The network for creativity
Join 1.25M professional creatives like you
Connect with clients, get discovered, and run your business 100% commission-free
Creatives on Contra have earned over $150M and we are just getting started
Back to feedPost
Excited to share some of the backend work I've been doing lately with Supabase! 🚀
Here's a look at what went into building a production-ready backend from scratch:
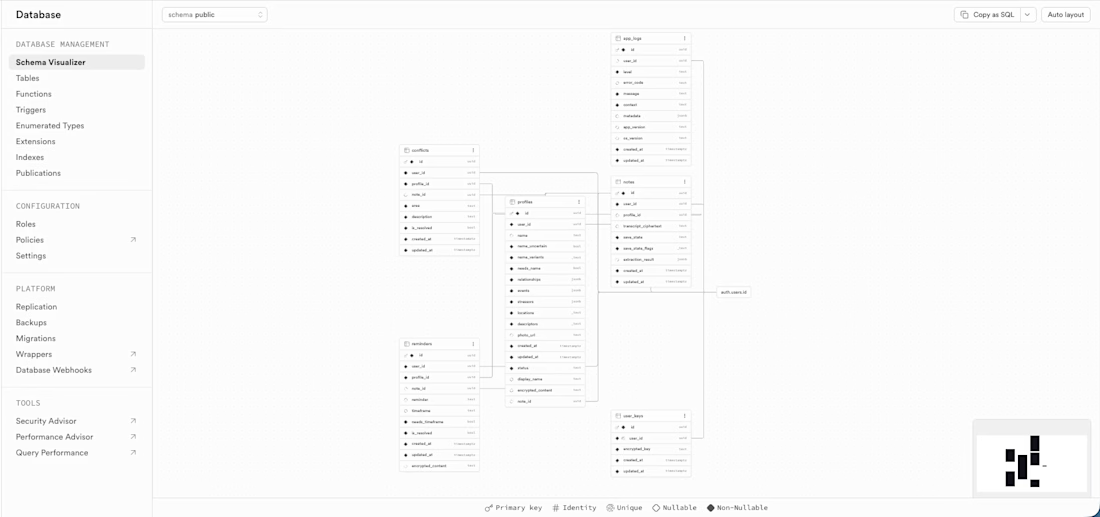
🗄️ Database Schema Design
Designed a relational schema with multiple interconnected tables: profiles, notes, reminders, conflicts, and a dedicated user_keys table for encryption key management. Every table has proper foreign key relationships, timestamps, and nullable/non-nullable constraints enforced at the DB level.
🔒 Row Level Security (RLS)
Every single table has RLS enabled with two policies: users can only access their own rows, and anonymous access is blocked entirely. No exceptions. Security is enforced at the database layer, not just the application layer.
🔑 Auth & Email Flows
Set up Supabase Auth with email + OAuth support, including full PKCE flow for secure token exchange. Configured deep link redirects for email confirmation and password reset flows, all tested end to end.
⚡ Edge Functions
Built and deployed multiple Supabase Edge Functions handling AI processing pipelines, including JWT validation at the top of every function before any processing begins. The OpenAI API key lives exclusively in Supabase secrets, never in the app or any config file.
🔄 Merge Pipeline
Built a follow-up note merge pipeline as an Edge Function. New facts are appended to existing profiles, duplicates are detected and skipped, conflicts are logged, and resolved reminders are handled gracefully.
📦 Migrations
All schema changes go through versioned migration files under source control. No manual dashboard changes. CI/CD triggers migrations automatically on merge to main.
🔐 Encryption Architecture
Client-side AES-GCM encryption via CryptoKit. Plaintext never sits in the database. Encryption keys are stored in a dedicated RLS-scoped table, fetched after login, and held in memory only for the session duration.
Still a lot more to share about this project. Excited to talk about it publicly when it launches! 👀
Interesting work! Nice 🔥 Have there been any bottlenecks so far in testing?
Thank you! so far no bottlenecks, Supabase very smooth, you can easily verify how data stored from website or Postgres and for the edge functions with postman.
Yeah good choice using Supabase. It's the standard
The network for creativity
Join 1.25M professional creatives like you
Connect with clients, get discovered, and run your business 100% commission-free
Creatives on Contra have earned over $150M and we are just getting started
Related posts
Recently worked on BES Vinyl - a large-scale ecommerce infrastructure project built around Shopify, FileMaker Server, and AWS to support a rapidly growing online vinyl record business.
The project involved restoring and stabilizing a mission-critical FileMaker PIM system, rebuilding backend workflows, and implementing automated API-driven synchronization between Shopify and the internal product database for inventory, pricing, metadata, supplier imports, and catalog management.
