🛡️ Cloud Security Hardening & Zero-Trust Infrastructure Audit.Thiago Nazario
Expert Linux Hardening and Cloud Security Engineer focused on the Principle of Least Privilege.
I eliminate vulnerabilities and 'Permission Denied' errors through automated, security-first infrastructure practices.
What's included
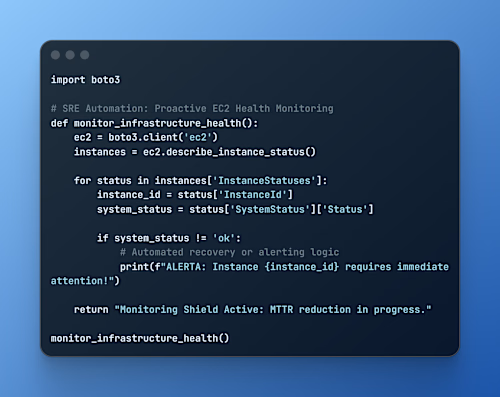
Comprehensive Infrastructure Security Audit
A deep-dive report identifying vulnerabilities, misconfigured permissions, and potential entry points within your cloud or server environment.
Zero-Trust IAM & Access Implementation
Full reconfiguration of users, roles, and policies following the "Principle of Least Privilege" to ensure maximum access control.
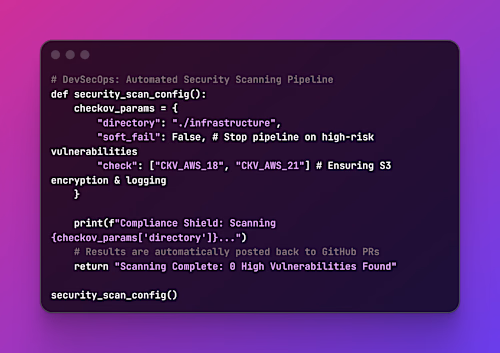
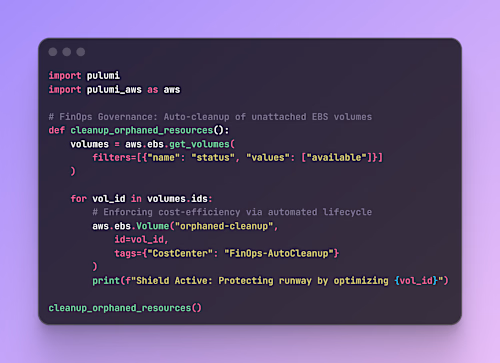
Security-First IaC Scripts (Terraform/Pulumi)
Hardened Infrastructure as Code templates including optimized Firewalls, VPCs, and Security Groups, ready for automated deployment.
Encryption & Compliance Documentation
Technical documentation detailing the security standards applied (at-rest/in-transit encryption) and guidelines for maintaining a compliant environment.
Security Posture Handover & Roadmap
A final technical briefing (delivered asynchronously) with recommendations for future security scaling as your business grows.
FAQs
Example work

🛡️ Cloud Security Hardening & Zero-Trust Infrastructure Audit.Thiago Nazario
Starting at$400
Duration1 week
Expert Linux Hardening and Cloud Security Engineer focused on the Principle of Least Privilege.
I eliminate vulnerabilities and 'Permission Denied' errors through automated, security-first infrastructure practices.
What's included
Comprehensive Infrastructure Security Audit
A deep-dive report identifying vulnerabilities, misconfigured permissions, and potential entry points within your cloud or server environment.
Zero-Trust IAM & Access Implementation
Full reconfiguration of users, roles, and policies following the "Principle of Least Privilege" to ensure maximum access control.
Security-First IaC Scripts (Terraform/Pulumi)
Hardened Infrastructure as Code templates including optimized Firewalls, VPCs, and Security Groups, ready for automated deployment.
Encryption & Compliance Documentation
Technical documentation detailing the security standards applied (at-rest/in-transit encryption) and guidelines for maintaining a compliant environment.
Security Posture Handover & Roadmap
A final technical briefing (delivered asynchronously) with recommendations for future security scaling as your business grows.
FAQs
Example work
$400