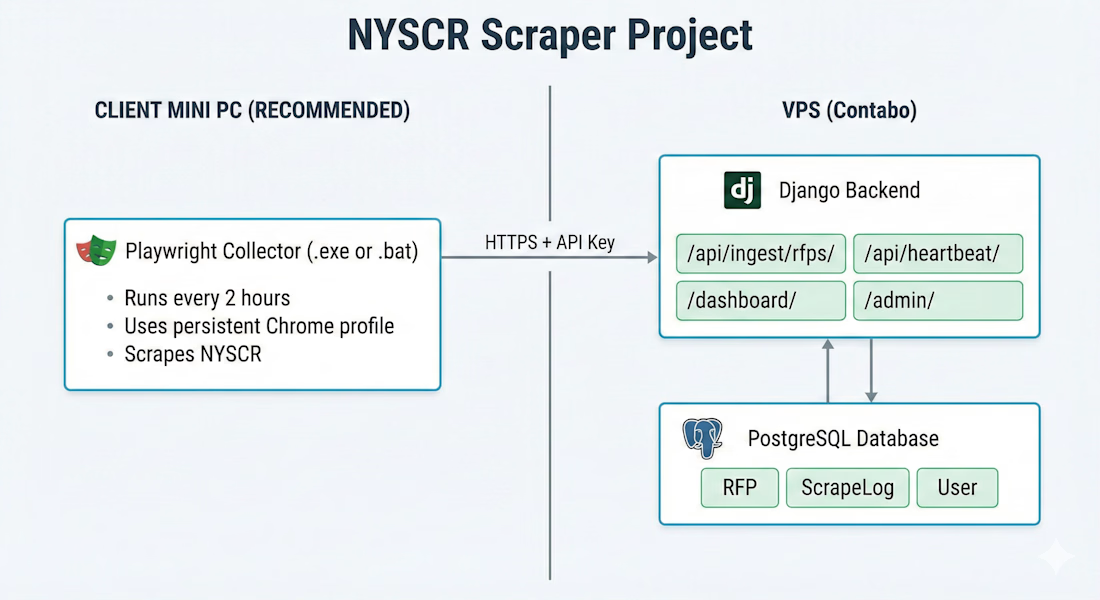
Hybrid RFP Monitoring System: reCAPTCHA v3 Bypass & Django Dashboard
High-Efficiency Hybrid RFP Orchestration
I developed a production-ready system to monitor New York State Contract Reporter (NYSCR) opportunities, overcoming aggressive reCAPTCHA v3 and cloud-blocking.
The Solution:
Hybrid Sync: A local Playwright collector on a Windows environment bypasses bot detection and pushes data via a secure API to the cloud.
Django Dashboard: A centralized VPS-hosted interface for real-time RFP tracking and filtering.
Intelligent Automation: Automated deduplication logic and instant email alerts for critical due date changes.
Resilience: Built-in heartbeat monitoring and automated scrape logs for 99.9% data freshness.
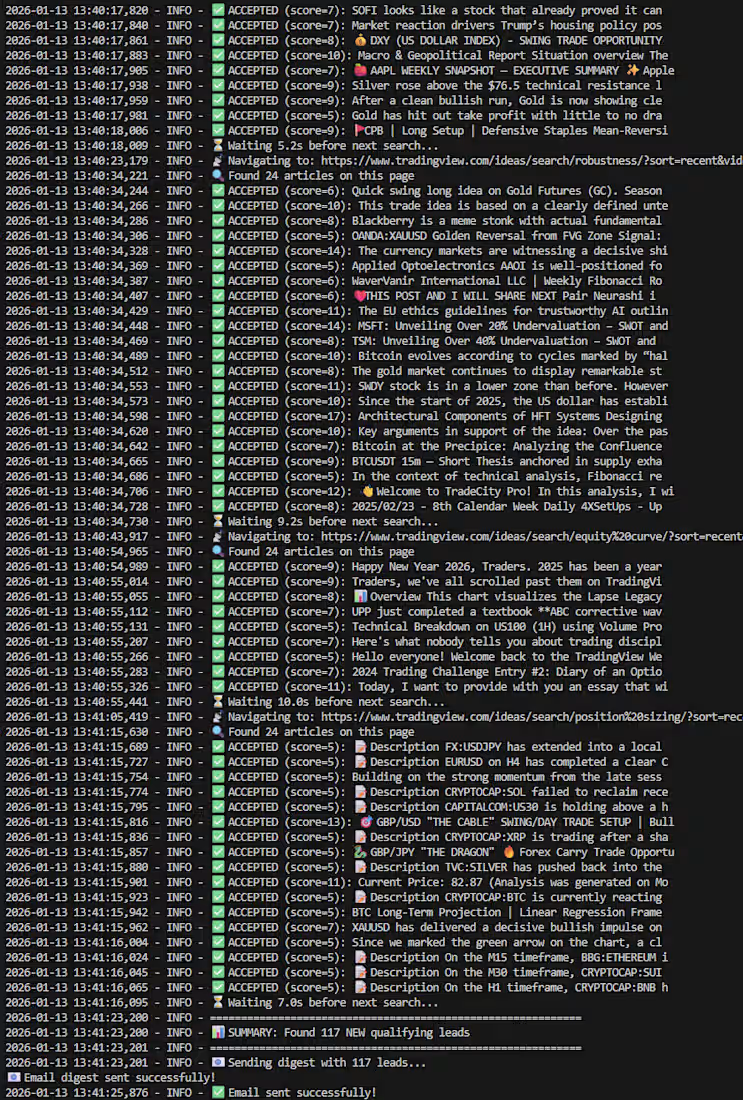
Automated TradingView Strategy Scraper & Scoring Engine
I built a custom "Intelligent Agent" to solve a common problem for traders: filtering through thousands of low-quality posts to find robust trading strategies.