Beyond the storefront experience, the real focus was operational scalability - reducing manual processes, improving data reliability, and creating a centralized commerce ecosystem capable of handling large product volumes efficiently.
Projects like this are where ecommerce, automation, and systems architecture come together to create measurable business impact. 🚀
Everything feels balanced, refined, and professionally designed 💯
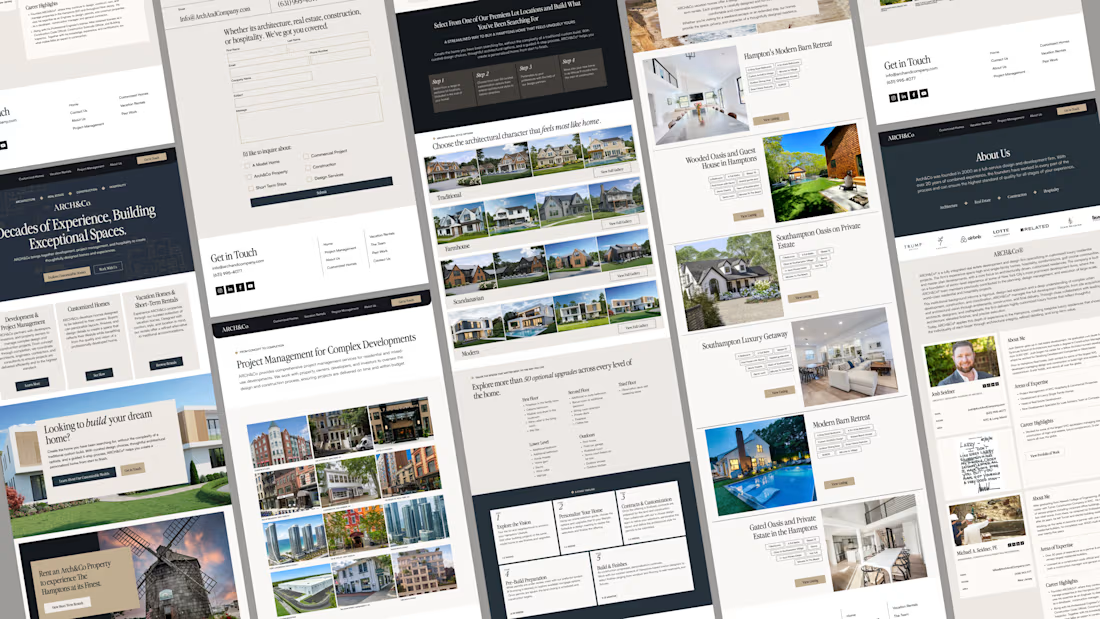
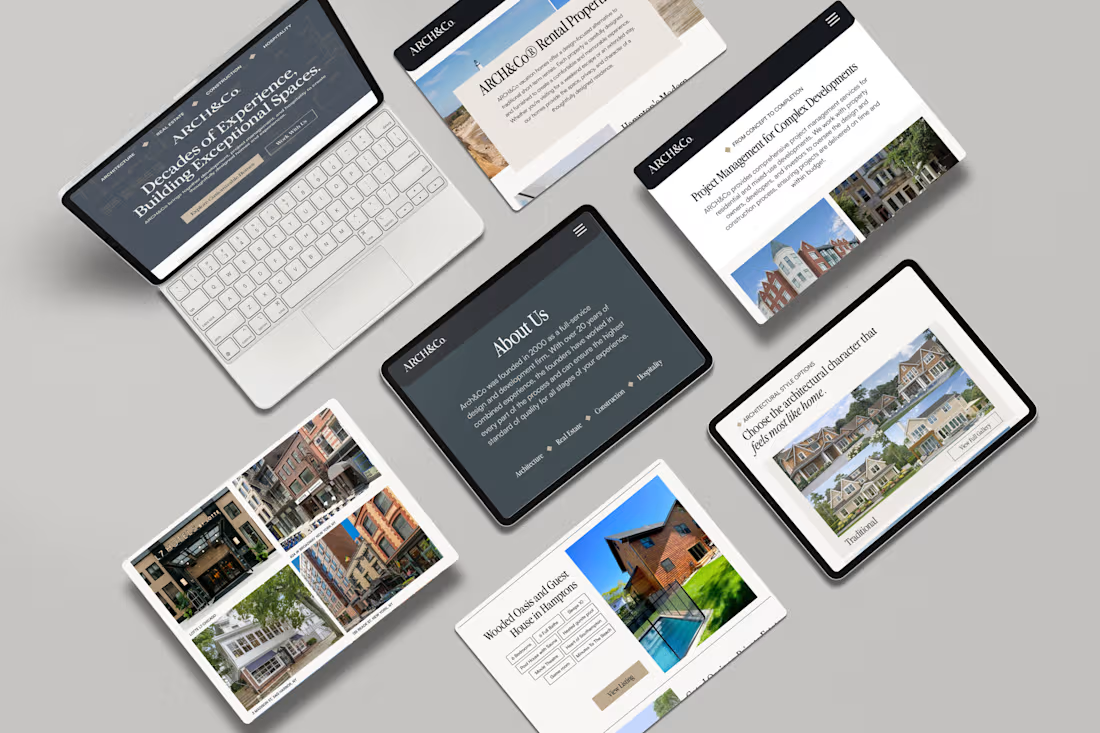
I had a great time working on this super clean, modern & sophisticated web design and development project with an old friend. Designed in Figma , Built in Webflow.

