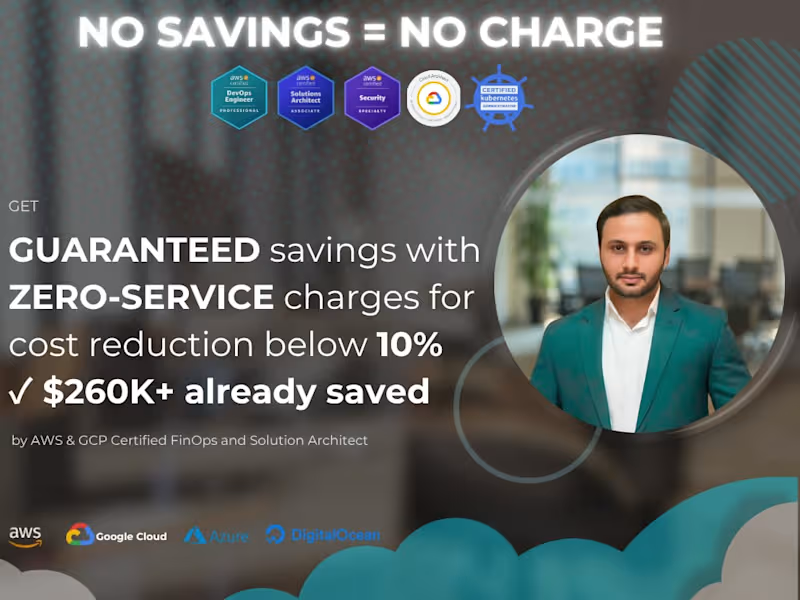
SOC2 & HIPAA Compliance AWS & GCP CloudIslam Ali
𝗦𝘁𝗿𝘂𝗴𝗴𝗹𝗶𝗻𝗴 𝘄𝗶𝘁𝗵 𝗰𝗹𝗼𝘂𝗱 𝘀𝗲𝗰𝘂𝗿𝗶𝘁𝘆 𝗮𝗻𝗱 𝗱𝗮𝘁𝗮 𝗽𝗿𝗶𝘃𝗮𝗰𝘆?
Whether you're in fintech, healthcare, or building a SaaS platform, your AWS or GCP infrastructure must be secure, auditable, and compliant with SOC2 or HIPAA.
As a 𝗖𝗲𝗿𝘁𝗶𝗳𝗶𝗲𝗱 𝗦𝗲𝗰𝘂𝗿𝗶𝘁𝘆 𝗦𝗽𝗲𝗰𝗶𝗮𝗹𝗶𝘀𝘁 and 𝗗𝗲𝘃𝗢𝗽𝘀 𝗘𝗻𝗴𝗶𝗻𝗲𝗲𝗿, I've secured environments supporting millions of users and assisted clients in passing multiple SOC2 audits.
𝗪𝗵𝘆 𝗪𝗼𝗿𝗸 𝗪𝗶𝘁𝗵 𝗠𝗲?
✅ 𝗔𝗪𝗦-𝗰𝗲𝗿𝘁𝗶𝗳𝗶𝗲𝗱 𝗦𝗘𝗖𝗨𝗥𝗜𝗧𝗬 𝗦𝗣𝗘𝗖𝗜𝗔𝗟𝗜𝗦𝗧 with 7+ years of enterprise experience, not a traditional freelancer.
✅ TEXAS-based LLC for compliance requirements.
✅ Proven track record of achieving SOC2 compliance for 𝗘𝗭𝗢 and 𝗤𝘂𝗶𝗰𝗸 𝗤𝘂𝗮𝗰𝗸 𝗖𝗮𝗿 𝗪𝗮𝘀𝗵.
🔐 𝗖𝗹𝗼𝘂𝗱 𝗦𝗲𝗰𝘂𝗿𝗶𝘁𝘆:
• IAM hardening and least privilege with zero-trust architecture implementation.
• Data encryption at rest and in transit.
• Security monitoring with GuardDuty, Security Hub, and GCP Security Command Center.
• Logging with CloudTrail, Config, audit logs, and centralized log storage.
• Vulnerability management and automated patching.
🚀 Let's connect to secure your cloud infrastructure!
What's included
PDF report
summarizing findings with a prioritized remediation plan (impact/effort/owner).
IAM Credential Report
review of root MFA, access key status, stale users.
Architecture notes/diagram
Design diagram for current setup along with any recommendations aligned with AWS/GCP well-architecture framework.
Contact for pricing
Tags
AWS
Azure
Google Cloud Platform
Kubernetes
Terraform
Cloud Security Engineer
Security Engineer
Security Manager
Service provided by
Islam Ali Lahore, Pakistan
SOC2 & HIPAA Compliance AWS & GCP CloudIslam Ali
Contact for pricing
Tags
AWS
Azure
Google Cloud Platform
Kubernetes
Terraform
Cloud Security Engineer
Security Engineer
Security Manager
𝗦𝘁𝗿𝘂𝗴𝗴𝗹𝗶𝗻𝗴 𝘄𝗶𝘁𝗵 𝗰𝗹𝗼𝘂𝗱 𝘀𝗲𝗰𝘂𝗿𝗶𝘁𝘆 𝗮𝗻𝗱 𝗱𝗮𝘁𝗮 𝗽𝗿𝗶𝘃𝗮𝗰𝘆?
Whether you're in fintech, healthcare, or building a SaaS platform, your AWS or GCP infrastructure must be secure, auditable, and compliant with SOC2 or HIPAA.
As a 𝗖𝗲𝗿𝘁𝗶𝗳𝗶𝗲𝗱 𝗦𝗲𝗰𝘂𝗿𝗶𝘁𝘆 𝗦𝗽𝗲𝗰𝗶𝗮𝗹𝗶𝘀𝘁 and 𝗗𝗲𝘃𝗢𝗽𝘀 𝗘𝗻𝗴𝗶𝗻𝗲𝗲𝗿, I've secured environments supporting millions of users and assisted clients in passing multiple SOC2 audits.
𝗪𝗵𝘆 𝗪𝗼𝗿𝗸 𝗪𝗶𝘁𝗵 𝗠𝗲?
✅ 𝗔𝗪𝗦-𝗰𝗲𝗿𝘁𝗶𝗳𝗶𝗲𝗱 𝗦𝗘𝗖𝗨𝗥𝗜𝗧𝗬 𝗦𝗣𝗘𝗖𝗜𝗔𝗟𝗜𝗦𝗧 with 7+ years of enterprise experience, not a traditional freelancer.
✅ TEXAS-based LLC for compliance requirements.
✅ Proven track record of achieving SOC2 compliance for 𝗘𝗭𝗢 and 𝗤𝘂𝗶𝗰𝗸 𝗤𝘂𝗮𝗰𝗸 𝗖𝗮𝗿 𝗪𝗮𝘀𝗵.
🔐 𝗖𝗹𝗼𝘂𝗱 𝗦𝗲𝗰𝘂𝗿𝗶𝘁𝘆:
• IAM hardening and least privilege with zero-trust architecture implementation.
• Data encryption at rest and in transit.
• Security monitoring with GuardDuty, Security Hub, and GCP Security Command Center.
• Logging with CloudTrail, Config, audit logs, and centralized log storage.
• Vulnerability management and automated patching.
🚀 Let's connect to secure your cloud infrastructure!
What's included
PDF report
summarizing findings with a prioritized remediation plan (impact/effort/owner).
IAM Credential Report
review of root MFA, access key status, stale users.
Architecture notes/diagram
Design diagram for current setup along with any recommendations aligned with AWS/GCP well-architecture framework.
Contact for pricing