Intelligent Agent for Trading Strategy Discovery
I built a custom Intelligent Agent to solve a common problem for traders: filtering through thousands of low-quality posts to find robust trading strategies.
The Challenge
TradingView is flooded with spam and low-effort posts. Manually checking them takes hours every day.
The Solution
I developed a Python-based automation bot that autonomously monitors the platform. It doesn’t just scrape data — it analyzes it.
Key Features
🕵️ Stealth Scraping
Built with Playwright (Async) and stealth libraries
Bypasses anti-bot detection and Cloudflare protection
🧠 Heuristic Scoring Engine
Reads post descriptions and assigns a Quality Score
Rewards professional keywords (e.g., Walk-Forward, Backtest)
Penalizes spam signals (e.g., 100% Win Rate)
🗃️ Data Deduplication
Uses a local SQLite database
Ensures the client never receives duplicate alerts
📧 Automated Reporting
High-scoring strategies are compiled into a clean digest
Delivered instantly via email notifications
The Result
The system runs 24/7 on a VPS, saving the client 10+ hours of research time per week by delivering only high-value trading strategy leads.
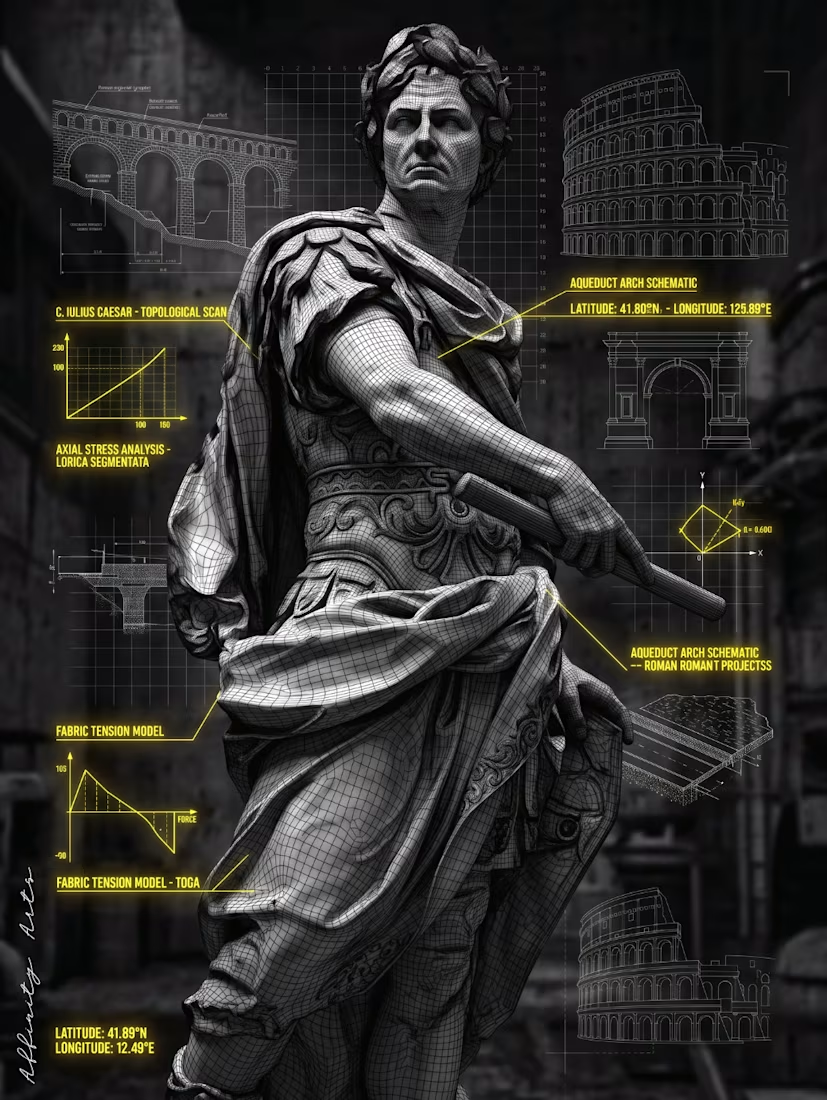
"Caesar Topological Scan" — Decoded Icons Series
C. Iulius Caesar submitted to full engineering analysis. Lorica Segmentata stress-tested, toga fabric tension modelled, aqueduct arch schematics filed alongside the Colosseum coordinates. The man who built an empire gets the blueprint treatment — every fold of cloth, every conquest reduced to data points and vectors.
Awesome!
Trending
Claude
Claude has entered the design space. How are you using Claude Design?
Contra University
Learn from expert creatives how to earn more using next-gen AI tools.
creativeaiflow
Creative AI workflows are evolving. What tools do you use, and what are their strengths and weaknesses?
portfolioreview
The best portfolios tell a story, not just show a grid. Share yours for feedback.
freelancerlife
Freelancer life is wins, pivots, and everything in between. What’s yours right now?