Creative 😍
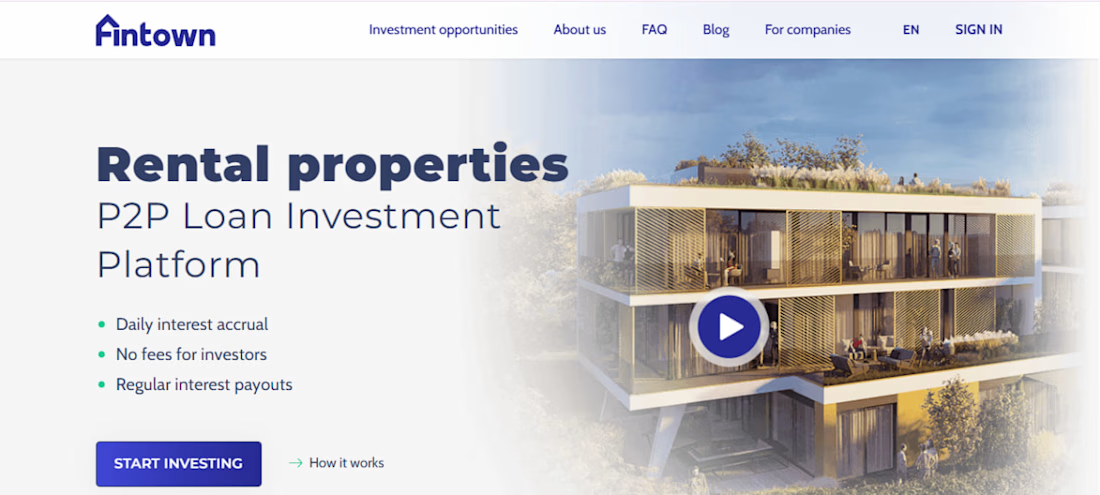
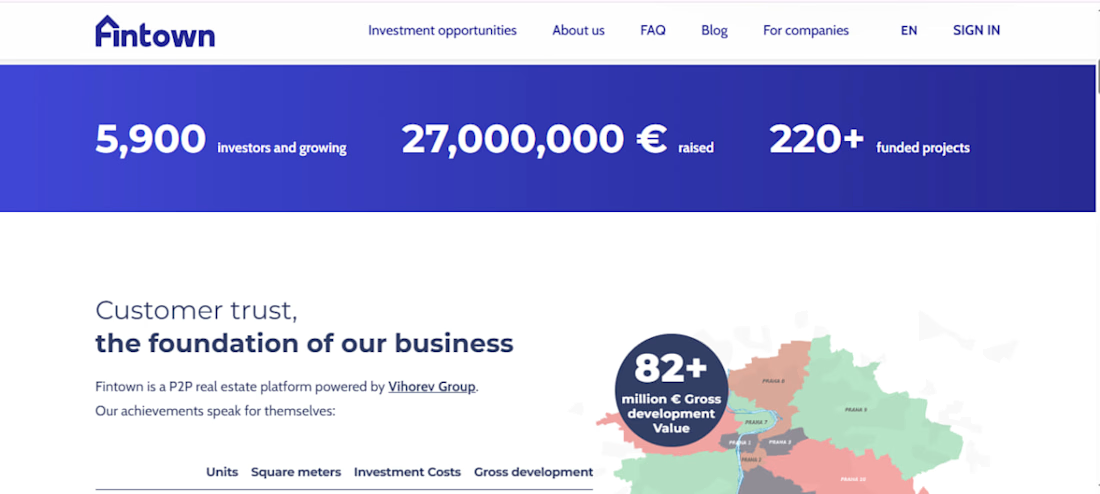
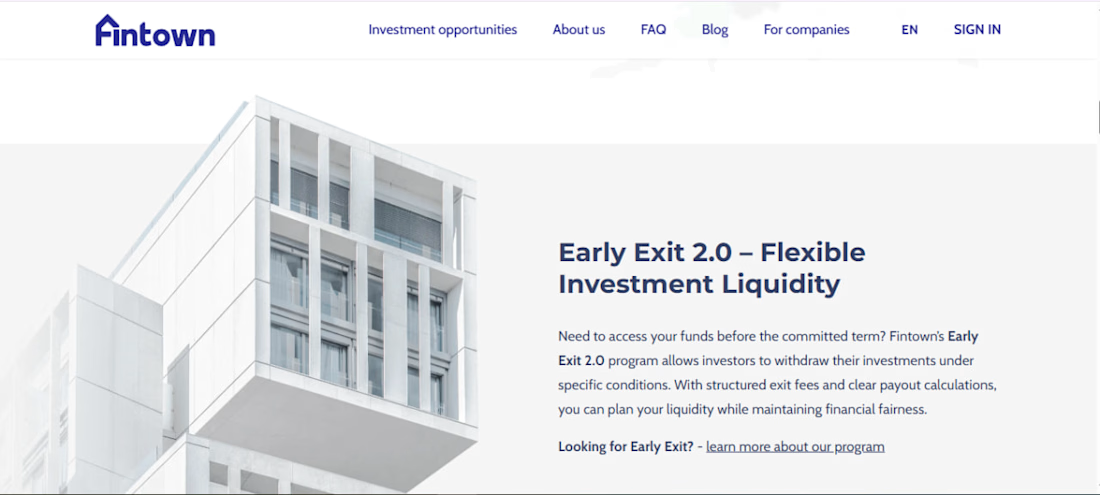
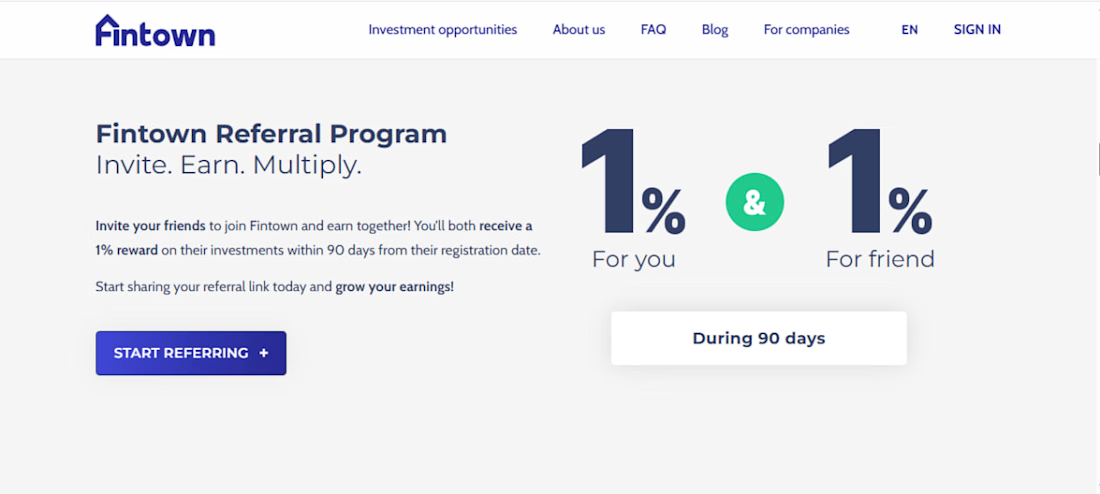
P2P Real Estate Investment Platform
Fintown is a European P2P real estate investment platform that allows investors to explore rental and development projects, invest online, track opportunities, and receive regular interest payouts through a modern digital platform.
I worked on this project as a Full Stack / Frontend Developer, focusing on building a clean, responsive, and user-friendly web experience for investors and real estate developers. The platform needed to present investment opportunities clearly, support smooth user navigation, and provide a professional interface for users who want to review projects, understand returns, and manage investment-related actions.
The main goal of the project was to create a trustworthy and easy-to-use investment platform where users can quickly understand available opportunities, review project details, calculate potential returns, register or sign in, and move through the investment flow with confidence.
My responsibilities included frontend development, responsive UI implementation, API integration, reusable component development, performance improvements, and production-level bug fixing. I also worked on improving page structure, user flows, layout consistency, and cross-browser compatibility.
Trending
Claude
Claude has entered the design space. How are you using Claude Design?
Contra University
Learn from expert creatives how to earn more using next-gen AI tools.
creativeaiflow
Creative AI workflows are evolving. What tools do you use, and what are their strengths and weaknesses?
portfolioreview
The best portfolios tell a story, not just show a grid. Share yours for feedback.
freelancerlife
Freelancer life is wins, pivots, and everything in between. What’s yours right now?